iterative DNS query
What is iterative DNS query?
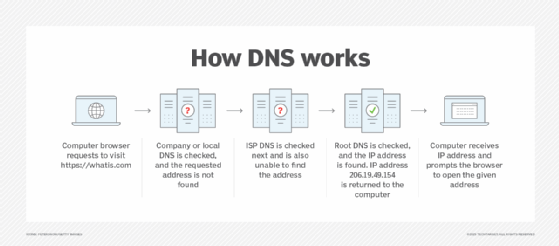
An iterative DNS query is a request for a website name or URL. However, with this query type, the domain name system (DNS) server does not fetch the complete answer for the query. Rather, it provides a referral to other DNS servers that might have the answer. Thus, if the queries server does not have the IP address requested, it forwards it to another DNS server until the answer is found.
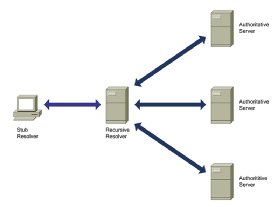
There are primarily three types of DNS queries, depending on how a request is processed. Two common queries are recursive and iterative. In a recursive query or lookup, one DNS server communicates with many DNS servers to find an IP address and return it to the requesting client. It is similar to a client saying, "Find the IP address for this domain and don't get back to me until you do."
In contrast, in an iterative DNS query the client communicates directly with each DNS server. This approach is analogous to the client telling the DNS resolver to provide the address of the next DNS server in the lookup process so the client can pursue the IP address on their own. Iterative DNS queries are also known as nonrecursive DNS queries.
Iterative requests are used to return information from servers that aren't always able to sustain the workload of performing start-to-finish query responses. This could be a DNS server for a domain that is prioritizing traffic to its sites or to root hints or an authoritative server that must maintain availability.
How an iterative DNS query works
An iterative DNS query responds directly to the client with an address for another DNS server. The client queries each DNS server in an iterative manner until one of them finds and fetches the correct IP address for the requested domain.
The DNS server responds to iterative queries that have no local information through "referral." The referral points to a DNS server that is authoritative on a domain namespace and those for lower levels of a domain space. The referrals continue until a DNS server is found that is authoritative to the queried site (and can therefore reveal its IP address) or until an error is returned or a time out is reached.
Here's how iterative queries work:
In this example, the DNS server is 172.16.200.30.
Step 1. The client enters www.techtarget.com into the browser and hits Enter. A DNS query for the IP address (a record) is sent by the operating system's resolver to the DNS server.
Step 2. The DNS server receives the query and starts looking through its tables (cache) to find the IP address for www.techtarget.com. However, the entry does not exist in its tables.
Step 3. In a recursive query, the DNS server would query the root server for the answer. But because this is an iterative query, the DNS server will reply with a referral to a root server. The resolver will then query the root server for the IP address.
These three steps are repeated until the IP address is found and delivered to the client.
Iterative DNS queries vs. recursive DNS queries
In a recursive query, the client only sends the request to the first DNS server. If the server cannot answer, it will send the request to the next server. The process continues until the query is resolved. The reply to the query can be an answer (IP address) or an error message.
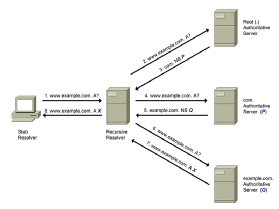
In an iterative query, the DNS server does not query another server for the IP address. Instead, it provides the client with a referral to a DNS root server. The referral could be to a lower-level DNS server that is delegated to be "authoritative" for the DNS namespace related to the DNS query. After getting the referral from the higher-level DNS server, the DNS client sends a DNS query to the lower-level DNS server.
It is the client's responsibility to send the query to successive servers for resolution. The query will be resolved when it hits a server that is authorized for the domain name. Other possible outcomes are an error or a timeout. In this case, it is the job of the local OS resolver to find the answer from the referral provided. That said, if the queried higher-level DNS server has the IP address, it will fetch it for the client and no further queries will be required.
Iterative requests are made by both iterative DNS servers and recursive DNS servers. The requests made by recursive servers to other DNS servers are iterative. At the level of root DNS, all servers are iterative because they are the end of the line. The availability of root servers is crucial to the proper functioning of the internet.
Learn about DNS server troubleshooting for Linux and Windows, and explore ways to best secure DNS.
