information technology (IT)
What is information technology?
Information technology (IT) is the use of any computers, storage, networking and other physical devices, infrastructure and processes to create, process, store, secure and exchange all forms of electronic data. Typically, IT is used in the context of business operations, as opposed to technology used for personal or entertainment purposes. The commercial use of IT encompasses both computer technology and telecommunications.
The Harvard Business Review coined the term information technology to make a distinction between purpose-built machines designed to perform a limited scope of functions, and general-purpose computing machines that could be programmed for various tasks. As the IT industry evolved from the mid-20th century, computing capability increased, while device cost and energy consumption decreased, a cycle that continues today when new technologies emerge.
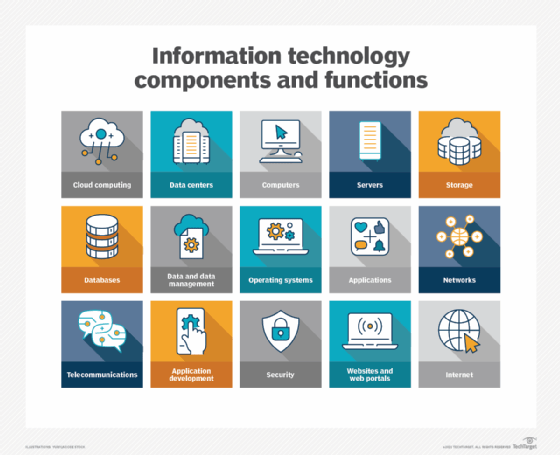
What does information technology encompass?
The IT department ensures that the organization's systems, networks, data and applications all connect and function properly. The IT team handles three major areas:
- deploys and maintains business applications, services and infrastructure (servers, networks, storage);
- monitors, optimizes and troubleshoots the performance of applications, services and infrastructure; and
- oversees the security and governance of applications, services and infrastructure.
Most IT staff have different responsibilities within the team that break into several key areas including:
- Administration. Administrators handle the day-to-day deployment, operation and monitoring of an IT environment, including systems, networks and applications. Admins often perform a range of other duties such as software upgrades, user training, software license management, procurement, security, data management and observing adherence to business process and compliance requirements.
- Support. Help desk staff specialize in answering questions, gathering information and directing troubleshooting efforts for hardware and software. IT support often includes IT asset and change management, helping admins with procurement, handling backup and recovery of data and applications, monitoring and analyzing logs and other performance monitoring tools and following established support workflows and processes.
- Applications. Businesses rely on software to perform work. Some applications are procured and deployed from third parties, such as email server applications. But many organizations retain a staff of skilled developers that create the applications and interfaces -- such as APIs -- needed to deliver critical business capabilities and services. Applications might be coded in a wide array of popular languages and integrated with other applications to create smooth and seamless interactions between different applications. Developers might also be tasked with creating interactive business websites and building mobile applications. The trend toward agile or continuous development paradigms require developers to be increasingly involved with IT operations, such as deploying and monitoring applications.
- Compliance. Businesses are obligated to observe varied government- and industry-driven regulatory requirements. IT staff play a major role in securing and monitoring access to business data and applications to ensure that such resources are used according to established business governance policy that meets regulatory requirements. Such staff are deeply involved with security tasks and routinely interact with legal and business teams to prevent, detect, investigate and report possible breaches.
Why is information technology important?
It's been said that data is what powers industries worldwide. That may be hyperbole, but few businesses -- large or small -- can remain competitive without the ability to collect data and turn it into useful information. IT provides the means to develop, process, analyze, exchange, store and secure information.
Data processing plays a significant role in these core business practices, among others, including:
- product development and design;
- marketing and market research;
- sales and invoicing;
- customer development and retention;
- accounting and taxes;
- human resources and payroll; and
- regulatory compliance.
Computing has penetrated practically every part of business and much of our personal lives. The ubiquity of computing -- also referred to as pervasive computing -- is another reason why IT is critical. Computing devices have evolved well beyond personal computers and servers. Today, all businesses and most individuals have and use multiple computing devices, including phones, tablets, laptops, game consoles and even doorbells, thermostats, vacuums and many kitchen appliances.
