bitcoin mining
What is bitcoin mining?
Bitcoin mining is a type of cryptomining in which new bitcoin are entered into circulation and bitcoin transactions are verified and added to the blockchain. Bitcoin, often abbreviated as BTC, is a cryptocurrency that's traded for goods or services as payment. Bitcoin mining is done to record current bitcoin transactions in blocks, which are then added to a blockchain -- the public, decentralized record of past transactions.
Bitcoin miners use software to solve transaction-related algorithms that check bitcoin transactions. In return, miners are awarded a certain number of bitcoin per block. This encourages them to keep solving the transaction-related algorithms, supporting the overall system.
About 90% of the 21 million bitcoin cap has been mined, and it's predicted that the last bitcoin under that cap will be mined by 2140. Bitcoin miners often range from individual enthusiasts and pools to large-scale mining farms and institutions. Mining operations are typically costly, which makes it less practical for the average consumer to perform.
How does bitcoin mining work?
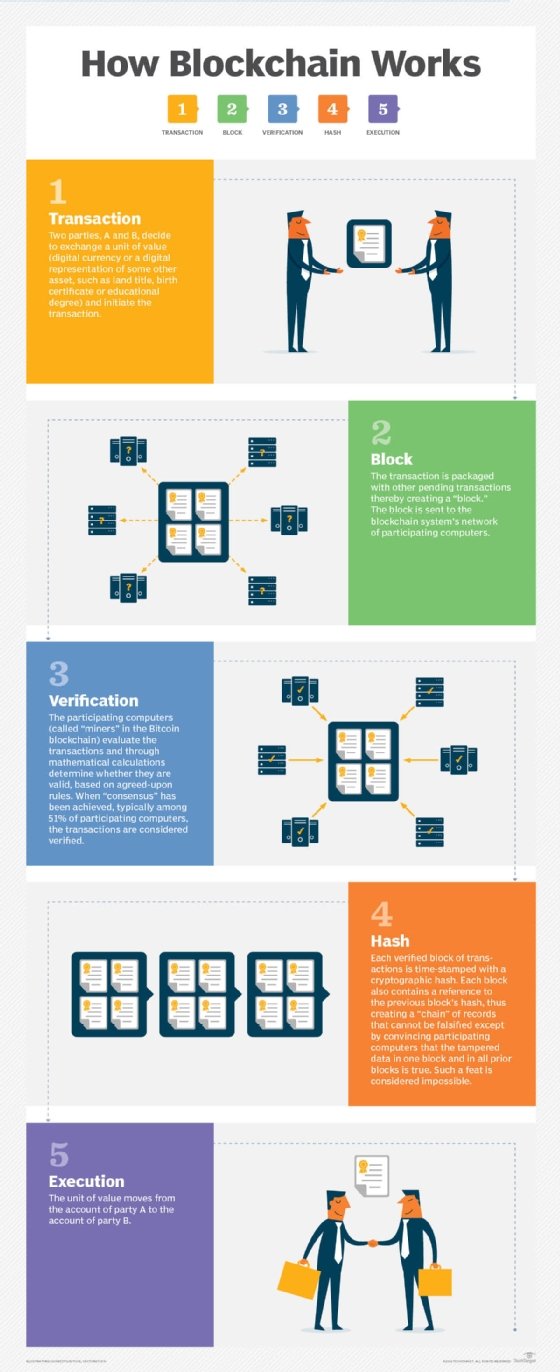
No central authority oversees or regulates the Bitcoin process. Bitcoin miners confirm and verify transactions by solving complex mathematical cryptography calculations that are then included in a block of the bitcoin blockchain. Bitcoin mining accomplishes three tasks: It verifies bitcoin transactions, creates a way to issue more currency and incentivizes more bitcoin mining.
Miners are given the latest batch of transaction data, which is run through a cryptographic algorithm. This algorithm generates a hash, or string of numbers and letters that validates a transaction without revealing any transaction data. The hash is designed to ensure its corresponding block hasn't been tampered with. If even one number is different or out of place, the corresponding data generates a different hash, which indicates tampering. Each block includes the previous block's hash so that if something has been changed in the previous block, the generated hash then changes.
The hash must also be below a specified length limit set by the hash algorithm. If the generated hash is too big, it's generated again until it is below its specified target. Miners are rewarded with bitcoin when they validate that the generated hash meets its target. This process, known as proof of work, proves that a miner has expended computational resources to validate the system.
The hashing process makes solving transaction-related algorithms more challenging over time. This means solving these algorithms also requires more computing resources -- such as mining hardware known as nodes and electricity -- over time.
The processing power for bitcoin mining requires access to powerful computers and large amounts of electricity. Bitcoin mining was originally done by individuals on single computers. However, because the difficulty level of solving transaction-related algorithms grows over time, individual computers are now highly unlikely to be able to mine bitcoin. As the cryptocurrency mining difficulty has increased, most bitcoin miners have turned to application-specific integrated circuits (ASICs) and other methods to mine bitcoin.
The mining reward amount decreases by half every four years. The reward began at 50 bitcoins per validated block in 2009 when Bitcoin launched and is currently 6.25 bitcoin per validated block.
What is proof of work in bitcoin mining?
In bitcoin mining, proof of work is a consensus mechanism that refers to the process where bitcoin miners verify bitcoin transactions. Proof of work requires miners to solve a hash function, or a complex mathematical puzzle; it is often compared to proof of stake. The first miner to solve the puzzle is rewarded with a newly minted bitcoin.
The hash function used in bitcoin mining is Secure Hash Algorithm 256-bit, or SHA-256. It takes an input and produces a unique output known as a hash. A miner's computational power is measured by their hash rate, which represents the number of hashes they calculate per second.
