
2 Free Server and Hardware Inventory Templates
Maintaining an inventory of your servers, devices and apps helps classify information about servers and keeps information about software and applications all in one place. In addition, a provisioning inventory provides evidence of activities the IT team has executed, such as configuration changes, capacity planning, last restores and recovery tests.
The types of inventory data collected and the business management decisions they are used for include hardware and software provisioning, asset management and asset tracking.
Here are two free downloadable templates, which administrators can use to manually record inventory data. They are:
- An asset tracking template
- A configuration/asset management template
The asset tracking template focuses on data with financial relevance, and the configuration/asset management template focuses on data relevant to the asset's upkeep and ability to provide a service. For example, the management template includes a column for recent configuration changes, which is important to the functioning of a server. The tracking template has columns for the warranty status, which is data that primarily relates to the server's financial status.
Why You Should Use These Templates
Both free templates provide administrators a guideline for manually recording data about provisioning, management and tracking processes. Manually recording and organizing inventory data allows for more thorough audits and closer administrator control over sever data. Administrators can tend to issues that an automated tool might miss when manually managing inventory data. Depending on the inventory data, one template might be preferable over the other.
Provisioning, Configuration and Asset Management
Proper provisioning is a central part of configuration management. A network administrator can view and use the hardware and software details collected from servers to make important decisions about provisioning. For example, a server provisioned for a new workload needs the operating system, files, applications and access configured according to established policy for a known desired state. When new employees join the company, their digital provisioning includes details of the client settings, including access to groups, applications and storage appropriate for their roles.
It's hard to provision resources without knowing what resources are available. So, organizations use IT asset management and configuration management tools to find and manage their available resources.
Configuration and asset management govern the items under different lifecycles. For example, asset management governs a server from procurement through disposal. Conversely, configuration management is only aware of this server while it is associated with a given service or services. If the service is discontinued, asset management continues to govern the server's financial relevance, while configuration management no longer has active reference to it. A server could be provisioned over its lifetime to support several different services, where each implementation of the same physical server would be viewed as a new continuous integration to the configuration management process.
Many configuration management tools have some native IT asset inventory capabilities. Some inventory features in configuration management tools enable automated discovery, wherein the tool queries systems and determines the hardware and software available on each server, as well as desktop computers, storage and network devices. Discovery may also extend to the virtual layer's VMs, operating systems and applications. An import feature can pull in inventory lists supplied by other parties, such as a cloud infrastructure provider.
A prime example of such a tool is Microsoft's Azure Resource Explorer run with Microsoft’s System Center Configuration Manager (SCCM). Administrators can use its software inventory tool to collect information about files on client devices. The software inventory functionality can also collect files from client devices and store them on the site server. The client sends the information to a management point in the client's site. The management point then forwards the inventory information to the Configuration Manager site server, which stores the information in the site database.
Below is an example template for storing and tracking configuration data collected by a management tool:

Asset Tracking
Inventory also crosses over into IT asset tracking, providing a comprehensive picture of physical and software assets across the enterprise. IT asset information ranges from vendor makes and models to details such as serial numbers, device asset number information, purchase and service contract forms, and software license and maintenance agreement data. Asset management helps organizations monitor spending, protect gear, ensure useful agreements and prevent license violations.
IT asset tracking summaries can inform resource capacity decisions. When administrators see which resources are available and how those resources are used over time, they can predict future use and make purchasing decisions.
A free asset tracking template, like the one below, can be used to record important minutia associated with servers. These include the CPUs (e.g., the socket name, status, number of cores, cores enabled, number of threads, vendor, version, signature of the server CPUs); I/O devices (e.g., description, type, vendor, MAC address and serial number of the I/O devices on the server); and the storage (e.g., the description, type, vendor, size, bus info and serial number of the storage devices).
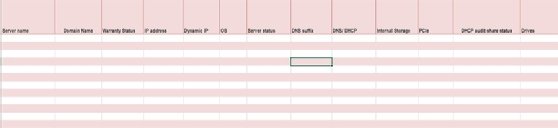
 Click image to download
Click image to download


