supply chain risk management (SCRM)
What is supply chain risk management (SCRM)?
Supply chain risk management (SCRM) is the coordinated efforts of an organization to help identify, monitor, detect and mitigate threats to supply chain continuity and profitability.
The supply chain is a network of companies and activities involved in the manufacturing and distribution of goods and services. With SCRM, possible risks such as natural disasters, geopolitical upheavals, pandemics, cyber attacks and supplier failures are assessed. By identifying and assessing these risks, organizations can build mitigation strategies to manage and lessen the effect of disruptions on their operations and bottom line.
Examples of supply chain risks
Threats to the supply chain can affect business continuity by inducing risk factors such as cost volatility, material shortages, supplier financial issues and failures, and natural and manmade disasters.
According to the National Institute of Standards and Technology, examples of risks to the supply chain can encompass counterfeiting, tampering, theft, introduction of malicious software and hardware and substandard manufacturing and development procedures. SCRM strategies and software help an organization foresee potential issues and adapt to those risks and unforeseeable supply chain disruptions as quickly and efficiently as possible.
This article is part of
What is risk management and why is it important?
The risks to the supply chain can come from both internal and external factors.
Internal supply chain risks
Internal supply chain risks originate from within a company and can cause operational or supply chain disruptions. As these risks are within the organization's control or influence, there are opportunities to effectively mitigate and manage them. Examples of internal supply chain risks include the following:
- Manufacturing risks. Interruptions and disruptions in internal procedures can result in quality failures where products fail to meet their specifications or their performance is subpar.
- Business risks. Business risks can arise from changes to key employees, management, reporting structures or operational protocols, such as the interaction between suppliers, customers and procurement.
- Mitigation risks. Mitigation risks can arise when companies fail to plan for contingencies or explore alternative options.
- Planning and control risks. Planning and control hazards can result from inadequate assessment and planning, which can lead to less-than-ideal management and control.
- Cultural risks. Cultural risks can arise from a business culture that's prone to concealing or postponing the release of negative facts.
External supply chain risks
Risks that come from outside a company and have the potential to affect the supply chain's seamless operation are known as external supply chain risks. Since businesses can't directly manage these risks, it's necessary to take preventative actions to reduce their negative effects. Examples of external supply chain risks include the following:
- Demand risks. These risks stem from unseen or inaccurately interpreted needs of consumers or end users.
- Environmental risks. Environmental hazards come from outside the supply chain and are usually associated with political, social, economic and environmental problems, such as natural disasters and the possibility of terrorism.
- Supply risks. Supply risks are generated by any interruptions in the movement of goods -- whether raw materials or components -- within an organization's supply chain.
- Business risks. Business risks are generated by variables such as a supplier's financial or management stability, or the purchase and sale of supplier enterprises.
- Physical plant risks. The state of a supplier's physical facilities and regulatory compliance can produce physical plant risks.
What are the consequences of a supply chain attack?
Supply chain attacks can have serious ramifications on businesses, their customers and even entire industries. According to Gartner, by 2025, 45% of global organizations are anticipated to have encountered attacks on their software supply chains.
Some key consequences of supply chain attacks include the following:
- Financial losses. Supply chain attacks can incur substantial financial setbacks for organizations. These attacks can cause interruptions in operations, expensive periods of inactivity, postponements in production or service provisions and necessitate extensive corrective actions.
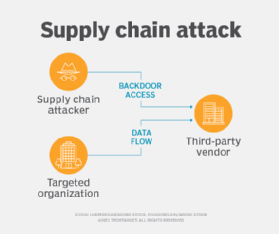
- Data breaches. A supply chain attack has the potential to compromise sensitive data and result in data breaches. Attackers might gain unauthorized access to systems, steal valuable information or manipulate data for malicious purposes.
- Business disruptions. Successful supply chain attacks have the potential to seriously impair an organization's functioning, as they can lead to production delays, disruptions in services and crippled productivity.
- Reputational damage. Supply chain attacks can seriously damage an organization's reputation if they jeopardize the reliability and quality of its products. Trust and loyalty from customers and suppliers can deteriorate, resulting in a decline in business prospects and earnings.
- Regulatory and legal consequences. Attacks on the supply chain could have legal and regulatory repercussions for organizations. For example, if an organization violates data protection rules or fails to protect consumer data, it can be held accountable with fines and legal implications.
