
virtual assistant (AI assistant)
What is a virtual assistant (AI assistant)?
A virtual assistant, also called an AI assistant or digital assistant, is an application program that understands natural language voice commands and completes tasks for the user.
Such tasks -- historically performed by a human personal assistant or secretary -- include taking dictation, reading text or email messages aloud, looking up phone numbers, scheduling, placing phone calls and reminding the user about appointments. Popular virtual assistants include Amazon Alexa, Apple Siri, Google Assistant and Microsoft Cortana.
Types of virtual assistants
Though this definition focuses on the digital form of virtual assistants, the terms virtual assistant and virtual personal assistant are also commonly used to describe contract workers who work from home doing administrative tasks typically performed by executive assistants or secretaries.
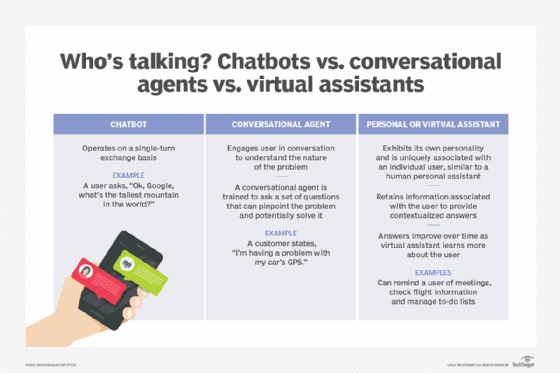
With the evolution of chatbots and generative AI, various types of virtual assistants have gained popularity. However, they serve different purposes for customers and provide different levels of assistance.
This article is part of
A guide to artificial intelligence in the enterprise
Common types of virtual AI assistants include the following:
- AI chatbots. AI chatbots are computer programs that serve as virtual assistants and communicate with users through text-based interfaces on websites, social media platforms and messaging apps. These chatbots can assist customers, respond to inquiries or start a discussion with them. AI chatbots employ natural language processing (NLP) and machine learning (ML) algorithms to understand user input, produce pertinent responses and improve their performance over time by learning from these interactions.
- Conversational agents. Beyond text-based chatbots, conversational agents enable virtual assistants to converse in a human-like manner through both text and voice interfaces. These AI-based systems are designed to comprehend intricate linguistic patterns, discern user intent and offer responses that are appropriate in a given situation. Conversational AI can be used to build more sophisticated virtual assistants that can handle various tasks and offer a more intuitive and natural user interface.
- AI virtual assistants. These advanced virtual assistants can perform a variety of tasks, often across multiple devices and platforms. They frequently converse with users by using natural language through voice-based interactions. With these AI virtual assistants, users can easily and quickly access information, control smart home appliances and manage their calendars by integrating with a variety of services and applications. Amazon Alexa and Apple Siri are examples of AI virtual assistants.
Virtual assistant devices and technology
Virtual assistants are typically cloud-based programs that require internet-connected devices and applications to work. Most AI virtual assistants can be found on devices such as smartphones, smart speakers or other platforms, including instant messaging apps.
AI chatbots that use generative AI, such as ChatGPT, are also gaining popularity for their ability to generate human-like responses to text-based conversations.
Common virtual assistant technologies and devices include the following:
- Siri. Apple's built-in, voice-controlled personal virtual assistant is available on devices using iOS, iPadOS, watchOS, macOS and tvOS. It uses voice recognition technology that's powered by AI.
- Cortana. Microsoft's personal productivity assistant Cortana uses the Bing search engine to perform various tasks, including setting reminders and answering user queries.
- Copilot. Copilot is an AI assistant built into the Windows 11 operating system that can be used across all Windows apps and programs. It provides a natural user interface through AI-powered chat for interacting with the Windows operating system.
- Google Assistant. This virtual voice assistant software application was developed by Google for Android devices. Google Assistant can perform a variety of tasks including answering questions, adjusting hardware settings on the user's device, scheduling events and alarms, and playing games.
- Amazon Alexa. Used mainly through Amazon's product line of hands-free speakers known as Amazon Echo, Alexa is a cloud-based voice service available on more than 100 million Amazon devices as well as third-party manufacturers. To use Alexa, users call out the wake word, Alexa and a light on the device signals to the user that it's ready to receive a command, which typically involves simple language requests, such as "what is the weather today?" or "play pop music." Alexa will also gain access to generative AI with its own large language model and use it to enable access to more than 200 smart home APIs. Instead of saying “Alexa, turn on the air conditioning,” users can say, “Alexa, I’m hot,” and the assistant will turn on the heat using advanced contextual understanding that AI enables.
