
C-Level (C-Suite)
What is a C-level executive?
C-level, also called the C-suite, is a term used to describe high-ranking executive titles in an organization. The letter C, in this context, stands for "chief," as in chief executive officer and chief operating officer.
Officers who hold C-level positions are typically considered the most powerful and influential members of an organization; consequently, these executives set the company's strategy, make high-stakes decisions and ensure day-to-day operations align with fulfilling the company's strategic goals. They are also typically the highest-paid people in a company.
C-level executives must have strong leadership and communication skills, as well as team-building abilities. C-suite executives set the direction of the function they oversee and then hire staff to ensure the daily management is aligned with the established plans and policies. Because C-level executives work at a highest level within their departments, they typically do not engage in day-to-day management tasks. However, C-level executives at small and medium-sized businesses or startup companies might take on some management duties.
C-level executive roles and responsibilities
The number of positions and the kinds of titles within the C-suite vary from company to company. The variation reflects the different sizes of companies, with larger companies often having more executive positions to distribute the correspondingly large workload. Variations reflect each organization's missions and maturity. While a healthcare company, for example, needs a chief medical officer, a company focused on developing cutting-edge products might want to have a chief innovation officer.
This article is part of
The evolving CIO role: From IT operator to business strategist
It's important to note, too, that positions within the C-suite may change over time. Some positions have evolved with business needs and have become widely accepted; the chief information officer role has evolved in the past several decades as businesses seized on technology -- first, to automate processes for efficiencies and cost-savings and, now, to transform the services they offer and how they are delivered.
Essential skills for C-level executives
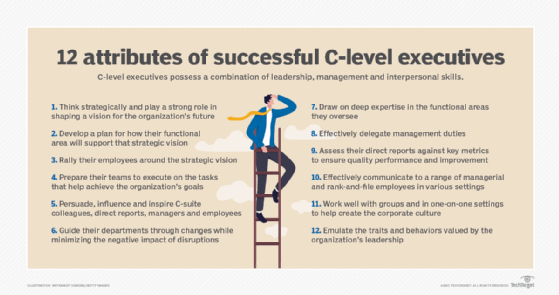
Successful C-level executives have a combination of leadership, management and interpersonal skills.
In general, these leaders have the ability to do following:
- think strategically and play a strong role in shaping a vision for the organization's future;
- develop a plan for how their functional area will support that strategic vision;
- rally employees around the strategic vision;
- prepare their teams to successfully execute on tasks that will move their organizations toward that future state;
- persuade, influence and inspire their C-suite colleagues, direct reports, managers and employees to make incremental and big improvements;
- guide their departments through changes while minimizing the negative impact of disruptions;
- draw on deep expertise in the functional areas they oversee;
- effectively delegate management duties;
- assess their direct reports against key metrics to ensure quality performance and improvement over time;
- effectively communicate to a wide range of both managerial and rank-and-file employees in various settings;
- work well with groups and in one-on-one settings to help create the corporate culture; and
- emulate the traits and behaviors valued by the organization's leadership.
Examples of C-level executive job titles
Chief executive officer (CEO). The CEO is responsible for the success or failure of the organization, overseeing the entire operation at a high level. The CEO implements plans and policies to ensure the successful management of the business and sets future strategies. The CEO hires the other executives in the C-suite and can fire those who do not perform to set standards. As such, the CEO is the boss of all the other executives.
Chief operating officer (COO). The COO is generally second in command to the CEO and might also sit on the board of directors along with the CEO. The COO oversees the organization's day-to-day operations on behalf of the CEO, creating the policies and strategies that govern operations. The COO is often responsible for the human resources function within an organization as well.
Chief financial officer (CFO). As the title suggests, the CFO oversees the organization's financial affairs, which includes developing annual budgets, managing cash flow and overseeing finance reporting and compliance.
Chief marketing officer (CMO). The CMO oversees the organization's marketing strategy. This includes advertising, brand management and market research. Responsibilities can also include newer duties driven by advances in technologies, such as overseeing a company's business intelligence initiatives and mobility strategy. Some CMOs also have broadened their responsibilities to act as the voice of the company's customers.
Chief information officer (CIO) and chief technology officer (CTO). In the past, these titles were almost interchangeable, given to the individual tasked with running the organization's information systems. Now, these roles are increasingly used to describe different functions and roles. The CTO most commonly has oversight for the information systems that run the enterprise's operations, as well as the technologies that drive the business. The CIO is usually the executive who manages research and development, oversees the development of technologies into products and services, and ensures that all IT initiatives are aligned with business goals.
Chief human resources officer (CHRO). The CHRO is in charge of an organization's human capital management. The CHRO's most important task is to set up and enable a company's talent strategy, which encompasses acquisition, development and succession planning.
Chief compliance officer (CCO). The CCO is in charge of managing and overseeing all compliance issues within an organization. A CCO's most important duties are ensuring that the company complies with regulatory requirements and employees comply with internal policies and procedures.
