CSO (Chief Security Officer)
What is a CSO (Chief Security Officer)?
A Chief Security Officer (CSO) is a C-suite executive responsible for a company's physical and digital security. The CSO provides executive leadership and oversees the identification, assessment and prioritization of risks, directing all efforts concerned with the security of the organization.
Modern companies have many valuable physical and digital assets. These include electronic devices, intellectual property, software, IT infrastructure and other items required for day-to-day operations.
Security breaches can disrupt work schedules and have a significant impact on the bottom line. Companies rely on the CSO to stay ahead of security issues, solve problems and ensure the organization runs smoothly.
Additionally, CSO expertise is required to implement safeguards and reporting risk management mechanisms for regulation compliance.
What are the key responsibilities of a Chief Security Officer?
The functions of the CSO role can be broken down into three main subcategories: prevention, governance and investigation.
Prevention
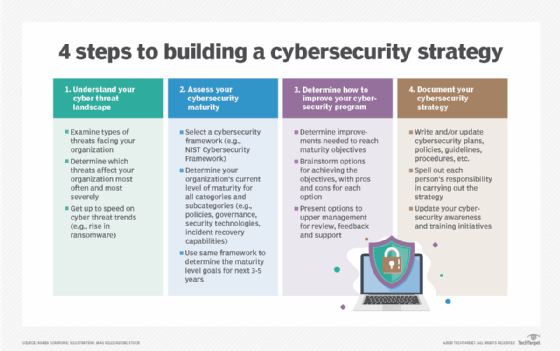
The CSO leads security initiatives and heads the overall security strategy of the company. This includes performing security risk assessments and implementing security policies that prevent data loss and fraud. Responding to new threats and upgrading security systems regularly are key aspects of this role.
Governance
The CSO is responsible for the day-to-day governance of corporate security. This includes access Authorization, identity checks and information systems protection. Managing data security during internal transitions is crucial for business continuity planning.
Investigation
The CSO manages the corporate security response to incidents -- this includes investigation, crisis management, disaster recovery and dealing with external security agencies.
What qualifications are required for a Chief Security Officer?
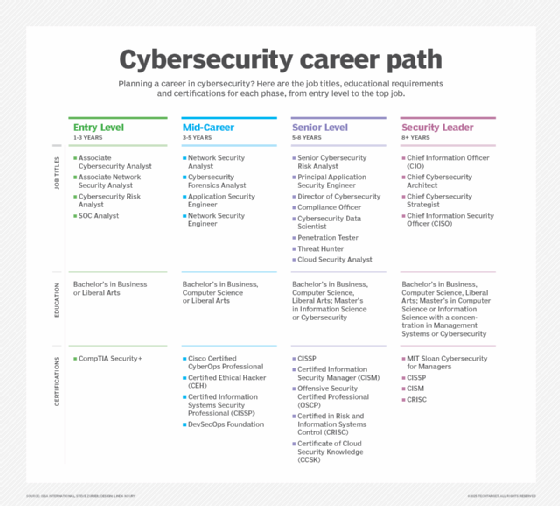
Typically, CSO candidates are expected to have advanced degrees in computer science, IT security, engineering or related disciplines.
Most job descriptions ask for a master's degree in cybersecurity and at least five years of experience in a security management role.
Security professionals or those with a bachelor's degree in a non-related discipline can transition to this role by completing additional IT certifications.
What other skills does a Chief Security Officer require?
The CSO typically requires a combination of technical and soft skills to succeed in the job. Sound knowledge of security systems, computer networks, programming languages, cybersecurity hardware and software is essential.
Strong research competencies are required for risk mitigation and regulatory compliance. Analytical thinking and problem-solving skills are necessary for incident response and crisis management.
Strong communication skills are essential to deal effectively with a variety of stakeholders, both internal and external. These include law enforcement agencies, homeland security, internal management and employees of different departments.
Leadership and management skills are also a must, given the seniority of this role. Candidates must have sufficient experience dealing with security incidents and leading security operations at the mid-management level to be considered suitable for the CSO role.

Who do Chief Security Officers report to?
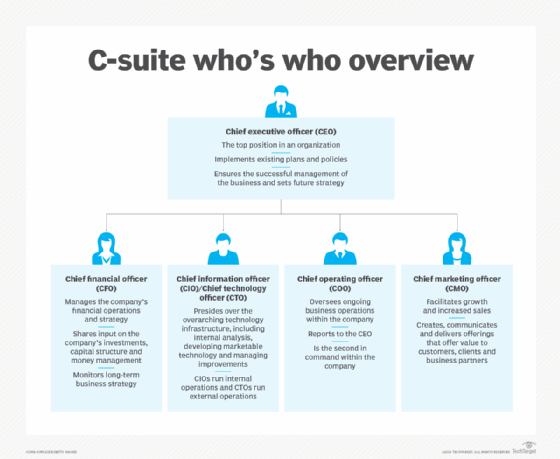
Depending on the size of a company and how security is integrated into company culture, a CSO may report to the Chief Information Officer (CIO) or the Chief Technology Officer (CTO), the Chief Risk Officer (CRO) or the Chief Executive officer (CEO).
A CSO may also work with other stakeholders like Human Resource Management, the Vice President of Security, or the Chief Procurement Officer to implement security functions throughout the organization.
In a large enterprise organization, the CSO may work closely with other security directors like the Chief Information Security Officer (CISO). If the company does not have a designated CISO or CSO, security responsibilities may be carried out by the CTO or CIO.
Outlook for the CSO role
The Bureau of Labor Statistics (BLS) predicts accelerated growth for information security analysts and related fields over the next decade.
Employment opportunities exist across multiple industries, and CSOs can work in financial services, information technology services, healthcare, pharmaceuticals, consulting, education and government contracting.
The BLS reports that average salaries can range from $150,000 to over $200,000 annually, depending on industry and work experience.
