project scope
What is project scope?
Project scope is the part of project planning that involves determining and documenting a list of specific project goals, deliverables, tasks, costs and deadlines. The documentation of a project's scope is called a scope statement or terms of reference. It explains the boundaries of the project, establishes responsibilities for each team member and sets up procedures for how completed work will be verified and approved.
During the project, this documentation helps the project team remain focused and on task. The scope statement also provides the team with guidelines for making decisions about change requests during the project. Note that a project's scope statement should not be confused with its charter; a project's charter simply documents that the project exists.
Effective scope management requires good communication. That ensures everyone on the team understands the extent of the project and agrees upon exactly how the project's goals will be met. As part of scope management, the team leader should ask for approvals and signoffs from stakeholders as the project proceeds, ensuring that the proposed finished project meets everyone's needs.
The importance of defining a project's scope
Writing a project scope statement that includes information on the project deliverables is a first step in project planning. The benefits a project scope statement provides to any organization undertaking a new initiative include the following:
- Articulates what the project entails so that all stakeholders can understand what's involved.
- Provides a roadmap that managers can use to assign tasks, schedule work and budget appropriately.
- Helps focus team members on common objectives.
- Prevents projects, particularly complex ones, from expanding beyond the established vision.
Establishing project scope ensures that projects are focused and executed to expectations. The scope provides a strong foundation for managing a project as it moves forward and helps ensure that resources aren't diverted or wasted on out-of-scope elements.
Managing project scope in Agile environments
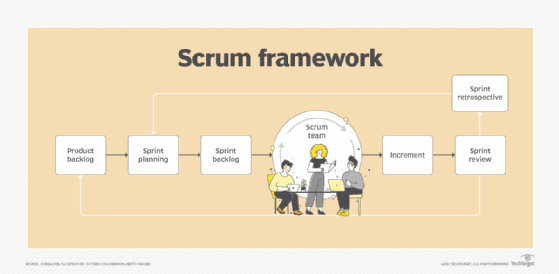
In Agile environments, project scope management takes a more dynamic approach, where flexibility and adaptability are prioritized. Unlike traditional methods that define the entire project scope at the outset, agile methodologies like Scrum and Kanban allow for iterative scope definition.
As the project progresses through sprints or iterations, the scope is regularly reviewed and adjusted based on stakeholder feedback and project team insights. This continuous refinement process helps ensure that the project remains aligned with business goals and can adapt to changing requirements or market conditions.
How to define the scope of a project
Defining project scope requires input from the project stakeholders. They work with project managers to establish the key elements of budget, objectives, quality and timeline.
To determine scope, project managers must collect requirements for what the stakeholders need from the project. This includes the following elements:
- The project's objective and deliverables.
- When the project must be completed.
- How much the stakeholders can pay for it.
The goal is to gather and record precise and accurate information during this process, so the project scope reflects all requirements. Doing this improves the chances for project leaders to deliver products that meet stakeholder expectations on time and on budget.

The role of project management software in scope management
Project management software and tools play a crucial role in defining, tracking and managing project scope. For instance, Jira is widely used in Agile projects to manage tasks, sprints and backlogs, facilitating real-time scope adjustments.
Tools like Asana help teams organize and track tasks and milestones, providing clear visibility into the project scope and progress. Microsoft Project is suited for traditional project management approaches and offers comprehensive features for planning, monitoring and controlling project scope, schedule and resources.
Utilizing these tools enhances accuracy, transparency and collaboration in scope management, leading to more successful project outcomes.
Integration of project scope with other management processes
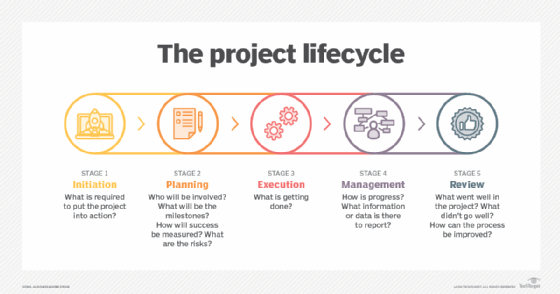
It's important to note that project scope is inherently connected to other project management processes, including schedule, cost, quality and resource management. A well-defined project scope lays the foundation for developing a realistic project schedule and budget, ensuring quality standards are met and allocating resources efficiently.
Effective scope management provides a roadmap for executing the project, where adjustments in scope directly influence project timelines, costs, resource allocation and quality outcomes.
This holistic view of project management ensures that changes in one area are reflected and managed across all aspects of the project, maintaining alignment with project objectives and stakeholder expectations.
Stakeholder involvement in scope definition and management
As mentioned above, stakeholders play a critical role in defining and managing project scope. Their diverse expectations and priorities must be carefully balanced to define a scope that is feasible and aligned with business objectives.
