attack surface
What is an attack surface?
An attack surface is the total number of all possible entry points for unauthorized access into any system. Attack surfaces include all vulnerabilities and endpoints that can be exploited to carry out a security attack. The attack surface is also the entire area of an organization or system that's susceptible to hacking.
For most modern businesses, the attack surface is complex and massive. The large number of devices, web applications and network nodes create many potential cybersecurity threats.
IT leaders, despite their best efforts, can only see a subset of the security risks their organization faces. However, they should consistently monitor their organization's attack surface to help identify potential threats.
An attack surface's size can change over time as new systems and devices are added or removed. For example, the attack surface of an application could include the following:
- Admin interfaces.
- Application programming interfaces (APIs).
- Authentication entry points.
- Data.
- Data pathways.
- Interfaces with other applications.
- Local storage.
- User interfaces.
What are the different types of attack surfaces?
Attack surfaces can be physical, digital or social:
- Physical attack surfaces comprise all endpoint devices, such as desktop systems, laptops, mobile devices, hard drives and USB ports. This type of attack surface includes all the devices that an attacker can physically access. Likewise, this also includes improperly discarded hardware that contains user data and login credentials, passwords on paper or physical break-ins.
- Digital attack surfaces encompass applications, code, ports, servers and websites, as well as unauthorized system access points. A digital attack surface is all the hardware and software that connect to an organization's network. Vulnerabilities caused by poor coding, weak passwords, default operating system settings, exposed APIs, outdated software or misconfigurations are all part of the digital attack surface.
- Social engineering attack surfaces surround the topic of human vulnerabilities as opposed to hardware or software vulnerabilities. Social engineering is the concept of manipulating a person with the goal of getting them to share and compromise personal or company data. Therefore, an organization's social engineering attack surface is the number of authorized users who are susceptible to social engineering attacks. Phishing attacks are a well-known example of social engineering attacks.
What is attack surface management?
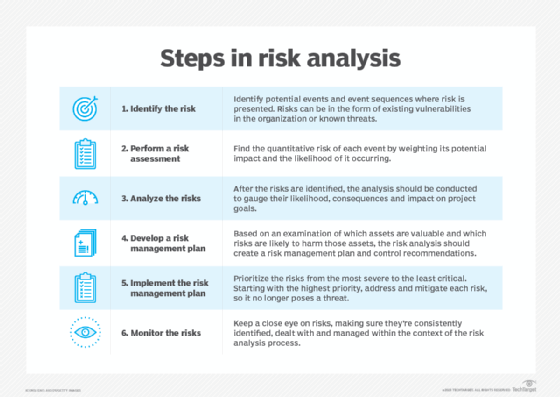
Attack surface management refers to the continuous surveillance and vigilance required to mitigate all current and future cyber threats. It includes all risk assessments, security controls and security measures that go into mapping and protecting the attack surface, mitigating the chances of a successful attack.
Key questions answered in attack surface management include the following:
- What are the high-risk areas and vulnerabilities in the system?
- Where can new attack vectors be created due to system changes?
- Who has access to each system?
- How can the system be protected from cyber attacks?
Organizations should continuously monitor attack surfaces for changes that could raise their risk of a potential attack. For example, an organization's internet-facing IT devices should be continually monitored for any changes and potential threats.
Organizations can also use security methods such as a zero-trust security policy to manage and reduce their attack surface. Zero-trust policies -- such as continuous validation, continuous monitoring and least-privileged access -- can help reduce attack vectors.
How can the attack surface be limited?
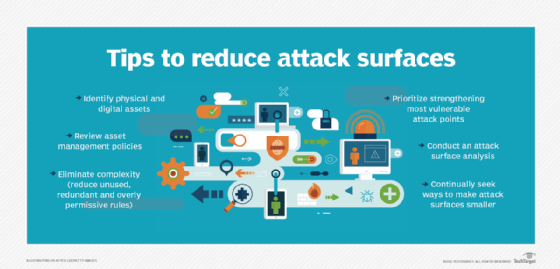
Organizations can have information security experts conduct attack surface analysis and management. Some ideas for attack surface reduction include the following:
- Control access. Organizations should limit access to sensitive data and resources both internally and externally. They can use physical measures, such as locking access cards, biometric systems and multifactor authentication.
- Remove complexities. Unnecessary or unused software can result in policy mistakes, enabling bad actors to exploit these endpoints. All system functionalities must be assessed and maintained regularly.
- Scan regularly. Digital assets and data centers must be scanned regularly to spot potential vulnerabilities.
