What is EM shielding (electromagnetic shielding)?
EM shielding (electromagnetic shielding) is the practice of surrounding electronics and cables with conductive or magnetic materials to guard against incoming or outgoing emissions of electromagnetic frequencies (EMF).
EM shielding is commonly used to prevent electromagnetic interference (EMI) or radio frequency interference (RFI) from affecting sensitive electronic components. Such interference can disrupt operations, corrupt data or even damage equipment. The interference might be caused by natural phenomena, such as lightning or solar flares, or by human technology, such as high-power transmitters or malfunctioning consumer devices.
EMI and RFI are sometimes used interchangeably or treated as two unrelated phenomena. However, radio waves are a subset of the larger EM spectrum. Even so, any incoming EMF can be a concern, as can outgoing EMF, which can potentially put an organization's sensitive data and systems at risk. There is also a growing concern about the impact of EMF on living organisms, especially as human-generated EMF continues to increase.
Materials and techniques used for EM shielding
A number of different materials and techniques are used for EM shielding. Most shields are made of some type of metal, such as copper, aluminum, steel or nickel. Metals possess the conductive and magnetic properties necessary to effectively mitigate the impact of incoming or outgoing EMF. In many cases, a shield will use a metal alloy, such as mu-metal, a nickel-iron ferromagnetic substance. An EM shield might also use a polymer that contains metallic elements.
The type and thickness of the material used for EM shielding will depend on the specific situation. For example, shielding might be used for incoming EMF, outgoing EMF or both. The kind of shielding will also depend on the components being protected and the type of EM energy. The following techniques represent some common approaches to EM shielding:
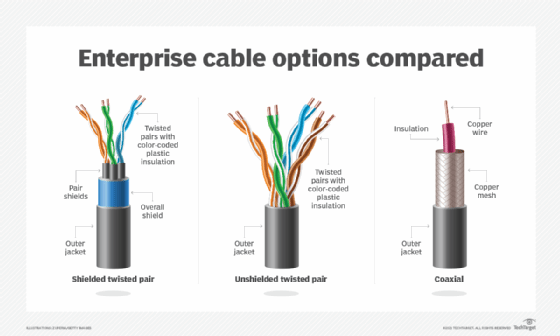
- Metallic foil or braids. Certain types of wires and cables can be surrounded by a metallic foil or braided shield to block errant EMI from core wiring.
- Metallic mesh. Metallic mesh shields are often used to prevent a component within a device from affecting another component in that device.
- Metallic sheets. A flat piece of thin metal, often a type of alloy, can be used in a variety of situations to provide EM shielding. The metallic sheet can be easily cut and formed to a specific shape.
- Metallic casing. Components are encased within a metallic enclosure that isolates them and protects them from EMI. For example, a metallic casing might be used to protect the circuits in a printed circuit board (PCB). The casing acts like a miniature Faraday cage, which is a conductive structure that surrounds equipment to block EM radiation.
- Conductive paint. Special conductive paint can be used to protect a room, building or other space from EMI. It can also prevent EM radiation from spreading outside that space, where it might be susceptible to eavesdropping or wireless attacks.
- Conductive foam. Special foam can be used to protect electronic equipment from EMI or RFI, providing a lightweight, flexible and low-cost shielding option that can be used in a variety of situations.
- Shielding gaskets. Conductive material is formed into specific shapes to seal connections and openings against EM radiation.
- Filters. Electronic connections might be filtered for EMI using components such as capacitors, ferrules or grounded wires. Even twisting wires together with grounds can help reduce interference.
An EM shield does not necessarily need to completely enclose a component as long as any openings are smaller than the EM waves being blocked. If blocking against a magnetic field with a range of less than 100 kHz, the EM shield must use magnetic materials, which redirect the magnetic field lines rather than block them.
How EM shielding is used
EM shielding is widely used in applications ranging from consumer electronics to NASA spacecraft. In a smartphone, for example, a metallic shield protects electronics from its cellular transmitter/receiver. Shielding in mobile phones also decreases the amount of RF energy that might be absorbed by the user. Audio speakers, on the other hand, often have inner metallic casings to block the EMI produced by nearby devices.
EM shielding is also used in a wide range of medical equipment, from pacemakers to patient monitoring systems. It's also incorporated into PCBs, hard disk drives and equipment cabinets in data centers. In addition, EM shielding is used to create a barrier around digital devices to prevent illegal access to the data, such as that stored on an RFID chip or embedded in the device.
EM shielding can also play a role in protecting air-gapped systems, which are physically isolated and lack external connectivity. Shielding prevents EM energy from escaping, thereby eliminating a potential vulnerability. Air-gapping is often used by military, government and financial institutions, as well as by reporters, activists and human rights organizations working with sensitive information.
EM shielding is used in other ways as well. For instance, it is commonly used to enclose high-current areas, such as substations or switch rooms, especially those near occupied spaces. Individuals might also employ shielding techniques to protect their homes or offices, perhaps painting their walls with shielding paint. EM shields can also be found in automobiles, satellites, airplanes, ships, laboratories and other places.
See wireless network configuration steps to follow, an overview of network management tasks and best practices, different types of configuration tools for network change management and how to troubleshoot wireless network connection problems.
