API gateway (application programming interface gateway)
What is an API gateway?
An API gateway is a software pattern that sits in front of an application programming interface (API) or group of microservices to facilitate requests and delivery of data and services. Its primary role is to act as a single entry point and standardized process for interactions between an organization's apps, data and services and internal and external customers. The API gateway can also perform various other functions to support and manage API use, from authentication to rate limiting to analytics.
These broad capabilities make the API gateway an essential piece of an enterprise API strategy.
How does an API gateway work?
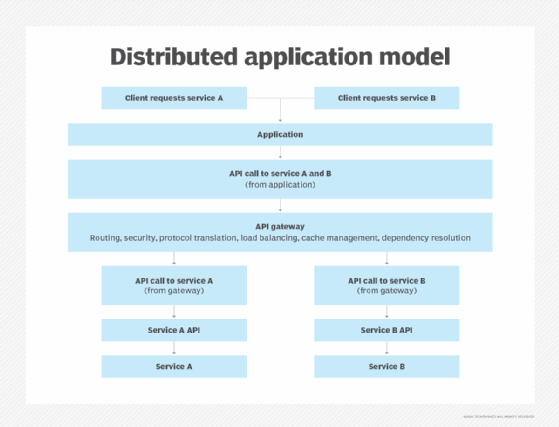
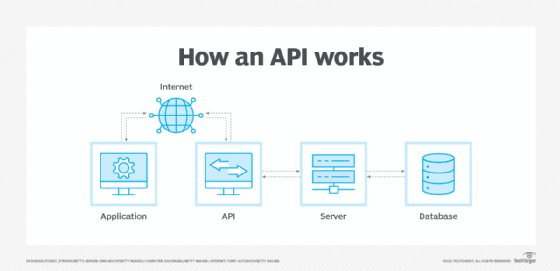
APIs allow separate applications to communicate with one another and exchange data within and outside a business. The API gateway provides a focal point and standard interface to perform these activities. It receives routing requests from internal and external sources that are called API calls and packages multiple requests, routes them to the appropriate API or APIs, and receives and delivers the responses to the user or device that made the request.
API gateways are also key to a microservices architecture, in which data requests invoke numerous applications and services that use multiple, disparate APIs. Here the API gateway's role is similar: Provide a single point of entry for a defined group of microservices and apply policies to determine their availability and behavior.
API gateways often handle other functions involved with APIs and microservices:
- Protocol translation.
- Service discovery optimization.
- Basic business logic and metrics.
- Authentication and security policy enforcement.
- Stabilization and load balancing.
- Cache management.
- Monitoring, logging and analytics.
- Access control.
- Scalability of workloads.
Who uses API gateways and why?
The API gateway is the focal point for API messaging, organizing and streamlining API activity and exchanges with internal and external customers. The gateway provides API management and oversight that lets an organization see and control a broad scope of APIs and integrations centrally, rather than tracking and managing APIs individually.
API gateway use cases typically include real-time monitoring and logging capabilities to record and analyze calls and responses ensure security and evaluate errors. Gateways also support functionality that governs APIs. For example, policy managers use logical statements operated through an API gateway to determine the API's availability and behavior, such as how it controls the flow of data or handles throttling and throughput of API calls.
Organizations that have adopted a microservices-based architecture similarly rely on API gateways to facilitate communications among those services. API gateways also help streamline B2B integration as an alternative to legacy approaches such as electronic data interchange services.
API gateway vs. API proxy
An alternative to the API gateway is an API proxy, which is a subset of an API gateway that provides minimal processing for API requests. The API proxy handles communication -- including protocol translation -- between specific software platforms -- such as a proxy endpoint and target API.
An API proxy can also have traffic management capabilities, controlling the flow of traffic between sending and receiving points. However, API gateways typically have better performance analysis and monitoring capabilities.
API gateway vs. service mesh
Like an API gateway, a service mesh facilitates communications to and from an enterprise's services with some load balancing and other functionality. However, a service mesh typically handles internal communications, and its role is at the network management level; an API gateway facilitates interactions with external users and devices as well as internal sources, and resides at the application layer.
