template
What is a template?
A template is a form, mold or pattern used as a guide to make something. Here are some examples of templates:
- Website design
- Creating a document
- Knitting a sweater
While the dictionary definition of a template is pretty straightforward, there are a number of use cases for templates.
They can be a physical object, such as a paper template that is used to cut out pieces of fabric, but they can also be a digital template, such as a file that opens in a design program like Photoshop.
Why are templates beneficial?
Using a template is beneficial because it can help you create something quickly and efficiently, from a pattern or standard operating procedure (SOP) that has been successful in the past.
Creating a template can save you time in the long run because you won't need to start from scratch each time you want to make something new.
It can also ensure that your final product is consistent and of high quality.
Examples of template use cases
Let's take a deeper look at some of the numerous applications for templates.
- Documents. Document templates typically contain placeholder text or a standard layout that should be repeated for each new file created. Thus, the template allows users to reuse certain standard section of text and simply fill in the variable parts rather than create an entirely new document every time.
- Website design. With a general design template, users can then change the color scheme, images and text to create a unique website without starting from scratch.
- Programming flowcharts. In programming, a template can be used to create Unified Modeling Language (UML) diagrams like activity diagrams, class diagrams and sequence diagrams. There is also the Standard Template Library for object oriented computing languages, such as the Microsoft Foundation Class (MFC) Library from which programmers can choose individual template classes to modify.
- Material patterns. Templates are often used in woodworking, sewing and other physical crafting projects to ensure that pieces are cut out of materials correctly.
Where can you get templates?
Users can purchase or download premade templates for website design, document creation and more, with a simple Google search. Or, users can create their own template to use repeatedly.
In certain cases where the template is highly specialized, users may need to hire a professional to create it for them or purchase the rights to use the templates.
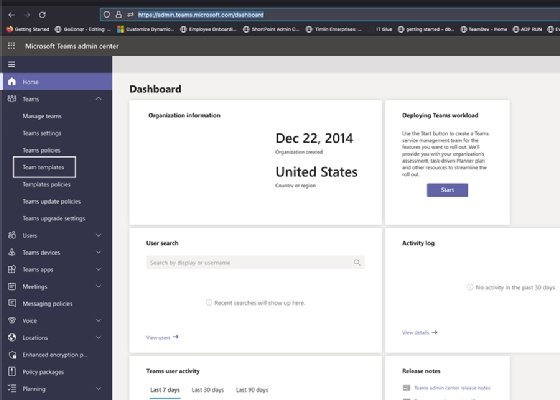
Often, business software includes templates for common marketing documents and other administrative tasks. A good example is Microsoft Word template, of which there are numerous templates to choose.
How to choose the right template
When choosing or creating a template, there are a few things to keep in mind:
- Prioritize templates for heavy volume, repeatable tasks or where specifications are needed.
- The template should be easy to use and understand.
- It should be flexible enough to be used for multiple purposes.
- The template should be designed for the intended audience.
- The template should be compatible with the software you're using.
See video example below for a template on how to build a disaster recovery plan:
Some sample templates:
- customer service email templates;
- remote access security policy template;
- free business impact analysis (BIA) template;
- an incident response plan template;
- cybersecurity impact analysis template;
- IT risk assessment template;
- data storage policy with guidelines template;
- complete crisis management guide and free template;
- free IT disaster recovery plan template and guide;
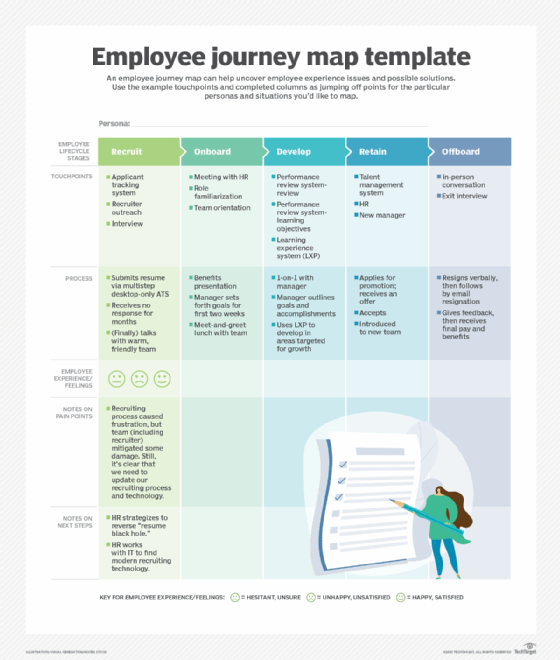
- how to design an employee journey map (with template);
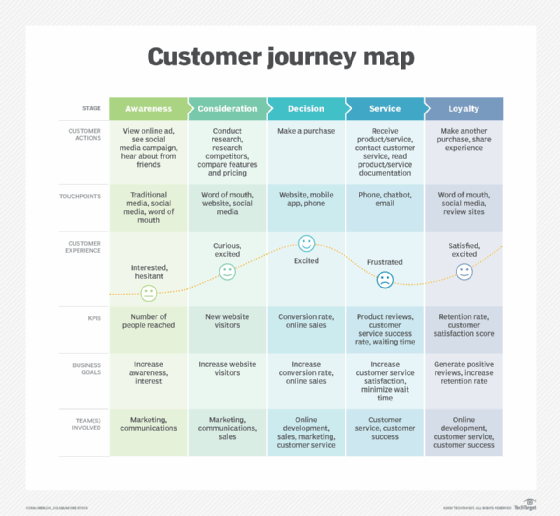
- how to create a customer journey map -- with template;
- free business continuity plan template and guide; and
- how to create and deploy a VMware VM template.