Virtually all these devices, many of which are part of the IoT, tap into the internet, which interconnects billions of devices worldwide. It's a complex and, potentially, perilous environment that requires IT expertise for management, security, maintenance and reliability.
Examples of information technology
So how is IT actually involved in day-to-day business? Consider five common examples of IT and teams at work:
- Server upgrade. One or more data center servers near the end of their operational and maintenance lifecycle. IT staff will select and procure replacement servers, configure and deploy the new servers, backup applications and data on existing servers, transfer that data and applications to the new servers, validate that the new servers are working properly and then repurpose or decommission and dispose of the old servers.
- Security monitoring. Businesses routinely employ tools to monitor and log activity in applications, networks and system IT staff receive alerts of potential threats or noncompliant behavior -- such as a user attempting to access a restricted file -- check logs and other reporting tools to investigate and determine the root cause of the alert and take prompt action to address and remediate the threat, often driving changes and improvements to security posture that can prevent similar events in the future.
- New software. The business determines a need for a new mobile application that can allow customers to log in and access account information or conduct other transactions from smartphones and tablets. Developers work to create and refine a suitable application according to a planned roadmap. Operations staff posts each iteration of the new mobile application for download and deploy the back-end components of the app to the organization's infrastructure.
- Business improvement. A business requires more availability from a critical application to help with revenue or business continuance strategies. The IT staff might be called upon to architect a high-availability cluster to provide greater performance and resilience for the application to ensure that the application can continue to function in the face of single outages. This can be paired with enhancements to data storage protection and recovery.
- User support. Developers are building a major upgrade for a vital business application. Developers and admins will collaborate to create new documentation for the upgrade. IT staff might deploy the upgrade for limited beta testing -- allowing a select group of users to try the new version -- while also developing and delivering comprehensive training that prepares all users for the new version's eventual release.
Software vs. hardware
IT includes several layers of physical equipment (hardware), virtualization, management systems, automation tools, operating systems, other system software and applications used to perform essential functions. User devices, peripherals and software can be included in the IT domain. IT can also refer to the architectures, methodologies and regulations governing the use and storage of data.
Software
There are two categories of software: system software and applications. System software encompasses the computer programs that manage the basic computing functions. They include the following:
- OSes;
- BIOSes;
- boot programs;
- assemblers; and
- device drivers.
Business applications include:
- databases, such as SQL Server;
- transactional systems, such as real-time order entry;
- email servers, like Microsoft Exchange
- web servers, like Apache and Microsoft's Internet Information Services (IIS);
- customer relationship management, such as Oracle NetSuite and HubSpot; and
- enterprise resource planning systems, such as SAP S/4HANA.
These applications make use of programmed instructions to manipulate, consolidate, disperse and otherwise work with data for a business purpose.
Mobile applications that run on smartphones, tablets and other portable devices typically connect with cloud or data center applications over the internet. These applications have expanded the scope of computing and created a new category of software and telecommunications that requires special expertise to maintain.
Hardware
There are many different types of computer hardware. Computer servers run business applications. Servers interact with client devices in the client-server model. They also communicate with other servers across computer networks, which typically link to the internet.
Storage is another type of hardware. It's any technology that holds information as data. Storage may be local on a specific server or shared among many servers, and it may be installed on premises or accessed via a cloud service. Information that is stored can take many forms, including file, multimedia, telephony, and web and sensors data. Storage hardware includes volatile random-access memory (RAM) as well as non-volatile tape, hard disk drives and solid-state drives.
Telecom equipment, comprising network interface cards (NICs), cabling, wireless communications and switching devices, connect the hardware elements together and to external networks.
Abstracting hardware and software
IT architectures have evolved to include virtualization and cloud computing, where physical resources are abstracted and pooled in different configurations to meet application requirements. Clouds may be distributed across locations and shared with other IT users, or they can be contained within a corporate data center, or some combination of both deployments.
Volatility is a characteristic of virtualized resources, enabling them to expand and contract as needed. Subscription-based cloud or locally installed resources, such as storage or composable architectures, can spin up resources, such as servers, OSes and application software, as needed and then release them when processing is complete.
Information technology vs. computer science
When researching careers in IT, you're likely to come across the term computer science. While there is overlap between IT and computer science, the two are distinct disciplines with different courses of study to prepare for careers in either area.