Engaging stakeholders early in the project planning process, through requirements gathering sessions and regular reviews, ensures that their needs are understood and integrated into the project scope. Transparent communication and negotiation are essential to manage differing priorities and to secure stakeholder buy-in, which is crucial for project success.
Writing a project scope statement
A project scope statement is a written document that includes all the required information for producing the project deliverables. It is more detailed than a statement of work; it helps the project team remain focused and on task. The scope statement also provides the project team leader or facilitator with guidelines for making decisions about change requests during the project.
The project scope statement establishes what is not included in its initiatives, either implicitly or explicitly. Objectives and tasks not listed in the scope statement should be considered out of scope. Project managers can also list specific work that will not be part of the project.
As such, this statement establishes the boundaries of a project. Project leaders must take those requirements and map what should happen and in what order those items should occur. This leads to the creation of a work breakdown structure (WBS). The WBS breaks down planned work into smaller, defined portions and required tasks.
A well-articulated scope statement is a critical part of effective project management. Project scope should be determined for every project, regardless of what project management method is used. Stakeholders for the project should review the project scope statement, revise it as necessary and approve it.
Once the project scope statement is completed and approved, project managers can assign tasks and give their teams directions on what they need to do to meet the target timelines, budget and goals.
Scope planning and management
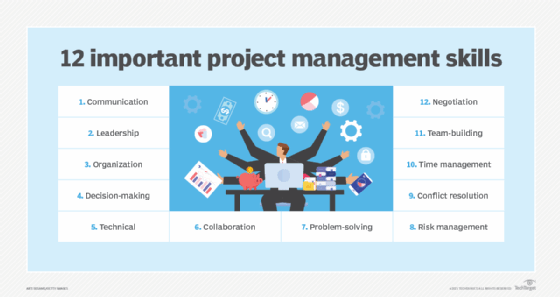
Updates and changes are part of the project management process. As work progresses, managers must carefully control what changes are made to the project scope and document them. This requires strong project management skills.
The change management process also requires that project managers and stakeholders adhere to the project scope statement. They must recognize what elements are within the project scope and what requests are out of scope.
Change management processes help project managers determine how to evaluate requests for updates and alterations to the project. Distinguishing between needed requests and ones that are out of scope enables organizations to avoid scope creep.
Scope creep is when more work is tacked onto a project while it is underway. It can add costs and unnecessary work, while distracting from the objectives and threatening the quality of the intended deliverables.
Regularly reviewing the project's progress against its defined scope and objectives helps identify potential scope creep early, allowing for timely corrective actions. This strategic approach to scope and change management ensures that the project remains on track and delivers the expected outcomes.
Project scope example
Scope statements attempt to provide key stakeholders with all the information they'll need. The following are some elements that should be included in a scope statement:
- Introduction. This defines the what and why of a project. An example would be "This content creation and marketing project is being undertaken by the company RealContent Inc. to distribute articles on its blog and social media sites to raise brand awareness and increase traffic to the website."
- Project scope. This defines the project requirements. It sets the general goals for the project schedule and tasks and identifies who will be involved. In the content creation example, it might state: "The project will include research, writing, content strategy and search engine optimization, and publishing on the company's website and social media profiles, in March of 2021. John Smith, RealContent content director, will oversee these tasks. Staff and contract writers will create the deliverables."
- Deliverables. The deliverables section defines what will be provided at the end of the project and specifies a submission date. In our example, "Deliverables for the project will include a well-researched, 2,000-word article to be delivered no later than Feb. 28, 2021. Ten related and linkable articles, expanding on points in the main article, will be delivered on that same deadline."
- Acceptance criteria. This describes the project objectives and the metrics that will be used to assess success. For example, "The main article will gain 3,000 cumulative pageviews within six months of publication and generate two new leads."
- Exclusions. This describes what will not be included in the project. For example, "The project will not need the creation of multimedia to go with the articles."
- Constraints. This lists hard limits of the project and things that cannot be changed. Project constraints may pertain to the project schedule, project budget or technical issues. For example, "The project has a hard submission date of Feb. 28, 2021, and a firm budget of $5,000."
Project scope vs. product scope
Project scope should not be confused with product scope. Product scope defines the capabilities, characteristics, features and functions of the deliverables at the end of the project.
Project leaders should create a separate product scope statement. They should use both the project scope and the product scope statements to support each other and establish a clear understanding of what every project aims to achieve.
Defining project scope is an important step in project planning and management. Before a project begins, project managers need to understand what the scope of the project is to determine what must be done and what falls outside of the project.
Project scope is defined in the scope statement, a document that provides the objectives, schedules, tasks and deliverables of a project. Scope statements align stakeholders' expectations and give projects a framework for success.
Once a project is underway, it is important to keep it on track and within scope. Various project management tools and strategies are available to help teams do that. Also, project, program and portfolio management are related but represent distinct disciplines. Learn about the responsibilities and goals of each as well as how they differ.







