moonshot
What is a moonshot?
In technology, a moonshot is an ambitious, exploratory and groundbreaking project undertaken without the assurance of near-term profitability or benefit and, perhaps, without a full investigation of potential risks and benefits.
Moonshot projects have the significant potential to benefit humanity since they rely on ambitious moonshot thinking, experimentation and the "fail fast" philosophy. Tech companies of different sizes and from different industry sectors have adopted the moonshot approach to tackle huge problems affecting humanity.
The term moonshot is derived from the Apollo 11 spaceflight project, which landed the first human on the moon in 1969. The term originally meant "long shot," in which the likelihood of great results is low, but people still make an effort hoping for such an outcome anyway. It may also reference the earlier phrase "shoot for the moon," which means to aim for a lofty target.
Today, moonshot refers to a new project that could have outstanding results after one intense, consistent effort. With potential benefits ranging from the creation of technologies essential for harnessing the continuous explosion of data to curing the most devastating illnesses to furthering the development of the metaverse, the moonshot concept is increasingly used to describe a giant leap -- i.e., an innovative project -- colossal effort, and an ambitious and lofty goal in the technology arena. If the goal is realized, the benefits could be huge for the project's stakeholders, end users and humanity as a whole.

Advantages of moonshot thinking
Moonshot thinking refers to an approach of choosing a huge, seemingly insurmountable problem and proposing a radical solution to that problem using disruptive technology. The idea is not to look for small, incremental improvements, but to aim for a huge improvement or, even better, solve the problem completely.
This kind of new-age thinking benefits business and other disciplines in the following ways:
- It empowers people to look for unconventional solutions with a high probability of success.
- Teams can use fast-paced experimentation to continuously learn and improve.
- The organization looks past established ways of doing things and assumes that everything is possible.
- It removes the fear of failure and helps teams focus on success.
Technology companies are investing more in moonshots that address some of the world's greatest problems. Alphabet, parent company of Google, defines a moonshot as a project or proposal that does the following:
- addresses a huge problem that affects millions or billions of people;
- proposes a radical solution that may seem impossible today; and
- uses breakthrough technology that may help create the solution in just five to 10 years.
At X Development -- formerly, Google X and a now a subsidiary of Alphabet -- the aim is to make a 10x impact on some of the world's biggest problems, rather than achieving a 10% improvement. In many ways, aiming for 10x instead of 10% has become synonymous with the idea of moonshot thinking.
In addition to the focus on 10x, moonshot thinking at Alphabet and Google also incorporates the following principles:
- Fall in love with the problem, and gain a deep understanding of it.
- Touch base with the real world, and test in the field as often as possible.
- Bring together diverse teams to generate creative connections and spark great ideas.
- Tackle the hardest tasks first.
- Fail fast, and embrace learning.
- Become a chaos pilot to embrace uncertainty and benefit from it.
- Create prototypes early for testing and experimentation.
- Shift your perspective to discover answers and apply insights in fresh ways.
- Focus on long-term goals.
Technologies with moonshot potential
A Bank of America (BofA) Global Research report titled "To the Moon(shots)! -- Future Tech Primer" identifies 14 groundbreaking technologies on which moonshots are focusing:
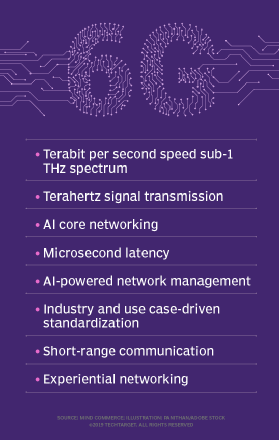
- 6G with 1 terabyte per second download speeds will be necessary to succeed 5G to address the rapidly escalating amounts and complexity of data; by 2028, global data capacity will be beyond the capabilities of 5G. According to the BofA Global Research report, "6G will offer 10-50x higher speeds and bandwidth compared with 5G, with a much better latency ratio (up to 1/1000)."
- Brain-computer interfaces, which combine human and machine intelligence, are in use to help cure cognitive and physically debilitating illnesses; future application of BCIs could change human interaction with computers or smartphones, or the technology could be used where robots controlled by humans work in dangerous environments.
- Emotional artificial intelligence (AI) is also referred to as affective computing and cognitive computing. According to BofA, emotional AI can "potentially collect, analyze and respond to completely new varieties of data and situations and predict or simulate human thought, leading people to take action."