Information technology
IT is generally associated with the application of technology to deal with business issues. As such, the IT workforce is oriented toward developed technologies such as hardware systems, OSes and application software. Proficiency in IT is required to identify the hardware and software components that should be used to enhance a specific business process. IT pros work with a variety of technologies, such as server OSes, communications devices and software, and applications.
Preparation for an IT career requires basic courses in hardware and software systems. IT degree programs may include subjects such as:
- business analysis
- project management
- telecommunications
- network administration
- database design
- database management
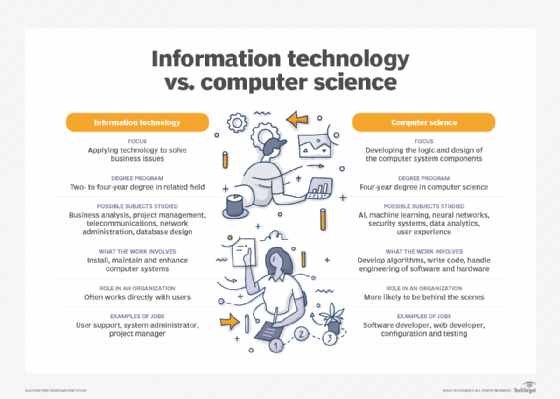
Computer science
Computer science focuses on the logic and design of the underpinnings of the components that IT experts use to assemble business systems. A strong mathematics background is required to pursue a computer science career. Much of the work in computer science involves developing the algorithms and logic and writing the low-level code that enables computer systems to address business problems.
Computer scientists may participate in the hardware and software engineering work required to develop products. They are also likely to delve into more abstract technologies, such as artificial intelligence (AI) and machine learning (ML).
A course of study in computer science requires a foundation in computer concepts and advanced mathematics. It may be complemented with subjects such as:
- AI and ML
- neural networks
- security systems
- data analytics
- user experience
Careers in information technology
A team of administrators and other technical staffers deploy and manage a company's IT infrastructure and assets. IT teams depend on a range of specialized information and technology skills and knowledge to support equipment, applications and activities. Third-party contractors and IT vendor support personnel augment the IT team.
The information technology profession is extremely diverse. IT workers can specialize in fields such as software development; application management; hardware components; server, storage or network administration; network architecture; and more. Many businesses seek IT professionals with mixed or overlapping skill sets.
There is a wide array of IT careers, each with varying technological and managerial requisites. Among the most common IT job titles are the following:
- Chief information officer (CIO). This person is responsible for IT and computer systems that support the goals of the business.
- Chief technology officer (CTO). This person sets the technology goals and policies within an organization.
- IT director. This person is responsible for the function of the business's technology tools and processes. This role may also be called IT manager or IT leader.
- System administrator (sys admin). This person configures, manages, supports and troubleshoots a multiuser computing environment. Within a business, this role can be divided up by technology, requiring an administrator or team dedicated to server, desktop, network administration, virtualization, or other components and technologies.
- Application manager. This person's role centers on the provisioning and management of a high-value business application, such as Exchange.
- Developer or software engineer. This person or team writes, updates and tests code for computer programs to meet internal or customer-facing business objectives.
- Chief IT architect or IT architect. This person examines and changes IT functions to best support the business.
IT skills and certifications
A successful IT career will involve developing several technical skills. For the current IT job market, these 10 skills are among those most in demand:
- cybersecurity
- cloud computing
- edge computing and IoT
- IT automation
- software development
- big data management and data analytics
- DevOps
- AI
- ML
- mobile application development
In the pursuit of these IT disciplines, it is advantageous to earn certification to demonstrate proficiency in specific technologies and areas of expertise. Some of the most highly regarded certifications include the following:
- AWS Certified Solutions Architect -- Professional
- Certified Ethical Hacker (CEH)
- Certified in Risk and Information Systems Control (CRISC)
- Certified Information Security Manager (CISM)
- Certified Information Systems Security Professional (CISSP)
- Cisco Certified Network Associate (CCNA)
- Google Certified Professional Cloud Architect (GCP)
- Microsoft role-based certifications
- Project Management Professional (PMP)
- VMware Certified Professional (VCP)