- Use network segmentation. Tools such as firewalls and strategies including microsegmentation can divide the network into smaller units.
- Remove impractical features. Removing unnecessary features reduces the number of potential attack surfaces.
- Train employees. Help employees avoid social engineering attacks such as phishing by training them.
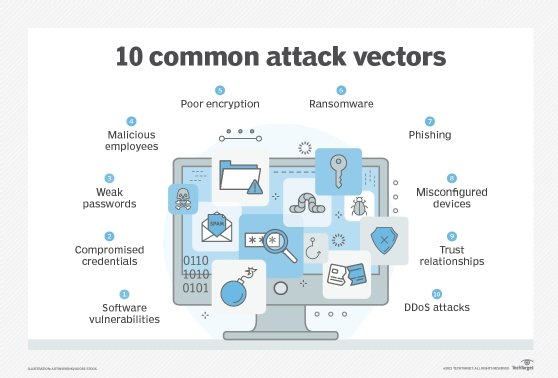
What is the difference between an attack surface and an attack vector?
The term attack surface is often confused with the term attack vector, but they aren't the same thing. The surface is what's being attacked; the vector is how an intruder gains access. Some common attack vectors include the following:
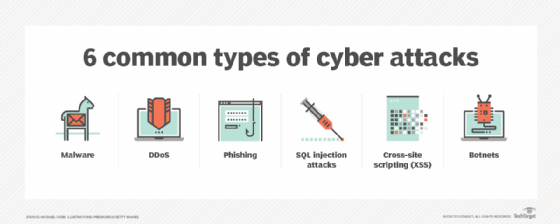
- Cyber attacks. These are deliberate attacks cybercriminals use to gain unauthorized access to an organization's network. Examples include phishing attempts and malicious software, such as Trojans, viruses, ransomware or unethical malware.
- Network data interception. Network hackers might attempt to extract data such as passwords and other sensitive information directly from the network.
- Data breaches. Inside threats -- such as rogue employees, social engineering ploys and unauthorized users posing as service workers -- can result in sensitive data being leaked to the general public.
How to manage digital attack surfaces
Digital attack surfaces are all the hardware and software that connect to an organization's network. To keep the network secure, network administrators must proactively seek ways to reduce the number and size of attack surfaces.
There's a law of computing that states that the more code that's running on a system, the greater the chance the system will have an exploitable security vulnerability. One of the most important steps administrators can take to secure a system is to reduce the amount of code being executed, which helps reduce the software attack surface.
Organizations can use microsegmentation to limit the size of attack surfaces. The data center is divided into logical units, each of which has its own unique security policies. The idea is to significantly reduce the surface available for malicious activity and restrict unwanted lateral -- east-west -- traffic once the perimeter has been penetrated. Policies are tied to logical segments, so any workload migration will also move the security policies.
Network microsegmentation isn't new. But, its adoption has been sparked by software-defined networking and software-defined data center technologies.
Traditional firewalls remain in place to maintain north-south defenses, while microsegmentation significantly limits unwanted communication between east-west workloads within the enterprise.
Organizations should also conduct regular security testing at potential attack surfaces and create an incident response plan to respond to any threat actors that might appear.
It's also important to create a policy for managing third-party risks that appear when another vendor has access to an organization's data. For example, a cloud storage provider should be able to meet an organization's specified security requirements -- as using a cloud service or a multi-cloud environment increases the organization's attack surface. Similarly, the internet of things devices also increase an organization's attack surface.
How to manage physical attack surfaces
A physical attack surface includes access to all endpoint devices, including desktop systems, laptops, mobile devices, USB ports and improperly discarded hard drives. Once an attacker has accessed a computing device physically, they look for digital attack surfaces left vulnerable by poor coding, default security settings or software that hasn't been updated or patched.
Bad actors can exploit the physical attack surface through inside threats -- such as rogue employees, social engineering ploys and intruders posing as service workers -- especially in public companies. External threats include password retrieval from carelessly discarded hardware, passwords on sticky notes and physical break-ins.
Physical security includes three important components: access control, surveillance and disaster recovery (DR). Organizations should place obstacles in the way of potential attackers and harden physical sites against accidents, attacks or environmental disasters. Hardening measures include fencing, locks, access control cards, biometric access control systems and fire suppression systems.
Organizations should monitor physical locations using surveillance cameras and notification systems, such as intrusion detection sensors, heat sensors and smoke detectors. They should test DR policies and procedures regularly to ensure safety and to reduce the recovery time from disruptive man-made or natural disasters.
Still, many security risks can happen in the cloud. Learn how to reduce risks involved with cloud attack surfaces here.