public-private partnership (PPP)
What is a public-private partnership (PPP)?
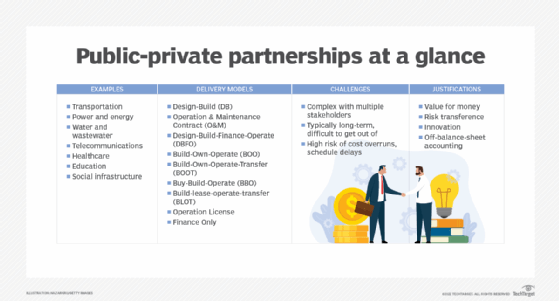
A public-private partnership (PPP) is a funding model for public infrastructure projects and initiatives such as a new telecommunications system, public transportation system, airport or power plant.
Government agencies represent the public partner at a local, state and/or national level. The private partner can be a privately-owned business, public corporation or consortium of companies with a specific area of expertise.
PPP is a broad term that can be applied to anything from a simple, short-term management contract -- with or without private investment requirements -- to a long-term contract that includes funding, planning, building, operation, maintenance and divestiture.
PPP projects (also known as P3 projects) are helpful for large ventures that require the procurement of highly skilled workers and a significant cash outlay to get started.
They are also helpful in countries, such as the United Kingdom or the Philippines, that require the state to legally own any infrastructure that serves the public.
Examples of sectors involved in PPPs
While PPPs can cover a range of projects across various sectors, there are several that are most associated with these types of initiatives. Here are a few examples.
- Transportation. PPPs are being used to finance, build and operate many different types of transportation infrastructure, including roads, bridges, tunnels, airports, seaports, railway systems and public transit.
- Power and energy. P3s have been used to finance and construct electricity generation plants (including nuclear), electrical transmission lines and natural gas pipelines.
- Water and wastewater. P3s have been used to finance, design, construct and operate water treatment plants, desalination plants and sewer systems.
- Telecommunications. P3s have been used to fund broadband networks and other telecommunications infrastructure rollouts.
- Healthcare. P3s have been used to finance the construction of hospitals, clinics and other healthcare facilities.
- Education. P3s have been used to finance the construction of educational facilities such as schools, colleges and universities.
- Social infrastructure. P3s have also been used to finance the construction of prisons, courthouses and other social infrastructure.
PPP project delivery models:
There are various PPP contract models based on funding and which partner is responsible for owning and maintaining assets at different stages of the government project.
Examples of PPP models include:
- Design-build (DB). The private-sector partner designs and builds the infrastructure to meet the public-sector stakeholder's specifications, often for a fixed price. The private-sector partner assumes all risk.
- Operation and maintenance contract (O&M). The private firm, under contract, operates a publicly owned asset for a specific period. The public partner then retains ownership of the assets.
- Design-build-finance-operate (DBFO). The private-sector company designs, finances and constructs a new infrastructure component and owns the operation and maintenance under a long-term lease. When the lease is up, the private-sector partner transfers the infrastructure component to the public-sector partner.
- Build-own-operate (BOO). The private party finances, builds, owns and operates the infrastructure component perpetually. The public-sector partner's constraints are stated in the original agreement and through ongoing regulatory authority.
- Build-own-operate-transfer (BOOT). Privatization is granted for financing, design, building and operation of an infrastructure component (and to charge user fees) for a specific time, after which ownership is transferred back to the public-sector partner.
- Buy-build-operate (BBO). This publicly owned asset is legally transferred to a private-sector partner for a designated period.
- Build-lease-operate-transfer (BLOT). The private-sector partner designs, finances and builds a facility on leased public land. The private-sector partner operates the facility for the duration of the land lease. When the lease expires, assets are transferred to the public-sector partner.
- Operation license. The private-sector partner is granted a license or other expression of legal permission to operate a public service, usually for a specified term. (This model is often used in IT projects.)
- Finance only. The private entity partner, usually a financial services company, funds the infrastructure component and charges the public-sector partner interest to use the funds.
Challenges with PPP models
The PPP model is not without its challenges. P3 projects are often complex, with multiple stakeholders involved in the decision-making process. This can lead to decisions for political incentives rather than what is best for the project.
Another challenge is that P3 contracts are typically long-term, so getting out of a deal that later becomes disadvantageous can be challenging.
Finally, because P3 projects are often large and require heavy private-sector financing, there is a high risk of cost overruns and schedule delays.
Public-private partnership validation
Despite their challenges, many public authorities and private partners continue to use PPPs to procure infrastructure and services. The following are some of the justifications given to validate the need for PPPs.
- Value for money. The value for money test compares P3 private-partner bids to a hypothetical public sector comparable bid intended to represent the costs of a completely public option.
- Risk transference. P3s are often justified based on risk transfer from the public to the private sector. P3s are assumed to be able to transfer more risks to the private sector than traditional procurement because P3 partners have an incentive to minimize these risks to maximize their profits.
- Innovation. P3s are also seen to encourage innovation, since private partners are typically more agile and have more experience with new technologies than the public sector.
- Off-balance-sheet accounting. P3s can also be used to keep infrastructure projects off the public-sector balance sheet, therefore allowing them to achieve more of their goals without incurring additional costs.
See also: corporate activism, public data, benefit corporation, procurement plan, risk mitigation, risk avoidance, residual risk, ICANN.
