What is the 11th dimension in M-theory?
The 11th dimension is a characteristic of spacetime that has been proposed as a possible answer to questions that arise in superstring theory. It unifies these theories into a potential single theory of everything.
The theory of superstrings involves the existence of nine dimensions of space and one dimension of time for a total of 10 dimensions. Over the years, multiple variants of string theory have emerged, all attempting to provide a theory of everything that explains how the universe works, with the goal of uniting general relativity and quantum mechanics. Of these variants, five theories are considered the most viable.
All five variants demonstrate mathematical consistency. However, they look different from each other and exhibit different characteristics, to the point of seeming contradictory in places. More importantly, each one offers only a partial glimpse into how everything works. To address these limitations, M-theory emerged, tying together the five string variants and introducing the concept of an 11th dimension to unify these five potential solutions.
The 11th dimension is a mathematical concept. In this context, dimension is best understood as an additional variable added to a math equation to make it solvable. It is not equivalent to the dimensions of space as we understand them in daily usage.
What is superstring theory?
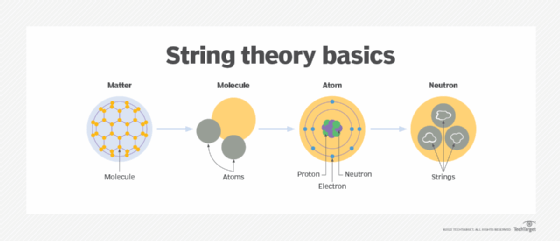
According to string theory, all the elementary particles in the universe are vibrating, one-dimensional filaments of energy known as strings. Strings have no width or height, but they do have length, which is estimated to be 10-35 meters -- many times smaller than the diameter of an atom's nucleus.
Every subatomic particle is a vibrating string, according to string theory. The string's movement determines the type of particle and its characteristics, whether a photon, electron, graviton or other type of particle. In this respect, a string acts much like a violin string whose vibrations determine the note and tone.
The concept of supersymmetry postulates that for each particle there is an associated anti-particle. Supersymmetric string theory is shortened to superstring theory.
String theory is only a mathematical model and still lacks concrete experimental evidence to prove its accuracy. Even so, the model provides an elegant description of the fundamental components that make up the universe. It also predicts the existence of 10 dimensions that the strings can vibrate in, rather than four.
Prior to the introduction of string theory, it was generally believed that we lived in a universe with four dimensions -- three spatial and one temporal.
- First dimension. Linear dimension that has length, but no width or height. This dimension is typically represented as a line that connects two points.
- Second dimension. Flat dimension that has length and width to create a defined area, but no height, much like a sheet of paper or computer display.
- Third dimension. Dimension in which we experience the world around us, with length, width and height. Three-dimensional objects -- such as cubes or spheres -- contain volume.
- Fourth dimension. Time dimension that extends the three-dimensional world by incorporating events that enable three-dimensional objects to move forward and change. The concept of a fourth dimension plays a key role in the general theory of relativity.
String theory introduces six more dimensions that are "curled up" or "compactified" into very small spaces. The six dimensions can be perceived only by the strings and are otherwise undetectable, but their configurations play a pivotal role in determining the properties of subatomic particles. They also provide the conceptual underpinnings needed by the five primary variants of string theory to make the mathematics work. Yet even with 10 dimensions, the variants still fall short in the quest for a theory of everything.
What is M-theory?
M-theory attempts to address these limitations by adding an 11th dimension, along with the concept of membrane, or brane. Like the string, a brane is theorized to be a universal building block that provides the foundation of all matter. However, unlike the original strings, branes add dimensionality, making them more flexible than strings alone. For example, a universe with 11 dimensions can support one-dimensional strings (1-brane), two-dimensional planes (2-branes) and perhaps other dimensional branes.
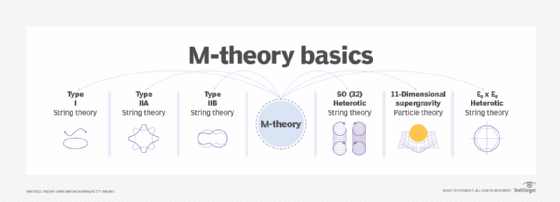
This added dimensionality requires an 11th dimension to make it mathematically feasible. The new dimension and its accompanying branes also resolve the limitations of the five string theory variants. Rather than treating them as conflicting theories, the 11th dimension makes it possible to see them as different aspects of a much larger whole, each viewing the universe from its own perspective. Furthermore, M-theory, with its 11 dimensions and collection of branes, offers a viable mathematical theory of everything, unlike its string predecessors. Nevertheless, as with string theory, M-theory still lacks concrete experimental evidence to move it beyond equations.
What are the 11 dimensions?
In M-theory, the various dimensions are best understood as the number of variables in an equation, and not the same as the dimensions of spacetime we are familiar with -- namely height, width, length and time.
To help understand this, imagine trying to fully describe an airplane moving through a three-dimensional space. You would need four variables to fully describe it: the yaw, pitch, roll and magnitude. These four numbers are known as quaternions. Quaternions are common in computing, where they are used to compute things like 3D graphics or the motions of spacecraft. Now add in time, and you are using five variables to fully describe a point in four-dimensional spacetime.
In string theory, eight variables known as octonions are used to describe the one-dimensional strings. Octonions can be operated on using algebra the same way as quaternions and imaginary numbers can. With it, all interactions of the strings, understood as forces and particles, can be calculated using octonion multiplication in the same numerical space.
Imagine a piece of string being moved; the path it takes describes a two-dimensional plane. This is what happens when time is added to the one-dimensional strings operating in eight-dimensional space. The two-dimensional path is what is called a brane. This adds two additional dimensions to our equation -- one of time and one to describe the brane. This brings the total number of variables, or dimensions, to 10.
As discussed earlier, using 10-dimensional string theory resulted in five separate systems that are all mathematically consistent within themselves, but contradict each other. By adding in an additional variable, or dimension for the brane to move through, these five systems can be made consistent with each other.
This gives us the total number of 11 dimensions.
Learn about the scientific method, empirical analysis and falsifiability, as well as the concept of absolute truth and its application in science, philosophy and mathematics.