web analytics
What is web analytics?
Web analytics is the process of analyzing the behavior of visitors to a website. This involves tracking, reviewing and reporting data to measure web activity, including the use of a website and its components, such as webpages, images and videos.
Data collected through web analytics may include traffic sources, referring sites, page views, paths taken and conversion rates. The compiled data often forms a part of customer relationship management analytics (CRM analytics) to facilitate and streamline better business decisions.
Web analytics enables a business to retain customers, attract more visitors and increase the dollar volume each customer spends.
Analytics can help in the following ways:
- Determine the likelihood that a given customer will repurchase a product after purchasing it in the past.
- Personalize the site to customers who visit it repeatedly.
- Monitor the amount of money individual customers or specific groups of customers spend.
- Observe the geographic regions from which the most and the least customers visit the site and purchase specific products.
- Predict which products customers are most and least likely to buy in the future.
The objective of web analytics is to serve as a business metric for promoting specific products to the customers who are most likely to buy them and to determine which products a specific customer is most likely to purchase. This can help improve the ratio of revenue to marketing costs.
In addition to these features, web analytics may track the clickthrough and drilldown behavior of customers within a website, determine the sites from which customers most often arrive, and communicate with browsers to track and analyze online behavior. The results of web analytics are provided in the form of tables, charts and graphs.
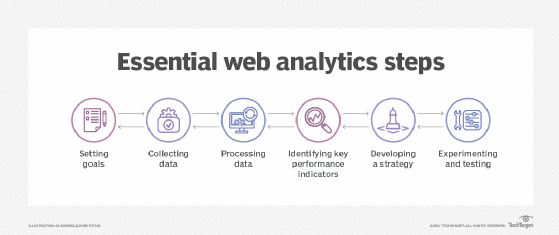
Web analytics process
The web analytics process involves the following steps:
- Setting goals. The first step in the web analytics process is for businesses to determine goals and the end results they are trying to achieve. These goals can include increased sales, customer satisfaction and brand awareness. Business goals can be both quantitative and qualitative.
- Collecting data. The second step in web analytics is the collection and storage of data. Businesses can collect data directly from a website or web analytics tool, such as Google Analytics. The data mainly comes from Hypertext Transfer Protocol requests -- including data at the network and application levels -- and can be combined with external data to interpret web usage. For example, a user's Internet Protocol address is typically associated with many factors, including geographic location and clickthrough rates.
- Processing data. The next stage of the web analytics funnel involves businesses processing the collected data into actionable information.
- Identifying key performance indicators (KPIs). In web analytics, a KPI is a quantifiable measure to monitor and analyze user behavior on a website. Examples include bounce rates, unique users, user sessions and on-site search queries.
- Developing a strategy. This stage involves implementing insights to formulate strategies that align with an organization's goals. For example, search queries conducted on-site can help an organization develop a content strategy based on what users are searching for on its website.
- Experimenting and testing. Businesses need to experiment with different strategies in order to find the one that yields the best results. For example, A/B testing is a simple strategy to help learn how an audience responds to different content. The process involves creating two or more versions of content and then displaying it to different audience segments to reveal which version of the content performs better.
What are the two main categories of web analytics?
The two main categories of web analytics are off-site web analytics and on-site web analytics.
Off-site web analytics
The term off-site web analytics refers to the practice of monitoring visitor activity outside of an organization's website to measure potential audience. Off-site web analytics provides an industrywide analysis that gives insight into how a business is performing in comparison to competitors. It refers to the type of analytics that focuses on data collected from across the web, such as social media, search engines and forums.
On-site web analytics
On-site web analytics refers to a narrower focus that uses analytics to track the activity of visitors to a specific site to see how the site is performing. The data gathered is usually more relevant to a site's owner and can include details on site engagement, such as what content is most popular. Two technological approaches to on-site web analytics include log file analysis and page tagging.
Log file analysis, also known as Log Management, is the process of analyzing data gathered from log files to monitor, troubleshoot and report on the performance of a website. Log files hold records of virtually every action taken on a network server, such as a web server, email server, database server or file server.
Page tagging is the process of adding snippets of code into a website's HyperText Markup Language code using a tag management system to track website visitors and their interactions across the website. These snippets of code are called tags. When businesses add these tags to a website, they can be used to track any number of metrics, such as the number of pages viewed, the number of unique visitors and the number of specific products viewed.
Web analytics tools
Web analytics tools report important statistics on a website, such as where visitors came from, how long they stayed, how they found the site and their online activity while on the site. In addition to web analytics, these tools are commonly used for product analytics, social media analytics and marketing analytics.
Some examples of web analytics tools include the following:
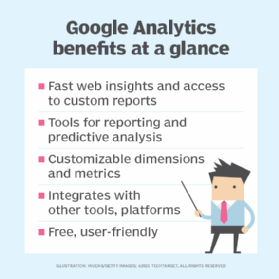
- Google Analytics. Google Analytics is a web analytics platform that monitors website traffic, behaviors and conversions. The platform tracks page views, unique visitors, bounce rates, referral Uniform Resource Locators, average time on-site, page abandonment, new vs. returning visitors and demographic data.
- Optimizely. Optimizely is a customer experience and A/B testing platform that helps businesses test and optimize their online experiences and marketing efforts, including conversion rate optimization.
- Kissmetrics. Kissmetrics is a customer analytics platform that gathers website data and presents it in an easy-to-read format. The platform also serves as a customer intelligence tool, as it enables businesses to dive deeper into customer behavior and use this information to enhance their website and marketing campaigns.
- Crazy Egg. Crazy Egg is a tool that tracks where customers click on a page. This information can help organizations understand how visitors interact with content and why they leave the site. The tool tracks visitors, heatmaps and user session recordings.







