35 cybersecurity statistics to lose sleep over in 2024
Here are 35 eye-opening cybersecurity stats from dozens of security experts -- on crime, jobs and trends -- to consider while developing your 2024 security plan.
Hackers and data miners continue to become more sophisticated, malicious and just plain greedy. Even the general public has become aware of security threats and incidents that splash across news headlines.
In other words, you don't have to be an enterprise IT pro to understand the latest security risks. That's the easy part.
The hard part is understanding who is at risk, why and when you might fall prey to an attack, how pervasive attacks are and what types of threats are most likely to occur. Also important is understanding the costs and consequences associated with attacks, technologies that prevent a cybersecurity attack, and the fallout once an attack or data breach has occurred. The following cybersecurity statistics should help you to understand the risks, ensure network security and -- just in case -- create an incident response plan.
Cybercrime and cybersecurity statistics
Before diving into the specific types of cyberattacks, you need to understand how much data is involved. By 2025, humanity's collective data will reach 175 zettabytes -- the number 175 followed by 21 zeros. This data includes everything from streaming video and dating apps to healthcare databases. Securing all this data is vital.
The main goal for cybercriminals is to acquire information -- name, passwords and financial records, for example -- that is then sold on the dark web. As explained below, attacks can happen at any time and both individuals and organizations are victims:
- Perhaps no cybersecurity trend has been bigger in the last several years than the scourge of attacks related to the supply chain. Cyber incidents, such as the 2023 MoveIt vulnerability, the breach at software management vendor SolarWinds and Log4j in the open source world, put organizations around the globe at risk. Analyst firm Gartner predicted that by 2025, 45% of global organizations will be impacted in some way by a supply chain attack.
- The volume of reported vulnerabilities continues to rise. The "Vulnerability and Threat Trends Report 2023" from Skybox Security reported a 25% year-over-year increase in the number of new vulnerabilities in the U.S. government's National Vulnerability Database from 2021 to 2022.
- Cybersecurity will remain a constant concern and there will be continued risk in 2024 from attacks against technology-enabled resources and services, including financial systems and communication infrastructure, according to the "Global Risks Report 2023" from the World Economic Forum.
- The annual average cost of cybercrime is predicted to hit more than $23 trillion in 2027, up from $8.4 trillion in 2022, according to data cited by Anne Neuberger, U.S. Deputy National Security Advisor for cyber and emerging technologies.
- While businesses try to protect their own sensitive files from attack, customer information is stored in vulnerable databases all over the world. Identity fraud losses tallied a total of $20 billion in 2022 and affected 15.4 million U.S. adults, according to data in the "2023 Identity Fraud Study: The Butterfly Effect" from Javelin Strategy & Research.
- It takes an average of 277 days for security teams to identify and contain a data breach, according to "Cost of a Data Breach Report 2023," released by IBM and Ponemon Institute.
- According to the same report, data breaches involving lost or stolen credentials take longer to identify and contain at 328 days.
- Cryptojacking remains incredibly prevalent, increasing by 659% over 2022's threats to 1.06 billion cryptojacking attacks in 2023, according to the "2024 SonicWall Cyber Threat Report."
- The mid-year update to the "2023 SonicWall Cyber Threat Report" identified a year-to-date increase of 37% in IoT malware attacks.
- An Apple sponsored independent study found that breaches reached an all-time high for the first nine months of 2023, coming in at 20% more than any other year for the same period.
- The FBI's Internet Crime Complaint Center reported the volume of complaints in 2023 from the U.S. public at 880,418, which is a 10% increase from 2022. Total losses from those complaints totaled $12.5 billion.
Cybersecurity issues and threats
There are many types of security threats. Unlike a breach, a security incident doesn't necessarily mean information has been compromised, only that the information was threatened. The biggest types of security threats are malware, ransomware, social engineering, phishing, credential theft and DDoS attacks.