What are the risks of bitcoin mining?
The following risks are associated with mining bitcoin:
- Environmental. Bitcoin mining requires huge amounts of processing power and electricity; it accounts for more than 65 megatons of carbon dioxide emissions annually, according to Digiconomist. As a result, mining operations are generally located where electricity is cheaper, such as in China. However, China banned bitcoin mining in 2021, and since then mining operations have shifted to other countries. In a June 2023 paper, the MIT Center for Energy and Environmental Policy Research reported that as of the end of 2022, the U.S. and Canada accounted for at least 38% of all global bitcoin mining activity.
- Price volatility. Since its introduction, bitcoin price has varied widely. This volatility and the changing price of bitcoin rewards make it difficult for miners to know how much they will earn from the process.
- Profitability. Depending on factors such as the mining rig used, the cost of the mining machines, bitcoin volatility, changing reward prices and continued cost of electricity, there's no guarantee that bitcoin miners will continue to make enough money to pay for the operating costs.
- Regulatory risks. Cryptocurrency regulations continue to develop and change as Bitcoin becomes more popular. Regulations include how bitcoin are taxed and even bans on mining in some countries.
- Cryptojacking and scams. A prevalent malware threat is mining botnet infections known as cryptojacking, in which threat actors use compromised systems to mine bitcoin without the owners' knowledge. Phishing scams are also a risk to bitcoin mining, targeting miners through mining pools and fake mining software.
What do you need to mine bitcoin?
Originally, bitcoin miners used the central processing units (CPUs) of individual computers. Then they turned to systems with multiple graphics processing units (GPUs) and field-programmable gate arrays. Today, miners use ASICs in an attempt to find more hashes using less electrical power.
To partake in bitcoin mining, prospective miners need the following:
- Competitive mining computers. The computers miners use are often referred to as rigs. They include ASICs, the microchips designed for a specified application, which significantly help the mining process.
- Electricity. Power is the main operating expense, and the high cost of power keeps the profit margin associated with mining within a few cents per kilowatt-hour. Having an efficient power supply is a critical part of successful mining.
- Mining software. This software solves cryptographic math problems in the mining process. For example, this can be Open Source software, such as CGMiner.
- Mining pool. This process combines the computing resources of many miners to speed the hashing process.
What are bitcoin mining pools and farms?
The Bitcoin network aims to add a new block to the blockchain about every 10 minutes. It's difficult for an individual miner to create a new hash for a block. This is where mining pools help. They combine the computational resources of many individual miners to increase the chance of successfully hashing a block. Rewards are then distributed to the miners based on how many resources they provided. This method doesn't require as many upfront resources as individual bitcoin mining.
Bitcoin mining farms are similar to mining pools; however, with mining farms, mining rigs are typically all located in one location, data center or warehouse.
Is bitcoin mining legal?
Bitcoin mining is legal in many, but not all, countries. Some countries have passed regulations that ban owning, trading or mining bitcoin. Bitcoin mining is illegal, restricted or under significant governmental oversight in Algeria, Bolivia, China, Egypt, Morocco, Nepal and Pakistan.
Though not illegal in the United States, Bitcoin has become an increasingly regulated digital currency.
The economics of bitcoin mining
Bitcoin mining is not only critical to maintaining the security of the network, but it also provides an economic incentive for miners. Miners are rewarded by consensus algorithms with newly minted bitcoin and transaction fees for their work. This is known as a bitcoin block reward. Initially, the block reward was set at 50 bitcoin per block. However, as part of the Bitcoin protocol, the block reward is halved approximately every four years.
Bitcoin halving
The current block reward is 6.25 bitcoin per block. This reduction in block reward controls the inflation rate of bitcoin and ensures the total supply is capped at 21 million coins. Halving reduces the rate at which new bitcoin are created and makes bitcoin scarcer over time.
This scarcity, coupled with growing demand for bitcoin, has led to significant price increases. Bitcoin halving events are closely monitored by miners and investors alike, as they have a direct impact on the economics of bitcoin mining.
The cost of bitcoin mining
Mining bitcoin requires substantial computational power and energy consumption. The process of solving the complex mathematical puzzles requires specialized mining hardware, such as ASIC systems, which are optimized for bitcoin mining. These systems are significantly more efficient than traditional CPUs or GPUs and offer higher hash rates.
However, the cost of mining bitcoin goes beyond the initial investment in hardware. Electricity costs play a significant role in the profitability of mining operations. As the computational power required for mining increases, so does the amount of electricity consumed. Miners often seek locations with cheap electricity or renewable energy sources to minimize operational costs.
The history of bitcoin mining
Bitcoin mining has undergone significant evolution since its inception. Initially, miners used standard CPUs; they soon replaced these with GPUs, which have more computational power. The introduction of ASIC miners revolutionized the industry, making it more specialized and efficient.
GPU mining. GPUs, originally designed for graphics-intensive tasks, were first used for mining around 2010. They offered significant advantages over CPUs in terms of computational power and energy efficiency. Miners could mine bitcoin more effectively, leading to a greater chance of solving blocks and earning rewards.
ASIC mining. In 2013, miners developed ASIC miners, custom-built hardware designed for bitcoin mining. ASIC systems offer unparalleled computational power and energy efficiency, far surpassing the capabilities of CPUs and GPUs. These specialized machines transformed bitcoin mining, making it more competitive and centralized. Large mining operations with access to cheap electricity and specialized ASIC miners now dominate the market.
Learn about three of the most popular cryptocurrencies on the market -- Bitcoin, Ethereum and Dogecoin -- and how they differ.