gig economy
What is the gig economy?
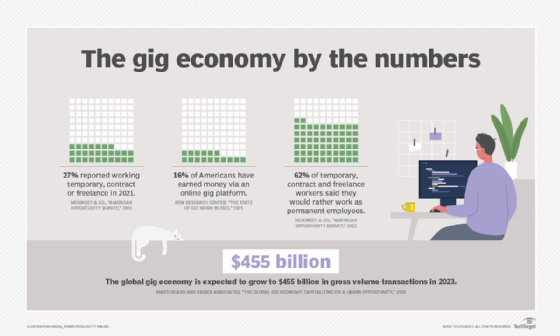
A gig economy is a free market system in which temporary positions are common and organizations hire independent workers for short-term commitments. The term "gig" is a slang word for a job that lasts a specified period of time. Traditionally, the term was used by musicians to define a performance engagement.
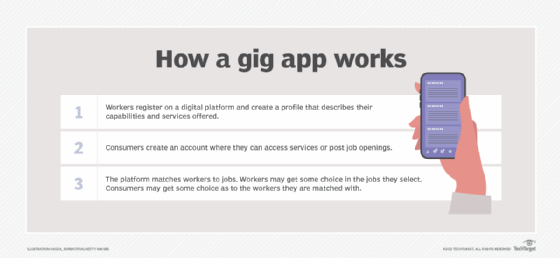
Examples of gig workers include freelancers, independent contractors, project-based workers and temporary or part-time hires. Gig apps and digital technology are often used to connect customers and gig workers.
The gig economy is a recent trend, with a number of factors contributing to its rise. The two most important factors are the following:
- The workforce has become more mobile.
- Work is increasingly done remotely via digital platforms.
As a result, jobs and locations are being decoupled. That means freelancers can take a job or project with an employer anywhere in the world. At the same time, employers can select the best person for a specific project from a larger pool than is available in any given area.
The gig economy is part of a shifting cultural and business environment that also includes the sharing economy, gift economy, barter economy and more flexible jobs. The cultural impact of the gig economy continues to change; for example, the COVID-19 pandemic has had a significant effect on hiring trends.
Who is part of the gig economy?
The gig economy is made up of companies, workers and consumers. All gig workers aren't the same. They include the following:
- freelancers who get paid per task;
- independent contractors who perform work and get paid on a contract-to-contract basis;
- project-based workers who get paid by the project;
- temporary hires who are employed for a fixed amount of time; and
- part-time workers who work less than full-time hours.
The gig economy provides consumers with an alternative to commercial products and industries. They turn to the gig economy for convenience, better service or both. This is the case with ride-hailing apps, like Uber, and food delivery services, like Grubhub. Gig apps have also met consumer demand where a service is in short supply or expensive. This is a role Airbnb has played in places where hotel rooms are in short supply, making more temporary accommodations available, sometimes at lower prices.
Common gig economy jobs and industries
Gig economy jobs include familiar positions found in diverse industries, including the following:
- Accounting and finance. Independent consultants and mortgage representatives.
- Administration. Administrative assistants.
- Art and design. Musicians or graphic designers.
- Construction. Carpenters and other construction trades.
- Education. Substitute instructors and tutors.
- Freelance writing. Content writers and copywriter jobs.
- Information technology. Various jobs, such as information security engineers and network analysts.
- Media and communications. Technical writers and photographers.
- Project management.Project or office manager jobs.
- Software development. DevOps engineers and user experience
- Transportation. Ride-hailing drivers.
Perks of the gig economy
The benefits of the gig economy vary, depending on whose perspective you take -- the business, worker or consumer.
The business
In a gig economy, businesses save money and resources. They aren't responsible for providing employee benefits, such as sick leave and health insurance, and they often don't have to provide workers with office space, equipment and training. A gig model also enables a business to contract with experts, who might be too expensive hire as full-time staff, for specific projects.
