social media marketing (SMM)
What is social media marketing?
Social media marketing (SMM) is a form of internet marketing that uses social media apps as a marketing tool.
These social media platforms enable brands to connect with their audience to:
- build a brand;
- increase sales;
- drive traffic to a website; and
- build a community of followers to share and engage with content.
Producing relevant content that users will share with their own networks helps brands increase their exposure. It also extends their reach toward fans, potential customers and even potential employees when used as a recruitment tool.
Social media marketing also enables organizations to get customer feedback while making the company seem more personable. Social media enables organizations to create relationships with their audience. It gives end users a platform to ask questions, voice complaints and generally be heard. It also gives brands the opportunity to respond, adapt and adjust business processes or products.
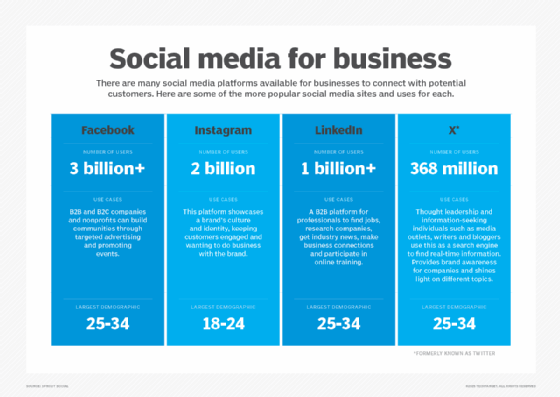
Some popular social media apps include Facebook, Twitter, LinkedIn, YouTube, Pinterest, Instagram and Snapchat. Each platform has elements that makes it attractive to use. And when a company uses several in combination to deliver a multichannel message, consumers can see those messages on their preferred channels.
Learn how to craft a multichannel marketing strategy here.
5 pillars of social media marketing
When developing marketing programs, one key area that marketers care about is how to deliver their messaging. Social media helps spread those messages to the right people at the right time, through both free and paid means. Social media also enables brands to learn more about their audience's personal, geographic and demographic information. This enables organizations to customize their messaging and content for the best engagement.

There are five pillars of social media marketing that will lead to a successful program.
1. Social strategy
With any marketing campaign or activity, an appropriate strategy should be laid out in advance. Organizations need to determine the goals of the program, the channels that will be used and what types of content will be shared. Here are some examples:
- Determine goals. Using social media for marketing should align closely with business and other marketing program goals. Some goals that businesses can use to measure success include increasing brand awareness, driving website traffic and leads, and increasing revenue.
- Select social media platforms. There are many social platforms available, but it doesn't make sense for businesses to use them all. Organizations need to know their audience and choose the platform(s) that best fit their demographic.
- Content mix. Each social platform has a unique flavor for distributing content -- including video, imagery, links and direct messaging. So brands need to identify which content their marketing persona is most likely to engage with.
2. Planning and publishing
After establishing a strategy, it is time to begin publishing. This can be as simple as posting a new blog post, sharing information about an upcoming event or posting a new product video. But being consistent is the key to an effective SMM program. To build an audience, organizations should post frequently to their page. Posting relevant content consistently will keep the audience coming back for more.
Content that organizations post to social media should align with other marketing promotions. Tools such as Hootsuite, HubSpot and Sprout Social enable marketers to schedule their posts at the appropriate time.
3. Listening and engagement
Businesses that create activity on social platforms can see growth in interaction and conversations about the brand and products. Users will comment on and share posts, tag the company in their own posts, and even begin communicating through the instant messaging functionalities. These types of interactions are ideal because there are notifications in place to alert social media managers. This enables them to practice good customer service, which in turns boosts the customer experience.
People on social media may also discuss a brand, product or service without tagging or speaking directly to a company. There are several social media listening tools available to stay plugged into the conversation, such as Brandwatch, NetBase Quid and Sprinklr. Free tools such as Google Alerts can also notify marketers when their company is being mentioned.
4. Analytics and reporting
As more content is published and the audience expands, it is a good idea to continuously measure performance. Questions to ask include the following:
- Which posts are getting the most engagement?
- Where are a brand's followers from?
The success of any marketing program is dependent on its data and analytics outputs. A marketing team can use this information to make more informed decisions on future campaigns and take advantage of what works.
Each social platform has its own analytics data, but there are other tools that can collect data from many channels into one location. This enables marketers to evaluate the overall success and failures of their marketing campaigns.
5. Advertising
Much of social media marketing is free -- with the exception of resource time and specialized tools. Building an audience and publishing content on free social media sites is a great way to achieve marketing goals, but as the program grows, so does the budget.
Paid marketing features can be very valuable to organizations. They can target their advertisements at audiences based on many factors, including demographic information, retargeting and behaviors.
There are tools to help manage social media marketing at volume, but using the native ads functionality to begin is enough to promote posts, capture leads and ensure messages get in front of the right audience.
Advantages and disadvantages of social media marketing
Social media marketing has embedded itself into every organization's sales and marketing roadmap. It is an additional channel to distribute content and messaging to a significantly larger audience than a homegrown database of contacts.
While there are advantages to rolling out a social media marketing program, there are disadvantages as well.
Advantages of social media marketing
- Reach a wider audience. There are more than 3.6 billion users across all social media channels. A single post share can exponentially increase brand exposure.