The roles of API gateways and service mesh can be complementary. For example, API gateways can be an entry point into a mesh, and some API gateways offer plugins to form a service mesh themselves.
API gateway benefits
An API gateway's primary benefit is in standardizing and centralizing delivery of services through APIs or microservices. Beyond this, API gateways help secure and organize an organization's API-based integrations and API ecosystem in several ways. The following are some of those benefits:
- Simplify services delivery. API gateways can combine multiple API calls to request and retrieve data and services, which reduces the volume of requests and traffic. This streamlines the API process and improves the user experience and workflows, particularly for mobile applications.
- Provide flexibility. API gateways are highly configurable. Developers can encapsulate the internal structure of an application in multiple ways, to invoke multiple back-end services and aggregate the results.
- Extend legacy applications. Enterprises that rely on legacy applications can use API gateways to work with those apps and extend their functionality. API gateways can be used as an alternative to broader, more complicated and expensive migration.
- Contribute to monitoring and observability. Most organizations rely on specific tools for monitoring activity through APIs, but an API gateway can help assist these efforts. Gateway logs can help pinpoint an issue during a monitoring failure event.
- Impact of artificial intelligence (AI). AI can enhance API gateway performance and automation. For example, it can examine performance data, identify trends for further analysis and potentially boost gateway performance.
API gateway challenges
The API gateway is the gatekeeper between API consumers and providers. That role presents unique challenges, such as the following:
- Reliability and resilience. Any impairment or hindrance to the API gateway's functionality can cause associated services to fail. In addition, an API gateway is an extra process step between customers and applications or data. Enterprises must be wary of adding features that affect performance or increase latency.
- API security. The API gateway is a trusted source that touches many parts of an enterprise's business. If it's compromised, this is potentially a serious and far-reaching security problem. Businesses should separate external-facing interfaces from internal APIs and systems, and define authentication and authorization parameters.
- Complexity and dependencies. Developers must update the API gateway whenever an API or microservice is added, changed or deleted. This is particularly challenging in a model where a few applications could become dozens or hundreds of microservices. Creation of and adherence to API and microservices design rules can help mitigate these problems.
- AI risks. Just as AI's emergence in technology promises increased benefits, it also carries risks. For example, AI elements must be properly instructed regarding their activities; errors in such instructions could negatively impact gateway performance.
Types of API gateway products?
Given the importance of the API gateway in today's API economy, many providers offer API gateways either as standalone tools or functionality bundled into broader API management platforms. Examples of API management platform vendors that incorporate some kind of API gateway functionality include Akana by Perforce, Cloudflare, MuleSoft, Postman, Tibco Software and Workato.
Organizations also can separately buy and use API gateway tools. Examples include Apigee (part of Google Cloud), Express Gateway, Gloo API Gateway, Goku API Gateway, Kong Gateway, KrakenD API Gateway, Ocelot API Gateway, Oracle API Gateway and Tyk API Gateway.
The major public cloud providers offer platforms that manage API lifecycles: AWS API Gateway, Google Cloud Endpoints and Microsoft Azure API Management. They also offer API gateway tools specific to their platforms.
Factors to consider when evaluating an API gateway
Businesses should weigh several criteria as they choose an API gateway, including the following:
- Current vs. long-term requirements. Business requirements must be factored into any technology investment decision. Current API gateway deployments might be satisfactory, but when planning API gateways, it's important to consider potential future requirements, such as adding new APIs.
- Proprietary vs. open source. A business evaluating a vendor's API gateway might already use other products from that vendor. Examples include Oracle, or the major public cloud providers. By contrast, many enterprises are comfortable with open source tools and in-house support.
- Architecture. Some API gateway tools emphasize simplicity, while others emphasize extensibility. They also often support different database systems, such as Cassandra, PostgreSQL, MongoDB or Redis. As stated above, businesses that already rely on a particular cloud provider might prefer that provider's API gateway.
- Customization. Some API gateways, particularly open source options, might offer more customization options and that requires in-house expertise. However, some API gateways rely on different programming languages, such as Golang or Lua. Ensure that IT staff skills line up with such requirements. Plugins can partly mitigate this issue.
Asking the right questions is important when selecting an API gateway and related tools. Learn more about popular API gateway tools.