- Malware installation. Applications containing malicious code from supply chain attacks can be exploited to download and inject malware into company networks. Attackers could install ransomware, rootkits, keyloggers, viruses and other malware using injected supply chain attack code.
Best practices for a SCRM plan
An organization should consider best practices for efficiently identifying, evaluating and mitigating risks while creating supply chain risk management strategies.
Key steps involved in creating an SCRM plan include the following:
- Identify and assess risks. The first step in developing an effective supply chain risk management program is to recognize and evaluate potential risks, including supply chain issues, natural disasters, geopolitical events and threats to cybersecurity. Both internal and external factors that can affect the supply chain should be assessed.
- Develop a formal SCRM program. Businesses should create a comprehensive supply chain risk management program that describes the roles, responsibilities and processes involved in managing supply chain risks. This program should be updated regularly.
- Monitor critical suppliers and components. Organizations must comprehend which providers are vital to their business and continue to keep an eye on and assess their performance, dependability and risk-taking acumen.
- Deploy SCRM across the board. SCRM practices should be executed throughout the organization, ensuring that all relevant departments and stakeholders are involved. This entails raising awareness, providing training and establishing communication channels within the organization.
- Establish protocols for supplier assessment. Organizations should create guidelines and standards for evaluating their vendors' supply chain operations. This could entail assessing their risk management procedures, supply chain security culture and adherence to industry standards.
- Collaborate with stakeholders. Organizations should encourage communication and cooperation between key stakeholders, such as vendors, clients and business associates as this can help them recognize possible hazards and take appropriate actions. SCRM requires collaboration and coordination among an organization's sales, marketing, production, development, procurement, finance and IT departments.
- Continuously improve and adapt. SCRM is an ongoing process that requires continuous improvement and adaptation. Organizations should stay current on industry trends, regulatory changes and emerging risks that could affect their supply chain through continuous monitoring, participation in industry forums and engagement with relevant experts.
SCRM tools and software considerations
Various tools are available for efficient control of supply chain risks. Examples of tools for SCRM include the following:
Tools for supply chain mapping
These tools aid in the visualization and mapping of the complete supply chain, encompassing vendors, producers, retailers and end users. They give businesses a thorough understanding of the supply chain network, making it possible to spot dependencies, weak points and possible risks. Examples of tools used for supply chain mapping include value stream mapping as well as vendor tools Microsoft Power BI and Tableau.
Tools for risk assessment
These tools aid in the identification, assessment and prioritization of hazards in the supply chain ecosystem. They can help organizations evaluate the possibility and effect of various hazards through the use of algorithms and data analysis techniques. Examples include risk assessment tools from vendors Avetta and Resilinc.
Tools for supplier relationship management (SRM)
SRM tools offer a consolidated platform for performance tracking, communication and collaboration, which aids in managing relationships with suppliers. Organizations can monitor supplier performance, assess compliance and oversee contracts and agreements with the help of these technologies. Examples of SRM software vendors include Coupa, GEP and SAP.
Tools for demand forecasting
These tools make predictions about future demand for goods and services based on market patterns, historical data and statistical models. Reducing supply chain interruptions, increasing customer happiness and optimizing inventory levels are all facilitated by accurate demand forecasting for businesses. Machine learning and various types of AI algorithms are increasingly being used for demand forecasting in the supply chain. Examples of tools include amoCRM, FutureMargin and Pipedrive.
Tools for code verification
Vulnerabilities caused by third-party code integrated into a proprietary system pose one of the biggest hazards in a digital supply chain. These tools scan all third-party code for verification and integrity before letting them get near the internal systems. Examples of code verification tools include IBM Rational AppScan and Veracode.
Tools for incident management
These tools help companies properly respond to and handle problems or disturbances in the supply chain. They aim to minimize interruptions by coordinating response activities and providing procedures, communication channels and documentation capabilities. Examples of tools that can be used for incident management in the supply chain include Elementum, FoodLogiQ and TraceLink.
Tools for collaboration and communication
These tools help supply chain stakeholders collaborate and communicate more effectively. Real-time information sharing, document collaboration and coordination amongst various supply chain teams and partners are made possible by these tools. Examples of tools include Epicor, Oracle SCM Cloud and SAP.
Effective risk management is crucial for every aspect of a business. Explore the 12 essential skills risk managers require to excel in their roles.