- Samsung's Bixby. Samsung's virtual AI assistant runs primarily on mobile devices but also some smart refrigerators. Bixby can be used for various tasks including texting, retrieving location-specific weather information, setting meeting reminders and reading news articles.
- Mycroft AI platform. Mycroft is the first open source voice assistant that can be run on any platform, including desktops, automobiles and even on a Raspberry Pi. It focuses on voice-enabling any device to turn it into a smart personal assistant.
The technologies that power virtual assistants require massive amounts of data, which feed AI platforms, including machine learning, NLP and speech recognition platforms. As the end user interacts with a virtual assistant, the AI programming uses sophisticated algorithms to learn from data input and become better at predicting the end user's needs.
Capabilities of virtual assistants
Virtual assistants typically perform simple jobs for end users, including the following:
- Adding tasks to a calendar.
- Providing information that would normally be searched in a web browser.
- Controlling and checking the status of smart home devices, including lights, cameras and thermostats.
- Making and receiving phone calls.
- Scheduling meetings.
- Creating text messages.
- Getting directions.
- Hearing news and weather reports.
- Finding hotels or restaurants.
- Checking flight reservations.
- Streaming podcasts.
- Setting reminders.
- Workflow management.
- Assisting in e-learning and training.
- Calling an Uber of Lyft.
- Listening to music.
- Playing games.
Privacy concerns
Some consumers have expressed privacy concerns about virtual assistants, such as Amazon Alexa and Google Home. These virtual assistants require large amounts of personal data and are always listening in order to respond to voice commands, also known as wake words or phrases. Although voice assistants are only intended to begin recording when given the wake command by a user, they may accidentally capture voice exchanges and private information without the user's knowledge.
Cortana, for example, works best by using data from a user's device, including emails and other communications, a user's contacts, location data, search history and data from other Microsoft services and skills -- third-party applications -- that users choose to connect with. Users can choose not to sign in and share this data with Cortana and can adjust permissions to prevent certain data from being collected, though these actions limit the virtual assistant's usefulness.
Virtual assistant providers also maintain privacy policies, which define how each company uses and shares personal information. In most cases, companies don't share customer-identifiable information without a customer's consent but there have been concerns regarding how voice assistant providers use and handle user data.
Besides privacy policies practiced by providers, end users can also take the following security precautions:
- The settings of voice assistants can be changed to enable sound notifications, which will alert the user when the assistant is accidentally triggered and begins to record voice interactions. By default, the notifications of certain voice assistants such as Echo and a few Google devices are set to silent.
- Users can opt out of recordings of commands and conversations as well as historical records saved on the devices, such as with Amazon Alexa. However, this step doesn't guarantee that the data won't be evaluated once the transcripts are deleted.
- Users should practice extra caution when sharing certain types of information with voice assistants. It's best to avoid giving voice assistants access to sensitive information.
Separating business and personal voice assistant profiles can also improve privacy. The majority of assistants -- including Alexa and Google Assistant -- support multiple accounts, enabling users to segregate their personal voice assistants from their professional ones.
For more on artificial intelligence in the enterprise, read the following articles:
Artificial intelligence vs. human intelligence: How are they different?
AI vs. machine learning vs. deep learning: Key differences
Main types of artificial intelligence: Explained
What is trustworthy AI and why is it important?
The future of AI: What to expect in the next 5 years
AI regulation: What businesses need to know
Steps to achieve AI implementation in your business
How businesses can measure AI success with KPIs
The future of virtual assistants
Virtual assistants are quickly evolving to provide more capabilities to users. As speech recognition and NLP have advanced, so too has the virtual assistant's ability to understand and perform requests. And as voice recognition technology continues to improve, virtual assistant use will move deeper into business workflows.
Experts predict that AI assistants will continue to become humanistic and able to provide more personalized experiences as AI technology advances. According to Gartner, by 2025, these AI assistants will become more ubiquitous with about 50% of knowledge workers using a virtual assistant on a daily basis. However, the widespread use of AI assistants doesn't obscure the growing worries about the privacy and security risks associated with them. Companies are being urged to address these concerns transparently in their policies to build trust with users. The future of virtual assistants might also be tied to the metaverse, with companies exploring new ways of integrating these assistants into virtual reality environments.
The emergence of ChatGPT, an intelligent virtual assistant and AI-powered language model developed by OpenAI, has also raised discussions about the future of virtual assistants. While there has been some speculation about the potential influence of ChatGPT on the virtual assistant market, it's not yet clear how it will ultimately affect the future and direction of the industry.
AI and machine learning technologies are transforming businesses and society at large. Discover the top 10 AI trends that businesses should look out for as AI continues to advance.






