
cloud service provider (cloud provider)
What is a cloud service provider?
A cloud service provider, or CSP, is a company that offers components of cloud computing -- typically, infrastructure as a service (IaaS), software as a service (SaaS) or platform as a service (PaaS).
Cloud service providers use their own data centers and compute resources to host cloud computing-based infrastructure and platform services for customer organizations. Cloud services typically are priced using various pay-as-you-go subscription models. Customers are charged only for resources they consume, such as the amount of time a service is used or the storage capacity or virtual machines used.
For SaaS products, cloud service providers may host and deliver their own managed services to users. Or they can act as a third party, hosting the app of an independent software vendor.
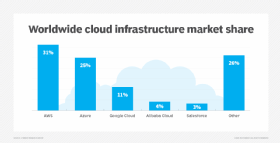
The most well-known cloud service platforms are Amazon Web Services (AWS), Google Cloud (formerly Google Cloud Platform or GCP) and Microsoft Azure.
What are the benefits and challenges of using a cloud service provider?
Using a cloud provider has benefits and challenges. Companies considering using these services should think about how these factors would affect their priorities and risk profile, for both the present and long term. Individual CSPs have their own strengths and weaknesses, which are worth considering.
Benefits
- Cost and flexibility. The pay-as-you-go model of cloud services enables organizations to only pay for the resources they consume. Using a cloud service provider also eliminates the need for IT-related capital equipment purchases. Organizations should review the details of cloud pricing to accurately break down cloud costs.
- Scalability. Customer organizations can easily scale up or down the IT resources they use based on business demands.
- Mobility. Resources and services purchased from a cloud service provider can be accessed from any physical location that has a working network connection.
- Disaster recovery. Cloud computing services typically offer quick and reliable disaster recovery.
Challenges
- Hidden costs. Cloud use may incur expenses not factored into the initial return on investment analysis. For example, unplanned data needs can force a customer to exceed contracted amounts, leading to extra charges. To be cost-effective, companies also must factor in additional staffing needs for monitoring and managing cloud use. Terminating use of on-premises systems also has costs, such as writing off assets and data cleanup.
- Cloud migration. Moving data to and from the cloud can take time. Companies might not have access to their critical data for weeks, or even months, while large amounts of data are first transferred to the cloud.
- Cloud security. When trusting a provider with critical data, organizations risk security breaches, compromised credentials and other substantial security risks. Also, providers may not always be transparent about security issues and practices. Companies with specific security needs may rely on open source cloud security tools, in addition to the provider's tools.
- Performance and outages. Outages, downtime and technical issues on the provider's end can render necessary data and resources inaccessible during critical business events.
- Complicated contract terms. Organizations contracting cloud service providers must actively negotiate contracts and service-level agreements (SLAs). Failure to do so can result in the provider charging high prices for the return of data, high prices for early service termination and other penalties.
- Vendor lock-in. High data transfer costs or use of proprietary cloud technologies that are incompatible with competitor services can make it difficult for customers to switch CSPs. To avoid vendor lock-in, companies should have a cloud exit strategy before signing any contracts.
Types of cloud service providers
Customers are purchasing an increasing variety of services from cloud service providers. As mentioned above, the three most common categories of cloud-based services are IaaS, SaaS and PaaS.
- IaaS providers. In the IaaS model, the cloud service provider delivers infrastructure components that would otherwise exist in an on-premises data center. These components include servers, storage, networking and the virtualization layer, which the IaaS provider hosts in its own data center. CSPs may also complement their IaaS products with services such as monitoring, automation, security, load balancing and storage resiliency.
- SaaS providers. SaaS vendors offer a variety of business technologies, such as productivity suites, customer relationship management software, human resources management software and data management software, all of which the SaaS vendor hosts and provides over the internet. Many traditional software vendors sell cloud-based versions of their on-premises software products. Some SaaS vendors will contract a third-party cloud provider, while other vendors -- usually larger companies -- will host their own cloud services.
