inductor
What is an inductor?
An inductor is a passive electronic component that temporarily stores energy in a magnetic field when electric current flows through the inductor's coil. In its simplest form, an inductor consists of two terminals and an insulated wire coil that either loops around air or surrounds a core material that enhances the magnetic field. Inductors help to handle fluctuations in an electric current running through a circuit.
When an electric current flows through a conductor such as copper wire, the current generates a small magnetic field around the wire. If the wire is shaped into a coil, the magnetic field becomes much stronger. If the wire is coiled around a central core made up of a material such as iron, the magnetic field grows stronger still -- this is essentially how an electromagnet works. The magnetic field completely depends on the electric current. Changing the electric current also changes that field.
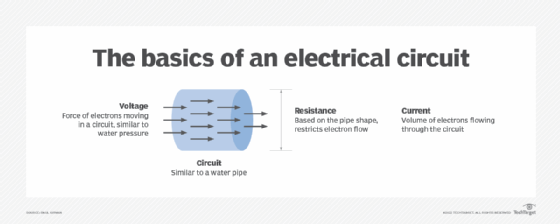
Inductors use the relationship between the electric current and magnetic field to compensate for changes in the current's flow. When the current begins to pass through the inductor's coil, the magnetic field starts to expand until it finally stabilizes. Until then, the coil inhibits the flow of current. After the magnetic field stabilizes, the current flows through the coil normally.
energy is stored in the magnetic field as long as the current continues to run through the coil. When the current stops flowing, the magnetic field starts to collapse, and the magnetic energy is converted back into electrical energy, which continues to flow into the circuit until the magnetic field completely collapses.
Inductors and inductance
If the flow of current remains in a steady state, the current passes through the inductor just like any wire, without any reaction on the part of the inductor. However, if there are sudden changes in the current, the inductor tries to resist them.
An inductor always lags behind changes to the current because of its magnetic field. When the current changes, the inductor's magnetic field changes -- increasing if the current increases, decreasing if the current decreases. Changes in the magnetic field cause changes to the magnetic flux, which in turn induces an electromagnetic field (EMF) that tries to oppose the change in current. If the current decreases, the EMF attempts to increase it. If the current increases, the EMF attempts to decrease it.
The inductor's ability to resist changes to the current is referred to as its inductance, which is the ratio of voltage to the current's rate of change within the coil. The standard unit of inductance is the henry (H). Because the henry is such a large unit, many inductors are measured in smaller quantities, such as the millihenry, abbreviated mH (1 mH equals 10-3 H), and the microhenry, abbreviated µH (1 µH equals 10-6 H). Occasionally, the nanohenry (nH) is used (1 nH equals 10-9 H).
Many factors can affect an inductor's level of inductance, including the number of coils, the length of the coiled wire, the material used for the core, and the size and shape of the core. If no core is used, then inductance also depends on the radius of the coil.
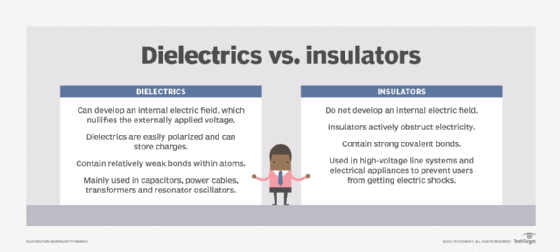
For a given coil radius and number of turns, air cores, or those without solid cores, offer the least inductance. Materials such as wood, glass and plastic -- known as dielectric materials -- are essentially the same as air in terms of inductance. Ferromagnetic substances such as iron, laminated iron and powdered iron increase the inductance. In some cases, this increase is on the order of thousands of times. The shape of the core is also significant. Toroidal or donut-shaped cores provide more inductance for a given core material and number of turns than solenoidal or cylindrical cores.
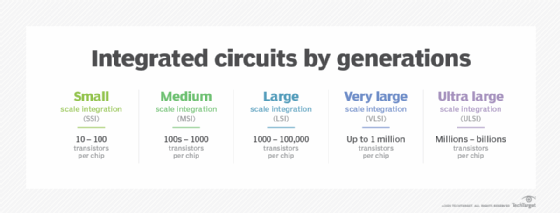
Fabricating inductors onto integrated circuit (IC) chips can be difficult, but it can be done, although they have a fairly low inductance. When inductors can't be used, resistors can be substituted. In some cases, inductance can be simulated by using transistors, resistors and capacitors fabricated onto IC chips.
Inductors are used with capacitors in wireless communications, audio systems and a wide range of other applications. An inductor connected in series or parallel with a capacitor can help filter out unwanted signals. Large inductors are used in the power supplies of electronic equipment of all types, including computers and their peripherals. In these systems, inductors help to smooth out the rectified utility alternating current (AC) power, providing pure, battery-like direct current (DC) power.
See also: electromagnetic induction, electric permittivity, electric grid, volt per meter, dielectric constant, ultracapacitor, transducer, picofarad per meter, coulomb, Ohm's Law, clean electricity, volt-ampere, impedance, susceptance and resistance.
