
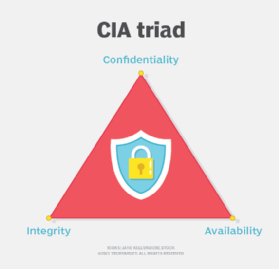
CIA triad (confidentiality, integrity and availability)
What is the CIA triad (confidentiality, integrity and availability)?
The CIA triad refers to confidentiality, integrity and availability, describing a model designed to guide policies for information security (infosec) within an organization. The model is sometimes referred to as the AIC triad -- which stands for availability, integrity and confidentiality -- to avoid confusion with the Central Intelligence Agency.
In this context, confidentiality is a set of high-level rules that limits access to all types of data and information. Integrity is the assurance that the information is trustworthy and accurate. And availability is a form of risk management to guarantee reliable access to that information by authorized people.
What are the 3 components of the CIA triad?
The following is a breakdown of the components of the CIA triad:
- Confidentiality. Roughly equivalent to privacy, confidentiality measures are designed to prevent sensitive information from unauthorized access attempts. It's common for data to be classified according to the amount and type of damage that could be done if it fell into the wrong hands. More or less stringent data security measures can then be implemented according to those categories.
- Integrity. The consistency, accuracy and trustworthiness of data must be maintained over its entire lifecycle. Data must not be changed in transit, and steps must be taken to ensure it can't be altered by unauthorized people -- for example, in data breaches.
- Availability. Information should be consistently and readily accessible for authorized parties. This involves properly maintaining hardware and technical infrastructure and systems that hold and display the information.
Why is the CIA triad important?
Each letter in the CIA triad represents a foundational principle in cybersecurity. The importance of the security model speaks for itself: Confidentiality, integrity and availability are considered the three most important concepts in infosec.
Considering these three principles together within the triad framework guides the development of security policies for organizations. When evaluating needs and use cases for potential new products and technologies, the triad helps organizations ask focused questions about how value is being provided in those three key areas.
This article is part of
What is data security? The ultimate guide
Thinking of the three concepts as an interconnected system, rather than as independent concepts, can help organizations understand the relationships between the three.
What are examples of the CIA triad?
Here are examples of the various management practices and technologies that constitute the CIA triad. While many CIA triad cybersecurity strategies implement these technologies and practices, this list is by no means exhaustive.
Confidentiality
Sometimes safeguarding data confidentiality involves special training for those handling sensitive documents. Training can familiarize authorized people with risk factors and help them with risk assessments and to guard against those risks. Further aspects of training include strong passwords and password-related best practices, as well as information about social engineering methods bad actors use to get users to make mistakes and break data-handling rules.
A good example of a method for protecting sensitive data and ensuring confidentiality is requiring an account number or routing number when banking online. Data encryption is another common method of ensuring confidentiality. User IDs and passwords constitute a standard procedure required for social media platforms, for example. Two-factor authentication (2FA) is also becoming commonplace in the healthcare and financial services industries.
Other options include real-time biometric verification, security tokens, key fobs and soft tokens. In addition, users can minimize the places where information appears and the number of times it's transmitted to complete a transaction. Extra measures might be taken in the case of extremely sensitive documents, such as storing only on air-gapped computers, on disconnected storage devices or in hard-copy form only.
Integrity
Measures related to data integrity include file permissions and user access controls. Version control is used to fix instances where an authorized user makes an erroneous change or accidental deletion. Organizations usually have some means to detect changes in data that occur as a result of non-human-caused events, such as an electromagnetic pulse or server crash.
Data might include checksums, even cryptographic checksums, for verification of integrity. Backups or redundancies must be available to restore the affected data to its correct state. Furthermore, digital signatures can be used to provide effective nonrepudiation measures, meaning evidence of logins, messages sent, and electronic document viewing and sending cannot be denied.
Availability
Rigorously maintaining hardware, performing hardware repairs immediately and maintaining a properly functioning operating system environment free of software conflicts are the best ways to ensure availability. It's also important to keep current with all system upgrades. Providing adequate communication bandwidth and preventing bottlenecks are also important tactics. Redundancy, failover, redundant array of independent disks (RAID) and even high availability clusters can mitigate serious consequences when hardware issues do occur.
