outsourcing
What is outsourcing?
Outsourcing is a business practice in which a company hires a third party to perform tasks, handle operations or provide services for the company.
The outside company, which is known as the service provider or a third-party provider, arranges for its own workers or computer systems to perform the tasks or services either onsite at the hiring company's own facilities or at external locations.
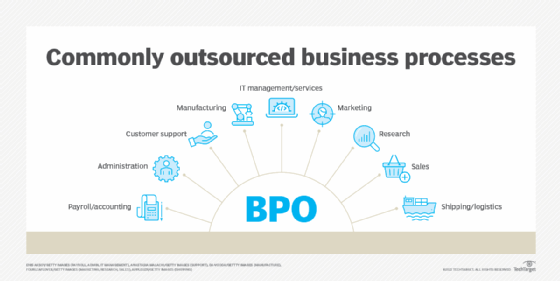
Companies today can outsource a number of tasks or services. They often outsource information technology services, including programming and application development, as well as technical support. They frequently outsource customer service and call service functions. They can outsource other types of work as well, including manufacturing processes, human resources tasks and financial functions such as bookkeeping and payroll processing. Companies can outsource entire divisions, such as its entire IT department, or just parts of a particular department.
Outsourcing business functions is sometimes called contracting out or business process outsourcing.
Outsourcing can involve using a large third-party provider, such as a company like IBM to manage IT services or FedEx Supply Chain for third-party logistics services. But it can also involve hiring individual independent contractors, temporary office workers and freelancers.
How outsourcing works
For a company to effectively outsource responsibilities, it is important to focus on the business partnership as much the logistics. Outsourcing is about managing relationships, more than service-level agreements, and is a partnership, not a purchasing project. Maintaining and securing a trusted relationship is essential in outsourcing efforts and is more complex than establishing service levels and relationships.
Some experts recommend placing extra emphasis on the exit clause of a service contract. It is important for companies to know when the contractual agreement inevitably times out and ensure that the involved parties fulfill their obligations and stick around until the contract is up.
Reasons for outsourcing
Companies often outsource as a way to lower costs, improve efficiencies and gain speed. Companies that decide to outsource rely on the third-party providers' expertise in performing the outsourced tasks to gain such benefits. The underlying principle is that because the third-party provider focuses on that particular task, it is able to do it better, faster and cheaper than the hiring company could.
Given such benefits, companies often decide to outsource supporting functions within their businesses so they can focus their resources more specifically on their core competencies, thereby helping them gain competitive advantages in the market.
However, some companies decide to outsource for other reasons.
For example, they outsource because they're unable to hire in-house, full-time employees with the specialized skills and experience needed to perform certain jobs.
Companies sometimes opt to outsource as a way to shift meeting regulatory requirements or obligations to the third-party provider.
Furthermore, companies look to outsourcing providers as innovation centers.
Types of outsourcing
There are several ways to outsource a business process, and depending on the process, one may be preferable over another. Broadly there are a few different types based on the distance between the two members of the relationship. These types are:
- Onshoring. Relocating work or services to lower-cost location in the company's own country.
- Offshoring. Relocating work or services to third-party providers overseas.
- Nearshoring. Relocating work or services to people in nearby, often bordering regions and countries.
Outsourcing agreements can also vary widely in scope. For certain processes, like programming or content creation, hiring freelancers on a job-to-job basis might be appropriate. A company outsourcing their entire IT department will require a long-term partnership with clearly stated requirements.
Examples of outsourcing
The increasing use of virtual assistants is one trend where outsourcing will play a significant role. More and more, enterprises are using business-level virtual assistants to automate certain processes. This means an increased need for specialized voice assistant applications. Many companies may choose to outsource that development project for cost and skill reasons.
If the company was American, and chooses to "offshore" that work, they may hire a development firm in India or England, for example. If they chose to "nearshore" the work, they may develop a relationship with a Canadian or Mexican third party. If they "onshore" the project, they would likely communicate with a business close by or hire independent contractors.
The closer the third party is to the client company; the less time and cultural differences will make an impact. Because application development is often an asynchronous process, being tightly scheduled isn't the top priority, and clients seeking that work may prefer offshoring to onshoring.
Pros and cons of outsourcing
In addition to delivering lower costs and increased efficiencies, companies that outsource could see other benefits.
By outsourcing, companies could free up resources (i.e., cash, personnel, facilities) that can be redirected to existing tasks or new projects that deliver higher yields for the company than the functions that had been outsourced.
Companies might find, too, that they can streamline production and/or shorten production times because the third-party providers can more quickly execute the outsourced tasks.
Outsourcing, however, can produce challenges and drawbacks for companies.
Companies engaged in outsourcing must adequately manage their contracts and their ongoing relationships with third-party providers to ensure success. Some might find that the resources devoted to managing those relationships rivals the resources devoted to the tasks that were outsourced, thereby possibly negating many, if not all, of the benefits sought by outsourcing.
Companies also could realize that they lose control over aspects of the outsourced tasks or services. For instance, a company could lose control over the quality of customer service provided when it outsources its call center function; even if the company's contract with the provider stipulates certain quality measures, the company might find it's more difficult to correct an outsourced provider than it would be to correct an in-house team.
Companies that outsource could also face heightened security risks, as they exchange with their third-party providers the company's proprietary information or sensitive data that could be misused, mishandled or inadvertently exposed by the outsource provider.
Additionally, companies might encounter difficulties in getting their own employees to communicate and collaborate effectively with those working for third-party providers -- a scenario that's more common if the third party operates overseas.
Ethics of outsourcing
Outsourcing has raised some ethical issues for companies as well.
Most notably, some have criticized the practice for its impact on workers. Employees at companies that decide to outsource frequently see the decision to outsource as a threat to their job security; in many cases, that fear is justified as they lose their jobs to workers who may be paid less and receive fewer benefits.
This scenario has also drawn criticism from the public, as well as from politicians and labor leaders.
Companies could also face negative publicity as a result of their decisions to outsource, with customers and the public in general viewing the move as a way to cut workers' wages and benefits or as a way to skirt environmental, financial or safety regulations.
Insourcing vs. outsourcing
Companies may decide against outsourcing and instead turn to insourcing.
As the name implies, insourcing refers to the practice of having in-house teams perform functions that could be handled by outside companies or contactors. Thus, insourcing can be viewed as the opposite of outsourcing.
Sometimes insourcing involves hiring new employees, either on a permanent or temporary basis, to execute the tasks being insourced. Companies might need to invest in new equipment, hardware and software when insourcing, and they might need to reengineer business processes as well.
Outsourcing trends
Although outsourcing had been viewed as a way to lower costs and gain efficiencies, it is increasingly becoming a strategic tool for companies.
Leading companies understand that outsourcing some functions can help them gain a competitive advantage by allowing them to access expertise or innovative technologies they don't have in-house; or by helping them deliver products or services more quickly; or enabling them to shift resources to the areas of the business that are most critical. Outsourcing offers both cost-efficiency and increased workload flexibility.







