Information Technology Amendment Act 2008 (IT Act 2008)
What is the Information Technology Amendment Act 2008 (IT Act 2008)?
The Information Technology Amendment Act 2008 (IT Act 2008) is a substantial addition to India's Information Technology Act 2000.
The Information Technology Amendment Act was passed by the Indian Parliament in October 2008 and came into force a year later. The act is administered by the Indian Computer Emergency Response Team (CERT-In) and corresponds to the Indian Penal Code.
The Information Technology Amendment Act has been widely hailed as a progressive step forward in protecting India's cyber infrastructure and citizens.
It is one of the most comprehensive pieces of legislation addressing IT-related issues and sets a strong precedent for other countries working to update their own laws.
Why was the Information Technology Amendment Act created?
The original version of the act was developed to promote the IT industry, regulate e-commerce, facilitate e-governance and prevent cybercrime.
However, it also sought to foster security practices within India that would serve the country in a global context.
In addition, the Information Technology Amendment Act established the office of the Cyber Appellate Tribunal to hear appeals from any person aggrieved by an order made under the act.
What does the Information Technology Amendment Act cover?
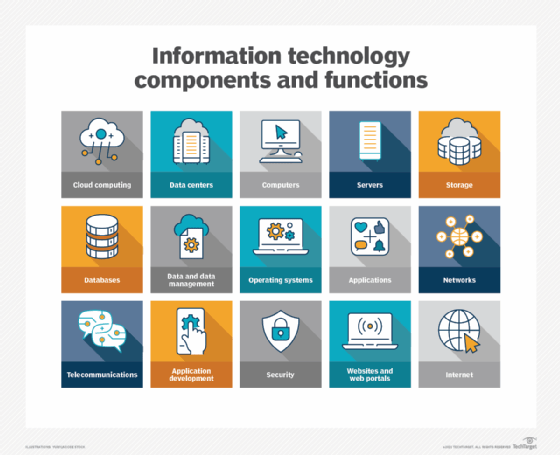
The Information Technology Amendment Act 2008 has nine chapters and 117 sections and covers a wide range of topics related to IT, cybercrime and data protection.
The act includes provisions for the following
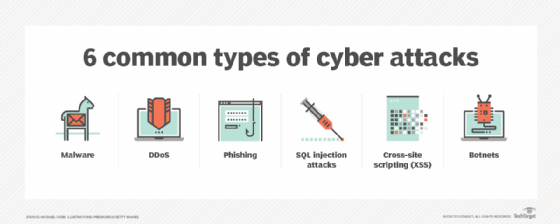
- tightening cybersecurity measures
- establishing a legal framework for digital signatures
- recognizing and regulating intermediaries
- regulating interception, monitoring and decryption of electronic records
- cyber forensics
- cyberterrorism
Amendments to the act have been created to address issues that the original bill failed to cover and to accommodate further development of IT and related security concerns since the original law was passed.
How has the Information Technology Amendment Act been updated?
Changes to the amendment over the years have included the following:
- redefining terms such as communication devices to reflect current use;
- validating electronic signatures and contracts;
- making the owner of a given IP address responsible for content accessed or distributed through it; and
- making corporations responsible for implementing effective data security practices and liable for data breaches.
In recent years, the IT Act has also been updated to include provisions for the regulation of intermediaries, penalties for cybercrime and restrictions on certain types of speech.
These changes included expanding the definition of cybercrime and adding new penalties for offenses such as identity theft, publishing private images without consent, cheating by impersonation, and sending offensive messages or those containing sexually explicit acts through electronic means.
Who does the Information Technology Amendment Act apply to?
The Information Technology Amendment Act is applicable to any person, company or organization that uses computer systems, computer networks or other information technology in India.
This includes but is not limited to the following:
- web hosting service providers
- internet service providers
- network service providers
- telecom service providers
This includes foreign companies and organizations with a presence in India, as well as Indian companies and organizations with operations outside of India.
What are the penalties for violating the Information Technology Amendment Act?
Penalties for violating the Information Technology Amendment Act can range from a fine of 1 lakh rupees (approximately $1,250) to imprisonment for up to three years.
More serious offenses can result in a person being liable to pay damages up to 5 lakh rupees (approximately $6,300) and include imprisonment of up to seven years.
Cyberterrorism offenses are punishable by imprisonment of up to 10 years.
In addition to these penalties, the court can also order the offender to pay compensation to the victim of the offense.
Challenges with the Information Technology Amendment Act
The amendment has been criticized for decreasing the penalties for some cybercrimes and for lacking sufficient safeguards to protect the civil rights of individuals.
Subsection 69, for example, authorizes the Indian government to intercept, monitor, decrypt and block data at its discretion.
According to Pavan Duggal, a cyber law consultant and advocate at the Supreme Court of India: "The Act has provided the Indian government with the power of surveillance, monitoring and blocking data traffic. The new powers under the amendment act tend to give Indian government a texture and color of being a surveillance state."
Still, the IT Act has been instrumental in developing a comprehensive legal framework for IT in India.
It has been successful in establishing procedures for electronic governance and the prevention of cybercrime.
The act will likely continue to be amended as needed to reflect the ever-changing landscape of IT.
See also: CERT-In (the Indian Computer Emergency Response Team).