Fast, adaptive disaster recovery (DR) plans are essential for the worst-case scenarios and require a comprehensive approach. Safeguards against data loss or interruptions in connections must include unpredictable events, such as power outages, natural disasters and fire. To prevent data loss from such occurrences, backup copies can be stored in a geographically isolated location or fireproof, waterproof safe. Extra security equipment and software, such as firewalls and proxy servers, can guard against downtime. They also help prevent security incidents that result in unreachable data blocked by malicious denial-of-service attacks, ransomware and other malware or cyber attacks.
Benefits of the CIA triad
The CIA triad provides multiple benefits to businesses, especially to ones that deal with sensitive data. The benefits of triad implementation include the following:
- Data security and privacy. The most obvious benefit is ensuring preparedness in the face of today's sophisticated cyber attacks and other unauthorized attempts to access, steal or manipulate valuable data.
- Compliance. Ensuring the confidentiality, integrity and availability of sensitive information means regulations and legal frameworks that exist to safeguard this information are followed.
- Proactive risk prevention. When applied correctly, the triad creates an environment where security risks are proactively prevented. Existing vulnerabilities are identified and mitigated to prevent future threats.
- Comprehensiveness. The three components mean that security teams aren't just concerned with thwarting attackers, but they're also ensuring the veracity and availability of their data. For example, when a large volume of data is needed for analysis, following the CIA triad means the data is available and accessible when needed.
CIA triad challenges
Challenges or concerns that may arise when attempting to adhere to this triad include the following:
- Large data volumes. Big data poses challenges to the CIA paradigm because of the sheer volume of information that organizations need safeguarded, the many sources that data comes from and the variety of formats in which it exists. Duplicate data sets and DR plans can multiply the already-high costs.
- Data stewardship and governance. Because the main concern of big data is collecting and making some kind of useful interpretation of all this information, responsible data stewardship, auditing and oversight are often lacking. Whistleblower Edward Snowden brought that problem to the public forum when he reported on the National Security Agency's collection of massive volumes of U.S. citizens' personal data.
- Internet of things (IoT) security and privacy. Almost any physical or logical entity or object can be given a unique identifier and the ability to communicate autonomously over the internet or a similar network. The data transmitted by an IoT endpoint might not cause any privacy issues on its own. However, when even fragmented data from multiple endpoints is gathered, collated and analyzed, it can yield sensitive information. IoT security is challenging because it involves so many internet-enabled devices that often go unpatched and are configured with default or weak passwords. Unless adequately protected, IoT can be used as a separate attack vector or part of a thingbot.
- Security in product development. As more products are developed with the capacity to be networked, it's important to routinely consider security in product development. The amount of potential attack vectors for hackers and other malicious actors who want to access sensitive information increases as more network-connected products become available.
Best practices for implementing the CIA triad
In implementing the CIA triad, an organization should follow a general set of best practices. These can be divided into the three subjects and include the following:
- Confidentiality
- Follow an organization's data-handling security policies.
- Use encryption and 2FA.
- Keep access control lists and other file permissions up to date.
- Integrity
- Ensure employees are knowledgeable about compliance and regulatory requirements to minimize human error.
- Use backup and recovery software and services.
- Use version control, access control, security control, data logs and checksums.
- Availability
- Use preventive measures, such as redundancy, failover and RAID.
- Ensure systems and applications stay updated.
- Use network or server monitoring systems.
- Have a data recovery and business continuity plan in place in case of data loss.
The history of the CIA triad
The CIA triad doesn't have a single creator. The term confidentiality may have first been used in computer science as early as 1976 in a study by the U.S. Air Force. Likewise, the concept of integrity was explored in a 1987 paper titled "A Comparison of Commercial and Military Computer Security Policies" written by David Clark and David Wilson. That paper recognized that commercial computing had a need for accounting records and data correctness. Even though it isn't as easy to find an initial source, the concept of availability became more widely used in 1988.
By 1998, people were using the three concepts together as the CIA triad. That year, infosec researcher and consultant Donn B. Parker wrote a book called Fighting Computer Crime that broadened the CIA triad to a hexad consisting of three added elements: authenticity, possession or control, and utility. For more than two decades, organizations have had varying perspectives on the CIA triad, applying it to their cybersecurity strategies in ways that meet their needs. Some experts believe the triad needs an upgrade to stay effective.
Enterprises can choose from a number of security frameworks. Learn about some of the top IT security frameworks and how to choose the right one for your organization.