The worker
From the worker's perspective, a gig economy can improve work-life balance compared with many traditional jobs. Independent workers are able to select freelance jobs that they are interested in, that provide new opportunities, and that look right for their preferences and schedule. They don't get stuck in a full-time job that doesn't interest them or have the flexibility they need. This sort of freelance economy also lets workers choose when they want to work and helps them avoid being locked in to or dependent on a single employer.
The consumer
Consumers often find a gig model provides more choices and convenience in personal services offered. In many cases, services are higher quality and offered at lower prices. Services are also offered more flexibly, and there are more choices in service providers, as well as times and locations of offerings.
Issues with the gig economy
Despite all the advantages, the gig economy has considerable downsides, including the following:
- Lack of benefits. This may be the biggest downside. Gig workers are typically not eligible for health insurance or other benefits they would get working as a full-time employee. Companies also are typically not required to pay temporary workers minimum wage or overtime.
- Work-life management challenges. Gig work can be disruptive if the worker isn't used to making their own schedule. Inexperienced workers can easily take on too many gigs, leading to overwork and burnout.
- Insecurity and inconsistent income. Having enough work to maintain a stable income is a challenge with gig work.
- Work culture. Temporary workers who come and go in an organization make it difficult to maintain consistent relationships among workers, employers and clients on a long-term basis.
- Effect on the job market. When temporary positions are all that are available, workers can find it difficult to establish and develop their careers.
What impacts the gig economy?
Shifting political, cultural and business environments affect the gig economy.
For example, changing government regulations and company policies around the employment status of gig workers -- who is considered a full-time employee versus an independent contractor -- can alter the gig workforce. A full-time worker may be eligible for certain benefits and a base level of pay that an independent contractor would not automatically receive.
One example of this is California's Assembly Bill 5 (AB5), which became law in January 2020. It required companies to reclassify independent contractors as employees. Later that year, California voters approved Proposition 22. It allowed app-based ride and delivery service drivers to remain independent contractors, overriding AB5. Legal challenges are currently working their way through the courts.
The pandemic and the gig economy
In 2020, the gig economy began changing due to COVID-19. The University of Chicago's Harris School of Public Policy and The Associated Press-NORC Center for Public Affairs Research conducted a survey in 2020 on consumer attitudes toward ride-hailing and delivery services. The survey found a divided user base.
Americans with higher incomes were more likely to use delivery services to reduce their risk of infection. The survey found that 26% of households with incomes of $100,000 or more a year have increased their use of these services, while only 12% of those with incomes under $50,000 have done so.
Among customers who previously used ride-hailing services, 63% said they had not used the service since March 2020, and 54% said they feel uncomfortable using a ride-hailing service during the COVID-19 outbreak.
Some other factors that have affected gig work and work in general include the following:
- Digitization. AI and other automated technologies have had a significant effect on the job market. In some cases, digitization has decreased jobs available as software replaces some types of workers, such as customer experience and content automation workers.
- Flexibility needs. Other influences have increased the pressure on organizations to hire more gig workers. These include financial pressures on businesses, leading to the need for a more flexible workforce that can be expanded or contracted quickly.
- Generational effects. Younger workers, such as millennials and Gen Zers, also tend to change jobs more frequently than older, more traditional workers. The gig economy is part of that trend.
- COVID-19. The pandemic has also put pressure on many businesses and organizations to remain visible and solvent. The growing digital marketplace and the gig economy have helped there. For example, some traditional brick-and-mortar restaurants, needing to provide contactless delivery, have added food-delivery apps, like DoorDash, in the last two years.
Virtual-only restaurants have also emerged out of the gig economy. For example, MrBeast Burger is a virtual-only restaurant that operates out of existing restaurant kitchens but is only available via food delivery services. These virtual businesses, sometimes called ghost kitchens or cloud kitchens, also enable existing restaurants to test new menu items without affecting their original brand.