- PaaS providers. The third type of cloud service provider, PaaS vendors, offers cloud infrastructure and services that users can access to perform various functions. PaaS products are commonly used in software development. In comparison to an IaaS provider, PaaS providers will add more of the application stack, such as operating systems and middleware, to the underlying infrastructure.
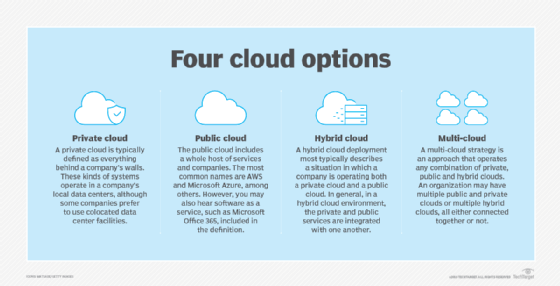
Cloud providers are also categorized by whether they deliver public cloud, private cloud or hybrid cloud services.
Common characteristics and services
In general, cloud service providers make their offerings available as an on-demand, self-provisioning purchase. Customers can pay for the cloud-based services on a subscription basis -- for example, under a monthly or quarterly billing structure.
Some cloud service providers differentiate themselves by tailoring their offerings to a vertical market's requirements. Their cloud-based services might deliver industry-specific functionality and tools or help users meet certain regulatory requirements. For instance, several healthcare cloud products let healthcare providers store, maintain, optimize and back up personal health information. Industry-specific cloud offerings encourage organizations to use multiple cloud service providers.
Major cloud service providers and offerings
The cloud services market has a range of providers, but AWS, Microsoft and Google are the established leaders in the public cloud market.
Amazon was the first major cloud provider, with the 2006 offering of Amazon Simple Storage Service. Since then, the growing cloud market has seen rapid development of Amazon's cloud platform, as well as Microsoft's Azure platform and Google Cloud. These three vendors continue to jockey for the lead on a variety of cloud fronts. The vendors are developing cloud-based services around emerging technologies, such as machine learning, artificial intelligence, containerization and Kubernetes.
Other major cloud service providers in the market include the following:
- Adobe
- Akamai Technologies
- Alibaba Cloud
- Apple
- Box
- Citrix
- DigitalOcean
- IBM Cloud
- Joyent
- Oracle Cloud
- Rackspace Cloud
- Salesforce
How to choose a cloud service provider
Organizations evaluating potential cloud partners should consider the following factors:
- Cost. The cost is usually based on a per-use utility model, but all subscription details and provider-specific variations must be reviewed. Cost is often considered one of the main reasons to adopt a cloud service platform.
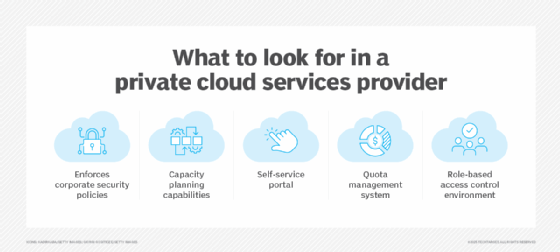
- Tools and features. An overall assessment of a provider's features, including data management and security features, is important to ensure it meets current and future IT needs.
- Physical location of the servers. Server location may be an important factor for sensitive data, which must meet data storage regulations.
- Reliability. Reliability is crucial if customers' data must be accessible. For example, a typical cloud storage provider's SLA specifies precise levels of service -- such as 99.9% uptime -- and the recourse or compensation the user is entitled to should the provider fail to deliver the service as described. However, it's important to understand the fine print in SLAs, because some providers discount outages of less than 10 minutes, which may be too long for some businesses.
- Security. Cloud security should top the list of cloud service provider considerations. Organizations such as the Cloud Security Alliance offer certification to cloud providers that meet its criteria.
- Business strategy. An organization's business requirements should align with the offerings and technical capabilities of a potential cloud provider to meet both current and long-term enterprise goals.
For more on cloud service providers and their offerings, check out our guide on the top public cloud providers.