- Synthetic biology entails redesigning organisms to give them enhanced capabilities. Using elements of molecular biology, genomics, chemistry, engineering, machine learning and computer science, synthetic biology taps into "the vast diversity of nature to make biomolecules that traditional chemistry cannot," the BofA report explained.
- Immortality, could it be possible? Human life could be extended, thanks to advances in health, biotech and anti-aging drugs.
- Bionic humans could be possible as a result of technology, such as exoskeletons, biohacking -- increasing performance by making adjustments to the brain and body -- and implants, that extends human abilities.
- Electric vertical takeoff and landing vehicles are a new class of light commercial aircraft that can take off and land vertically. These electric-powered vehicles, which can be used for passengers and cargo, could provide an alternative means of transportation in crowded urban areas.
- Wireless electricity employs magnetic fields or radio waves for the wireless charging of devices. This can provide near-continuous charging needed as the internet of things continues to grow, as well as a charging solution for electric vehicles and electricity for remote communities.
- Holograms are a next-generation media technology that will take the metaverse -- a 3D version of the internet in which people can interact using virtual reality -- a step further. New uses for holograms, such as for conferencing and cyberspace collaboration, will require 6G development because high-speed networking will be needed to display holograms on smartphones.
- Metaverse, which means "beyond the universe," refers to a "future iteration of the internet" composed of "3D-shared spaces linked into a virtual universe," the BofA report stated. "It could comprise countless persistent virtual worlds that interoperate with one another, as well as the physical world and transforming markets such as gaming, retail, entertainment, etc."
- Next-gen batteries will need greatly increased capacity to store energy and charge rapidly and cost-effectively. For electric vehicles, solid-state, vanadium flow and sodium ion batteries are alternatives to today's lithium batteries.
- OceanTech focuses on products that work in or use the ocean. Ocean energy, land-based aquaculture and precision fishing using AI are alternatives for tapping the ocean's benefits, while increasing its sustainability.
- Green mining, such as deep-sea mining (in which mineral deposits are retrieved from the deep sea), agromining (in which plants extract metal from soil) and mining of wastewater, could help sharply reduce toxins released into the atmosphere, protect natural lands and habitats, and improve worker safety.
- Carbon capture and storage (CCS) technology captures and stores carbon dioxide before it is released into the atmosphere. This is accomplished through the "separation of carbon dioxide to form a concentrated stream of CO2," the BofA report explained. "This stream is then compressed, transported and stored."
These future technologies have the potential to show an average compound annual growth rate of 36% to become a $6 trillion market by the 2030s, according to the BofA Global Research report.
"Leftfield technologies will be needed to tackle immense global challenges," the report stated. "Could 5G be unable to handle the exponential growth in data by the end of the decade? Then, 6G will need to be rapidly deployed in just 5-6 [years]. … Is health the new wealth post-COVID? Then, bionic humans, brain-computer interfaces and synthetic biology could all take us a step further towards the holy grail of 'immortality.'"
Examples of moonshot projects
One of the best recent examples of a moonshot project from Alphabet, Google and X is the self-driving car. With this moonshot, Google aimed to create an autonomously driven vehicle that requires little or no human input. Even though it seems like a lofty and impossible goal, Google is steadily working toward it by creating an electronically powered prototype equipped with highly sensitive sensors and cutting-edge software to operate, navigate and control the vehicle.
Other moonshots under development at X include the following:
- Mineral. Developing robotics, sensing and other technologies to build a more sustainable, resilient and productive food system and reduce food insecurity.
- Tidal. Improving underwater camera systems and machine perception tools to improve visibility into ocean ecosystems, expand ocean farming and meet humanity's growing protein needs.
- Everyday Robots. Creating affordable, user-friendly, general-purpose robots that can eventually help humans with everyday tasks in all kinds of unstructured environments, like homes and offices.
- Taara. Expanding global access to fast internet through narrow, invisible light beams that transmit information at super-high speeds.
- Tapestry. Developing new computational tools to accelerate the global transition to a resilient, carbon-free electricity grid.
For Google and others in the industry, moonshots that didn't work out as planned proved to be a learning experience. One example is the company's much-heralded 2013 launch of Google Glass, a wearable, hands-free device that enabled users to access the internet and many applications using voice commands. Still in the development stage, the device was too costly for the mass consumer market, and early users pointed to some problems, including privacy concerns.