- Improved customer satisfaction. Organizations don't just market to customers on social media, they also interact with them. This can improve customer service and create one-to-one relationships.
- Cost-effective tool. When executed correctly, the cost of managing a social media program can be low. Once the knowledge, team and program strategy are in place, marketing teams find it easy to use with very little overhead.
- Increase website traffic. Social posts are a great way to drive traffic back to a brand website. Promoting blog content, landing page offers and more can entice users to click through and engage further with a brand.
- Gain better insights. Using the analytics and reporting features from each social media platform gives insight into who page followers are, what content they are interested in and how they like to engage with a brand.
Disadvantages of social media marketing
- Time-consuming process. A lot of time can be spent on social media campaigns to ensure they are effective. Marketing teams also need to constantly fill the calendar with new content and respond to inquiries. This can make it difficult for small marketing teams to tap into the full capabilities of SMM.
- Need qualified resources. It takes the right person or team to run a social media marketing program. Social media marketing programs don't benefit from entry-level employees. Instead, skilled and seasoned social media marketers are key.
- Have to wait to see ROI. SMM is a long-term investment. Social media platforms yield a high ROI, but not in the form of immediate results. The success of an SMM program isn't determined by one piece of content, but rather several over long periods of time.
- Competitor's market research. Posting to social media is a public forum and everyone can see the content, including the competition. There is no workaround for this.
- Brand reputation is vulnerable. SMM can open a brand for public embarrassment and bad press. Negative reviews can be plentiful as customers take to social media to vent frustrations. And because of the public nature of the platforms, anything a company says or does will be seen and reacted to. Brands should expedite response times to mitigate this risk.
How to create a social media marketing strategy
Here are the steps a company needs to take to build an effective social media marketing strategy:
1. Identify social media goals that align to the business goals
Start by setting goals that will act as not only a guide for how to use social media, but also a benchmark of data to measure against. Use a SMART goal format to find out what is realistic to accomplish. Examples of goals include the following:
- increase traffic to website
- drive more leads
- increase revenue
- grow audience
2. Research and define the target audience
It's important to know who the target market is, what they care about and why they need a company's products or services. Social media platforms are rich with data about users, so this exercise can be done without a substantial market research project. Knowing demographic information and who follows the social channel are great starting points.
It's also important to know that different platforms attract different users. Knowing what social channels a company's target audience is on enables them to choose which channels to invest time and resources into.
3. Perform a competitive assessment
Knowing what the competition is doing enables marketing teams to identify what is working well and what is not for the competition. This provides industry insights as well as opportunities to bring a product or message to market.
Social listening tools can also help brands set up different monitoring streams for competitive content and industry keywords.
4. Create and curate relevant content for the channel
Knowing the goals, audience and competitive landscape will help determine the type(s) of content that brands need to create. Engaging content comes in different forms and media. It can be company generated, curated from elsewhere to share industry news or other thought leadership pieces.
Businesses should publish content frequently and consistently to develop an engaged follower base. Brands can post promotions to increase engagement. They can also create posts that show a more relatable and human side to the organization.
5. Be timely with posts and responses
Posting when convenient for a business isn't always convenient for customers. Taking advantage of the best times to post for engagement is information that can be collected from analytics. Then organizations can schedule posts ahead of time using available publishing tools. Timeliness of the content is also important as the news cycle moves fast.
Another element of being timely on social media is response time. If customers engage with a brand on social media, they also expect a quick reply. A brand can build authority and respect with its clientele through these one-to-one relationships.
6. Gain buy-in and support from others in the organization
Marketing departments need to engage other departments and stakeholders within an organization. Marketing can learn a lot from sales to inform future social campaigns, but sales can also benefit from marketing's reach. Sales and marketing alignment is great, but senior stakeholder support is also a necessity.
Supporting other departments' efforts is a common sign of a strong social media program. Every department in a company can benefit from social support, but HR is usually the next best place to partner with. Social media can be a recruitment tool and brand builder for prospective employees.
7. Measure and optimize
The last element of building a successful social media marketing program is to measure what works and what doesn't. Organizations should monitor the following:
- posts that get top engagement;
- followers that continue to buy; and
- ads that yield the highest ROI.
Businesses that benefit from social media marketing
Organizations that roll out an effective social media marketing campaign will see many benefits. Here are some examples of businesses that can benefit from social media marketing programs:
Small businesses and startups
Social media marketing is a great tool for small businesses and startups. It is a way for new businesses to build some awareness around their offerings. Using social media to sell products and services to a new market can be an entryway into building a customer base.
Direct sales companies
These types of businesses are very entrepreneurial and grow through communities. And social media can help build communities, tapping into friends, family and beyond.
These started out as Tupperware and Mary Kay parties in homes. But social media apps are paving the way for new waves of direct sales companies such as LuLaRoe and Thirty-One Gifts. Party hosts no longer must host parties in their homes. Instead, they can host virtual parties using social media apps where consultants are able to show off their wares.
Real estate
Real estate companies benefit from social media by promoting open houses and showcasing images of properties for sale. Features such as Facebook Live and Instagram stories show video footage of these properties in digestible formats for users to consume.
B2B companies
B2B marketing teams are better able to identify who their target prospects are -- and when done correctly -- can show up in the right person's newsfeed.
The data presented about users on social media platforms helps paint a picture of who the audience is. And using the social media advertising tools, businesses can get the right message in front of that decision-maker at the right time.