- The human element is the most common threat vector, and was the root cause of 74% of data breaches, according to Verizon's "2023 Data Breach Investigations Report." Humans also played a role in phishing attacks and stolen credentials. Phishing attacks are often delivered via email and hope to trick a user into clicking a link or providing information that can lead to exploitation.
- Mobile malware is on the rise, with Kaspersky Lab reporting that its products blocked 8.3 million mobile attacks in the third quarter of 2023 alone.
- Ransomware attacks are a constant threat affecting all sectors, and it's only getting worse. Ransomware affected 66% of respondents' organizations, according to Sophos' "The State of Ransomware 2023" report.
- Phishing attacks increased by a whopping 1,265% in 2023, thanks in part to the growth of generative AI (GenAI), according to "The State of Phishing 2023" report from SlashNext. The Anti-Phishing Working Group (APWG) observed almost 1.3 million phishing attacks in the second quarter of 2023, representing the third-highest quarterly total ever observed by the group.
- The financial sector remained the primary target, experiencing 23.5% of all phishing attacks, according to the APWG.
- DDoS attacks spiked in 2023, with Netscout reporting approximately 7.9 million DDoS attacks in the first half of 2023 for a 31% year-over-year gain. The maximum attack bandwidth for a DDoS attack was 991 Gbps.
- One of the largest and most sophisticated DDoS attacks in 2023 was an attack reported by Cloudflare that peaked at 201 million requests per second (rps), which is the highest volume of attack request reported to date.
For more on incident response, read the following articles:
How to create an incident response playbook
Incident response best practices for your organization
Building an incident response framework for your enterprise
The cost of cybercrime
Cybercrime can affect a business for years after the initial attack occurs. The costs associated with cyberattacks -- lawsuits, insurance rate hikes, criminal investigations and bad press -- can put a company out of business quickly.
- Part of maintaining a high level of security is ensuring nonsecurity employees know how security affects their day-to-day activities. Building a security awareness training program is a necessary part of any company's security strategy as employees ranging from associates to CEOs are constantly inundated with phishing emails. When you have mobile and IoT devices in your environment, creating a mobile incident response plan is a must. The Accenture "State of Cybersecurity Resilience 2023" report identified the impact of organizations that align cybersecurity with business objectives, as being very beneficial. The group that Accenture identifies as "cyber transformers" reported 26% lower costs from breaches than other respondent organizations and are 18% more likely to increase revenue growth.
- A single attack -- be it a data breach, malware, ransomware or DDoS attack -- cost U.S. companies an average of $8,300 in 2023, down from $10,000 in 2022. However, the average number of attacks per organization rose from three in 2022 to four in 2023, according to the "Hiscox Cyber Readiness Report 2023."
- The average total cost of data breaches in 2023 was $4.45 million, according to the IBM/Ponemon Institute report mentioned above. Breaches in the healthcare industry were the costliest at $10.93 million on average versus $5.90 million for financial services.
- While 48% of all SMBs have experienced a cyberattack, 43% of them have challenges understanding what security is actually required, according to the "Cyber security for SMBs: Navigating Complexity and Building Resilience" report from Sage Group.
- Excluding the Department of Defense, the U.S. government has budgeted $10.46 billion on cybersecurity spending for 2023.
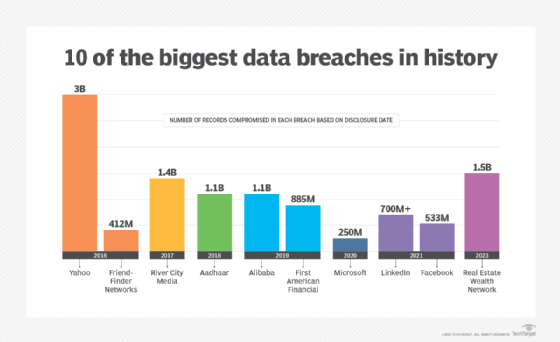
- Over the course of 2022 and 2023, Apple's sponsored security report found that a staggering 2.6 billion personal records had been leaked in data breaches.
- By 2030, global spending on cybersecurity will reach $538.3 billion, according to Statista.
