corporate governance
What is corporate governance?
Corporate governance is the combination of rules, processes and laws by which businesses are operated, regulated and controlled. The term encompasses the internal and external factors that affect the interests of a company's stakeholders, including shareholders, customers, suppliers, government regulators and management.
The board of directors or corporate executive board is responsible for creating a framework for corporate governance that best aligns business conduct with corporate objectives. Good corporate governance involves establishing principles of security, transparency, equity, compliance, reliance and accountability.
Importance of corporate governance
Corporate governance is critical for the proper functioning of an organization. Demonstrating good corporate governance is important for maintaining a company's reputation.
Corporate governance is based on a set of rules, bylaws, policies and procedures to ensure company accountability. When done correctly, it establishes a framework for attaining a company's objectives in all spheres of management. It also recognizes the importance of shareholders. Shareholders elect the company's members of the board, fund company operations and have a direct say in the operation of the business.
Good governance ensures a company's integrity, overall direction, risk management and success planning. This, in turn, helps companies stay financially viable and build strong community, shareholder and investor relations and trust. Demonstrating good corporate governance is often considered as important as profitability for businesses.
Bad corporate governance can lead to a host of negative outcomes, such as the following:
- failure to reach company goals;
- loss of support from stakeholders and community;
- financial losses; and
- collapse of the company.
Principles of corporate governance
While corporate governance structures may vary, most organizations incorporate the following key elements:
- Fair and equitable treatment. All shareholders, customers, employees and other stakeholders should be treated equally and fairly. Part of this is making sure shareholders are aware of their rights and how to exercise them.
- Accountability. Legal, contractual and social obligations to both shareholders and nonshareholders must be upheld. Organizations should define a code of conduct for board members; board committees, such as the audit committee and compensation committee; and senior executives. New individuals joining those ranks must meet those established standards.
- Diversity. The board of directors must maintain a commitment to ensure diversity within corporate governance and the company overall.
- Oversight and management. Board members must also possess the adequate skills necessary to review management practices.
- Transparency. All corporate governance policies and procedures should be disclosed to relevant stakeholders. This includes regularly and consistently communicating pertinent information to employees, customers, investors, vendors and members of the community.

Conflict management in corporate governance
One purpose of corporate governance is to implement a checks-and-balances system that minimizes conflicts of interest between various stakeholders and with any individual party.
Conflicts arise when two parties have opposing opinions or goals on the way business should be conducted. Conflicts of interest can also arise when individual stakeholders might gain personally from a corporate action or decision they have a say in. The board of directors should provide a nonbiased way to handle these sorts of conflicts.
Conflicts can occur when executives disagree with shareholders. For example, the shareholders may want to pursue goals that generate greater profits, while the chief executive officer might want to invest in better employee engagement efforts. Another type of conflict could arise if multiple shareholders disagree with each other.
Personal conflicts of interest or conflicts among directors, audit plan administrators and company executives are typically disclosed in proxy statements. A proxy statement is a document that shareholders use to evaluate the qualifications and compensation of the board of directors and key senior management staff.
Public companies are required by the Securities and Exchange Commission to release proxy statements. They are shared during annual meetings when a company is soliciting shareholder votes on a given matter, such as nominating a new member to the corporate boards.
Examples of corporate governance
Specific processes that can be outlined in corporate governance may include the following:
- action plans;
- performance measurement;
- environmental, social and governance principles;
- disclosure practices;
- executive compensation decisions;
- dividend policies;
- decision-making practices;
- procedures for reconciling conflicts of interest; and
- explicit or implicit contracts between the company and stakeholders.
An example of good corporate governance practices is a well-defined and enforced structure that works for the benefit of everyone concerned by ensuring that the enterprise adheres to accepted ethical standards, best practices and formal laws.
Alternatively, bad corporate governance is poorly structured, ambiguous and noncompliant approaches to running a business. All of these approaches can damage the image or financial health of a business.
The Enron scandal is an example of poor corporate governance. Enron Corp. declared bankruptcy in 2001 -- just months before it was one of the largest companies in the U.S. Enron falsely reported its revenue by a wide margin and used fraudulent methods to hide debts and toxic assets from investors and regulators to avoid accountability. This scandal had a lasting effect on Wall Street and led the government to pass new regulations on corporate accountability and governance.
Good corporate governance often goes unnoticed in the public sphere. One example of a company with a reputation for good corporate governance is PepsiCo. In its 2020 proxy statement, the company outlined its leadership structure and changes to the compensation program, as well as input from investors in the following areas:
- business sustainability issues;
- human capital management;
- ethical corporate culture; and
- long-term strategy and corporate purpose.
Regulation of corporate governance
Corporate governance has received increased attention because of high-profile scandals involving abuse of corporate power or alleged criminal activity by corporate officers. To counteract those activities, various laws and regulations have been passed to address the components of corporate governance guidelines, including the following:
- Basel II. This business standard minimizes the financial effect of risky operational decisions. Basel II includes the rights of shareholders, thus affecting corporate governance.
- Gramm-Leach-Bliley Act. This act, also known as the GLB Act, regulates the ways that financial institutions handle private information. It requires that companies include how they oversee financial organizations and stakeholders in their corporate governance strategy.
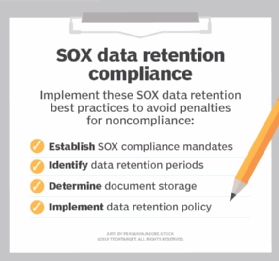
- Sarbanes-Oxley Act. Also known as SOX, this act was passed after it was found that high-profile companies and their executives were committing fraud -- specifically, Enron and WorldCom. As a result, emphasis was placed on corporate governance as a way to restore faith in public companies.
Good corporate governance depends on complying with various regulations, both general and industry-specific. Learn the top cloud compliance standards and how cloud companies can use them.





