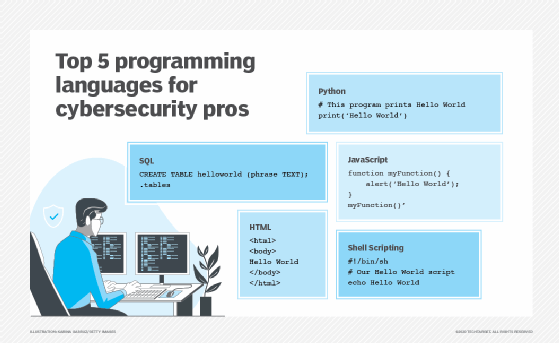
5 essential programming languages for cybersecurity pros
Coding is an important skill across almost every technology discipline today, and cybersecurity is no exception. Learn about the top programming languages for security professionals.
Coding is an essential skill across almost every technological discipline today, and cybersecurity is no exception. Cybersecurity professionals must understand coding concepts in order to correctly interpret the activity of malicious actors on their networks, and they must be able to write code to perform their own work more efficiently and effectively. While not every cybersecurity job explicitly includes coding skills as a job requirement, it's hard to imagine any cybersecurity career that wouldn't benefit from the ability to knock out at least a few lines of code every once in a while.
Cybersecurity pros who want to learn coding for the first time face a somewhat daunting question: Which language should they learn? There are dozens of popular programming languages in use today, and choosing a starting point can be an overwhelming task. There are five that I consider important elements of the modern cybersecurity toolkit:
- Python.
- Shell scripting.
- HTML.
- JavaScript.
- SQL.
Let's take a look at each of these important programming languages, examining why you need them and how to learn them.
1. Python
Why you need it. Python is the modern workhorse of programming languages. As a member of the group of languages known as general-purpose languages, you'll find that you can accomplish almost any software development task in Python, and for this reason, it's incredibly popular. If you're only going to learn one language, this is definitely the place to start. Python code lays beneath the surface of many popular cybersecurity tools, and it's easy to use Python to automate much of your work.
How to learn it. The best way to learn Python is a combination of tutorial and example. I'd recommend starting with a basic Python tutorial, such as those available from LearnPython.org or Codecademy. From there, start looking at some Python code written by others. Perhaps there are some examples in your own working environment, or you might try writing a Python script that works with a common cybersecurity tool, such as Nmap.
2. Shell scripting
Why you need it. Shell scripting uses many of the same commands that you might already use in terminal sessions on your operating system of choice and enables developers to write automated scripts to accomplish many routine tasks. Need a quick way to provision accounts and authorize appropriate access? Looking for a way to quickly automate the security lockdown of a system configuration? Shell scripting is the place to look. If you're using a Linux or Mac OS, you'll want to learn one of the Linux shell scripting languages, such as Bash. If you're a Windows pro, dive into PowerShell scripting.
How to learn it. If you're ready to learn shell scripting, the first thing to do is make sure that you're comfortable with the basic command-line tools available for your OS. From there, you can start stringing together some basic scripts by following the examples in common tutorials on Linux shell scripts or PowerShell.
3. HTML
Why you need it. I cheated a little bit here. HyperText Markup Language (HTML) isn't strictly a programming language. Technically speaking, it's a markup language. But it's the language used to create webpages across the internet. HTML is an essential skill for cybersecurity professionals because so many attack types revolve around HTML code. If attackers want to write a SQL injection attack or embed a malicious script in a website, they'll do it using HTML. If you want to be able to analyze those attacks, you'll need to understand HTML.
How to learn it. Fortunately, HTML is a pretty simple language to learn, and you can pick up the basics in a few hours. The reason for this is that, as a markup language, HTML starts with plain text and then uses a series of code elements known as tags to format that text and include other webpage elements, such as images and embedded video. W3Schools offers a free HTML tutorial that will have you up and running in no time. From there, learn by example. Visit pages around the web, and look at the HTML source code. You can examine the work of skilled web developers and learn how they built your favorite sites in HTML.
4. JavaScript
Why you need it. While HTML forms the basis of webpages, JavaScript provides them their power. JavaScript code is widely used to incorporate outside elements, track user activity and perform many other web tasks. It's also the language used in many web-based application attacks, such as cross-site scripting. If you want to become an intrusion analyst, you'll definitely need to have some JavaScript experience under your belt.
How to learn it. As with other coding languages, you can pick up some basic JavaScript in the tutorials available from any site, such as those at W3Schools. From there, a great way to start learning how it's used in practice is to simply look at the JavaScript used on any website that you visit. View the source of a webpage, and look for JavaScript code, trying to figure out the purpose and intent of the code. That's the exact same skill that cybersecurity professionals use when seeking to reverse-engineer JavaScript in the wild.
5. SQL
Why you need it. SQL, or Structured Query Language, is the language of relational databases. Database administrators, developers and end users write queries in SQL to retrieve, insert, update and delete information stored in database tables. Attackers also use this language to steal sensitive information, disrupt data stores and wage a series of web-based attacks. If you want to understand attacker activity and prevent SQL injection and other database-related attacks, you'll need at least a basic understanding of SQL.
How to learn it. Fortunately, it's not too difficult to learn SQL. If you have access to a relational database at work, exploring it is a great way to start. If you don't have access, many web-based tutorials provide you with the ability to get hands-on experience. I recommend the courses available from LinkedIn Learning and DataCamp. (Full disclosure: I am a LinkedIn Learning author.)
If you're still feeling overwhelmed, just pick any one of the five languages above, and get started. You'll soon learn that coding is an incredibly useful skill for any cybersecurity professional, and best of all, it's a lot of fun!
Mike Chapple, Ph.D., CISA, CISSP, is a senior director of IT with the University of Notre Dame.






