commodity hardware
What is commodity hardware?
Commodity hardware in computing is computers or components that are readily available, inexpensive and easily interchangeable with other commodity hardware. Almost all PCs use commodity hardware. The term is most used for general-purpose servers that can be used in any role. Commodity hardware is synonymous with off-the-shelf hardware. It is contrasted with proprietary, custom or bespoke hardware.
In the early days of computers, almost all computers were proprietary. The hardware, operating system (OS) and application software were designed by the same company and sold together. Often, software for one system would not work on other systems.
As computer technology matured, standards were developed for software and hardware. This enabled software from any vendor to run on hardware from any other vendor. This standardization and interchangeability led to most computer hardware becoming a commodity.
A commodity is considered a physical item that is fungible. Fungible means that one item is interchangeable with another, regardless of its origin or manufacturer. An example of a fungible commodity is coal. One ton of coal is equivalent to any other ton of coal, regardless of where it was mined. Often, commodity prices are determined by market forces.
Commodity hardware in PCs
Almost all PCs are commodity hardware. All PCs that use Microsoft Windows are basically functionally equivalent. For example, many businesses buy computers from a major manufacturer, such as Dell, Lenovo or Hewlett Packard. If another manufacturer were to offer greatly lower prices, the business could buy those computers instead with relative ease.
An example of non-commodity hardware computers are Apple computers running macOS. No other manufacturer can produce and sell macOS computers, so they must be purchased from Apple.
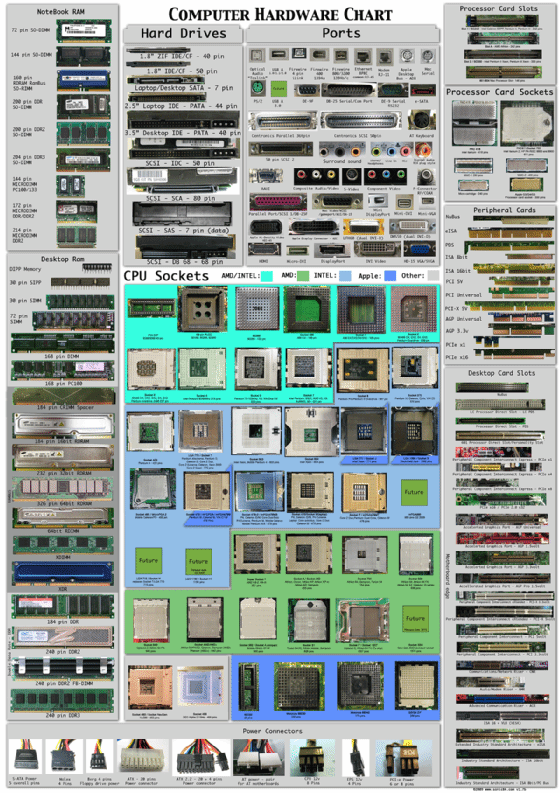
Many components of PCs are considered commodity hardware. Cables, hard drives and RAM are example components that are available from a variety of manufacturers and are easily interchangeable. These are said to be plug and play.
Commodity hardware in servers
Commodity hardware is mostly used in reference to servers. Certain server types are proprietary or only run on certain hardware. For example, IBM z/OS and related applications do not run on commodity hardware. Windows Server, Linux and Open Source software can run on commodity hardware.
Most servers used today are commodity servers. The growth of virtualization, containerization and cloud computing have made most server roles hardware-agnostic. These workloads can be easily shifted to run on the most cost-effective platform. Orchestration services can be used to run a service on thousands of commodity servers from different manufacturers.
The ability to run on commodity hardware is an important consideration when planning a high-performance computing (HPC) environment. Many HPC and supercomputer installations use proprietary hardware. This may result in high costs, and as the equipment ages, it may not be possible to replace failed nodes.
Commodity hardware-based HPC can utilize almost any available computer hardware. It can use equipment from different vendors and heterogeneous configurations. This results in lower costs and the ability to build out the compute power over time.
Apache Hadoop is a popular big data platform that can run on commodity hardware. This enables a Hadoop cluster to be created cheaply and to scale out easily over time.
Commodity hardware in networking equipment
Certain network equipment is considered commodity hardware. Some systems benefit from having a unified proprietary ecosystem. For example, an organization may use Cisco routers and access points to benefit from central management. In other areas, it may be better to use commodity hardware for cost savings, such as edge switches, fiber optic interfaces and patch panels.
Advantages and disadvantages of commodity hardware
There are several advantages and disadvantages to using commodity hardware.
Advantages
- Lower cost. Compared to proprietary systems.
- No vendor lock-in. Can switch between providers based on cost or availability.
- Highly available. Readily available from a variety of vendors and resellers.
Disadvantages
- Lower overall performance. Tightly integrated proprietary systems can offer greater performance per watt or capacity per unit of floor space.
- More difficult to troubleshoot. Using different hardware from different providers can lead to edge cases or obscure behavior that can be difficult to identify and resolve.
- Less support. Fully integrated stacks are fully supported top to bottom by the vendor. Commodity hardware only has limited support provided by the original equipment manufacturer.
Explore seven major server hardware components you should know.