availability bias
What is availability bias?
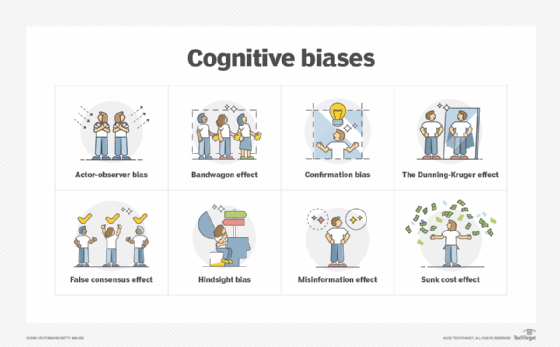
In psychology, the availability bias is the human tendency to rely on information that comes readily to mind when evaluating situations or making decisions. Because of this bias, people believe that the readily available information is more representative of fact than is the case. The availability bias -- also known as the availability heuristic -- is just one of a number of cognitive biases that hamper critical thinking and, as a result, the validity of our decisions.
The availability bias is a cognitive shortcut that relies on what immediately comes to mind to make quick decisions and judgments. The information might be derived from recent or particularly vivid memories. It might also be based on personal experience or fueled by outside sources such as news outlets or the internet. Relying on this information helps people avoid laborious fact-checking and analysis, but it increases the likelihood that their decisions will be flawed.
What are examples of the availability bias?
The Catalogue of Bias offers a formal definition of availability bias: "A distortion that arises from the use of information, which is most readily available, rather than that which is necessarily most representative." The Catalogue of Bias is both an organization and effort that is compiling a list of biases based on the work of David Sackett. His 1979 paper "Bias in Analytic Research" served as the first draft of a "catalog of biases which may distort the design, execution, analysis, and interpretation of research."
As an example of the availability bias, the Catalogue of Bias points to the work of researchers at Erasmus University in Rotterdam. In the study, they assessed whether first- and second-year medical interns tended to base their diagnoses on recent clinical experiences, rather than on analytic reasoning. It turned out that second-year interns were more likely to make diagnostic errors consistent with availability bias than first-year interns who based their assessments on those recent experiences. However, subsequent reflective reasoning tended to improve diagnostic accuracy for both first- and second-year residents.
Naturally, people recall recent vivid memories most quickly. However, there are a few factors that influence how well they remember things. Most people tend to recall details that they observed more easily than information they only heard about. For example, individuals who know of several successful startups are more likely to overestimate the percentage of startups that succeed, even if they have read statistics to the contrary.
Similarly, people remember vivid events like plane crashes over more common incidents such as car crashes, despite the much greater number of auto accidents. As a result, they often overestimate the likelihood that a plane will crash and might even choose to drive rather than fly, although they're much more likely to get into an accident on the road.
Availability bias can also play a role in decisions such lottery purchases. The sensational images of a relatively few lottery winners and their lavish lifestyles lead many people to purchase lottery tickets even if they can't afford them. That's because they believe that their chances of winning are much higher than the actual statistics bear out.
Other cognitive biases include the confirmation bias and self-serving bias. With the confirmation bias, people tend to give undue credence to materials that support their own beliefs and attitudes, disregarding any information that contradicts those perceptions. With the self-serving bias, people are more likely to put a positive spin on their own activities and interpret ambiguous data in a way that suits their own purposes, often at the expense of others.
Cognitive biases can lead to erroneous judgments and poor decisions. When carried out at a group level, they can have disastrous consequences. Awareness of these patterns is one of the first steps required to improve critical thinking.
See also: backfire effect, machine learning bias, cognitive diversity, fudge factor, reality check