Headlines from the cybersecurity industry
Plenty of security news broke in 2023. Hackers and cybercriminals ruthlessly attacked businesses and individuals alike. But cybercrimes aren't the only news security experts should consider from 2023. Here's a look at some of the major industry trends related to GenAI, incident response, attacks and testing:
- GenAI started to become a cybersecurity concern in 2023 and it's likely to become a much bigger issue in 2024 and beyond. According to the HackerOne 2023 "Hacker-Powered Security Report," 61% of hackers plan to use GenAI for hacking tools and to find more vulnerabilities.
- GenAI is making phishing more dangerous by enabling attackers to more easily construct articulate lures to reel in potential victims.
- Beyond phishing, there are multiple security risks associated with GenAI that began to be exposed in 2023, including sensitive data leakage and data poisoning.
- The FBI's Cyber's Most Wanted list features more than 100 individuals and groups that conspired to commit the most damaging crimes against the U.S. These crimes include computer intrusions, wire fraud, identity theft, espionage, trade secret theft and many other offenses.
- In 2023, approximately 63% of applications had first-party code flaws and 70% had flaws in third-party code, according to the Veracode "State of Software Security 2024" report.
- Managing mobile device security is another challenge. Devices that have been rooted or jailbroken, along with devices that likely had malware installed, are one form of risk. Additional mobile risk comes from the growing volume of text messaging-based business email compromise.
The skills shortage
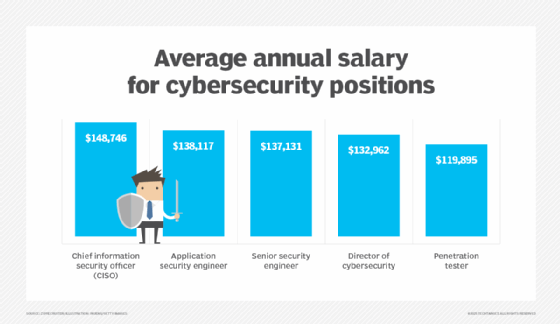
The cybersecurity industry has an employee and skills shortage. But don't lose heart, faithful security pros: Joseph Blankenship, a research director for security and risk at Forrester Research, suggested organizations look inward for current employees who might be well suited for security careers, and then recruit and train them for those new roles. There might be plenty of individuals out there -- such as networking admins, developers, systems engineers and even security analysts -- with the chops needed for the job.
The U.S. government is also working to improve the recruitment process. The Cybersecurity and Infrastructure Security Agency (CISA) is among the most active government agencies recruiting IT talent.
- An estimated 5.5 million people are globally employed in the cybersecurity industry, according to the "2023 ISC2 Cybersecurity Workforce Study," but approximately 4 million cybersecurity employees are still needed globally.
- The "State of Cybersecurity 2023" report from ISACA found that 71% of organizations have unfilled cybersecurity positions.
- Adding further insult to injury, that same study reported that 44% of organizations are managing staff with less than three years of cybersecurity experience. There are several reasons why organizations are managing an inexperienced workforce, including talented cybersecurity staff being recruited by other companies and poor salary incentives. Other top reasons employees leave, the survey said, are limited opportunities for promotion and high work stress levels.
- The "2023 ISC2 Cybersecurity Workforce Study" found Asia-Pacific, the Middle East and Africa, and North America had the biggest demands for a cybersecurity workforce.
If the previous statistics have you lying awake in the middle of the night, here's a statistic to help you sleep: According to Gartner's 2024 worldwide IT forecast, global IT spending is set to grow by 8% to $5.1 trillion. Cybersecurity will be a healthy benefactor of the spending growth, with Gartner reporting that 80% of CIOs plan to increase cybersecurity budgets in 2024.
Sean Michael Kerner is an IT consultant, technology enthusiast and tinkerer. He has pulled Token Ring, configured NetWare and has been known to compile his own Linux kernel. He consults with industry and media organizations on technology issues.