Chief security officer (CSO) or chief information security officer (CISO). The CSO or CISO is tasked with ensuring data and systems security. In general, a CSO is responsible for physical as well as digital security, while a CISO is only in charge of digital security.
Chief data officer (CDO) or chief digital officer (CDO). A chief data officer is tasked with overseeing an organization's data governance. A chief digital officer may also be responsible for helping the business to aggregate and digitize the data required to demonstrate compliance.
Other examples of C-level job positions
Some C-suite positions are fairly uncommon, appearing only briefly, in certain industries or in only a handful of companies. Such positions often fade away unceremoniously when responsibilities are folded into other positions. They include:
Chief analytics officer (CAO). The CAO is responsible for data analysis within an organization.
Chief experience officer (CXO). The CXO ensures positive interactions with an organization's external customers.
Chief green officer (CGO). The CGO is tasked with all aspects of making an organization environmentally friendly. This includes energy-efficient construction, e-cycling and e-waste mitigation, recycling, LEED compliance, meeting OSHA standards and clean production.
Chief IT architect (CITA). The CITA is responsible for solving integration problems and syncing technology frameworks across the organization's business units. Depending upon the organization, the chief architect may oversee and coordinate the efforts of other technology-specific architects, including the chief security architect, the chief data architect, the chief mobile architect and the chief cloud architect.
Chief knowledge officer (CKO). The CKO is responsible for gathering, organizing, sharing and analyzing an organization's knowledge in terms of resources, documents and people skills.
Chief learning officer (CLO). The CLO ensures that a company's corporate learning program and strategy supports its overall business goals.
Chief medical information officer (CMIO). The CMIO serves as the bridge between medical and IT departments at a healthcare organization.
Chief privacy officer (CPO). The CPO is charged with developing and implementing policies designed to protect employee and customer data from unauthorized access.
Chief process and innovation officer (CPIO). The CPIO is responsible for identifying parts of a company's business processes that could be improved and recommending specific ways to make them work better.
Chief procurement officer (CPO). The CPO is responsible for the strategic acquisition of goods and services.
Chief reputation officer (CRO). The CRO is charged with overseeing activities in all areas of an organization that could potentially have an impact on the public perception of that enterprise.
Chief risk officer (CRO). The CRO is tasked with assessing and mitigating significant competitive, regulatory and technological threats to an enterprise's capital and earnings.
Chief social scientist (CSS). The CSS is charged with developing policies that ensure a good work environment for employees while maintaining economic profitability for the company as a whole.
Chief strategy officer (CSO). The CSO is charged with helping formulate, facilitate and communicate an organization's plans for the future.
Chief trust officer (CTO). The CTO is responsible for building confidence around the use of customer information.
Corporate executive compensation
The U.S. Bureau of Labor Statistics put median annual executive pay for 2020 at $107,680.
The average annual salary for CEOs as of April 2021 was $148,709, according to ZipRecruiter.
At the same time Salary.com put the annual median executive salary at $203,034, noting that pay typically falls between about $181,000 and $241,000 annually.
C-level executives typically receive the highest compensation within an organization. Pay varies greatly, depending on the size of the company, revenue, market performance and other factors.
Compensation can range from $100,000 up to millions of dollars annually; it can also involve stock options and high-end perks -- from signing bonuses to loan forgiveness to use of a corporate plane.
A 2020 analysis from the Economic Policy Institute, a think tank based in Washington, D.C., found that compensation for CEOs at the top 250 firms averaged $21.3 million in 2019. EPI calculated CEOs at these firms earn 320 times the average pay for typical workers.
How to become a C-level executive
The number of executive positions in the United States is expected to grow about 4% over the next decade, according to the Bureau of Labor Statistics. The category is predicted to total 2,889,300 positions in 2029, up from 2,774,300 C-suite positions in 2019, a gain of 115,000 jobs. Federal researchers said that's as fast as the average for all occupations.
Not surprisingly, competition for those leadership roles is fierce.
Executive search firms look for candidates who have been successful at other levels of management or in their existing C-level roles. Industry experience and management experience are essential for climbing the corporate ladder and advancing to the C-suite; experience in talent management and product management are also important for attaining a C-level position.
Would-be executive officers must demonstrate most (if not all) of the skills typically associated with those corporate titles, but they often also need to market themselves as experts and thought leaders.
Although executives generally have at least a bachelor's degree, some famous corporate titans do not. Facebook CEO Mark Zuckerberg; the late Steve Jobs, co-founder of Apple; former Microsoft CEO Bill Gates; Virgin Group CEO Richard Branson and Vogue editor-in-chief Anna Wintour are among the top executives without college degrees.
Executives without degrees are the exception, however, and in fact most executive officers and senior managers have advanced degrees, frequently MBAs.
Additionally, they're often skilled in a functional area -- such as technology, in the case of CIOs -- as well as in management and business.
Furthermore, successful executive officers often have held senior management positions in more than one line of business and sometimes even at companies in various industries to broaden their levels of experience.
People who get to be C-level executives also typically build relationships with executive search firms, as well as cultivate an extensive professional network upon which to draw when looking to land their next C-suite position.