Although Google halted the Glass project in 2015, it later resumed work on the technology with Glass Enterprise Edition aimed at businesses, particularly in the medical, manufacturing and logistics fields. Additionally, other augmented reality products, such as Snap Spectacles and Pokemon Go, later proved popular for the consumer market.
Other early Google moonshoots included Project Loon, aimed at expanding internet access using stratospheric balloons; Project Calico to combat aging and related diseases; and Google Neural Machine Translation, which uses an artificial neural network to increase the fluency and accuracy of Google Translate results.
For many deep-pocketed technology companies, the moonshot approach is one part of their overall innovation strategy. While Amazon's moonshots include lofty goals, such as the use of machine learning to prevent and cure cancer, the company's innovation strategy includes a blend of its moonshot projects with process improvements to handle everyday challenges, such as improving delivery, for example, using automated robots, implementing shelving refinements, and other means of enhancing order accuracy and customer experience.
Large companies, including the likes of Google, Amazon, Intel and IBM, as well as niche players, have invested time and money in health-related moonshots. The U.S. government also is playing a role in healthcare-related moonshots.
In 2016, the U.S. White House and then-Vice President Joe Biden announced that it planned to spend $1.8 billion on the Cancer Moonshot project to accelerate scientific discovery in cancer research, foster greater collaboration among researchers and improve data sharing. The overarching goal was to accelerate the rate of progress in humanity's fight against cancer.
In 2022, President Biden and Vice President Kamala Harris announced the reignition of the Cancer Moonshot project. This time, the overarching goal is highly quantitative: to reduce the cancer death rate in the United States by at least 50% over the next 25 years.
Another organization with health-related moonshots is venture capital and health technology firm StartUp Health, which launched its Alzheimer's Moonshot, an effort to coordinate resources and funding programs to eradicate the disease.
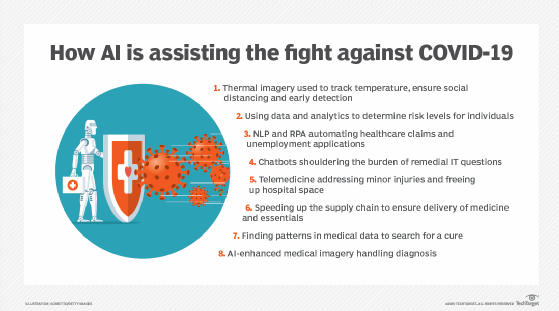
Also in healthcare, research projects for COVID-19 vaccines and antiviral medicines were considered moonshots. One effort on this front is the COVID Moonshot, a nonprofit collaboration of scientists focused on discovering safe, easily manufactured and affordable antiviral drugs to combat SARS-CoV-2 and other viral pandemics. More than 150 scientists participated in this moonshot to crowdsource, model and evaluate ideas for molecular compounds.
Companies in the aeronautics and space business are also proponents of moonshot thinking. A notable example is SpaceX, an aerospace company that aims to make humans a multiplanetary species. In 2020, a SpaceX commercial spacecraft called Dragon carried astronauts to the International Space Station for a long-duration stay.
Others focused on commercial space travel, including Blue Origin and Virgin Galactic, have moonshot projects that aim to create a new tourism sector by offering trips to outer space. Also focused on space are 3D printers for zero gravity created by startup Made In Space, whose goal is to make things for space for use in space.
Weighing moonshots' advantages and disadvantages
By definition, moonshots are well-informed bets in which companies take a chance on markets or technologies that may not take off. If they do, however, the rewards to society and to industry can be significant. Despite their potential, moonshots are risky, costly and time-consuming, and they can sap resources. Though key to businesses' innovation culture, moonshots are not for the faint of heart or the weak of wallet.
Companies often must weigh the need to concentrate on short-term solutions that enable them to grow revenue and attract customers against the inherent qualities of moonshots -- costly, potentially world-changing efforts that may be an instant success or may not bear fruit for years, if ever. On the plus side, benefits can be derived from failure -- learning that a product might not be ready for the consumer market but could make a splash in that same space later or may have other near-term applications. Finally, with the pace of technology transformation accelerating, not pursuing a moonshot that could yield stellar results is risky.
See also: SkunkWorks project, disruptive innovation, digital disruption and digital transformation.