customer premises equipment (CPE)
What is customer premises equipment (CPE)?
Customer premises equipment (CPE) is telecommunications and information technology equipment kept at the customer's physical location rather than on the service provider's premises. Telephone handsets, cable TV set-top boxes and Digital Subscriber Line (DSL) routers are examples of CPEs.
Connectivity is established through a carrier's telecommunication circuit at a demarcation point, or demarc. The demarc point is typically a central office utilized by the service provider.
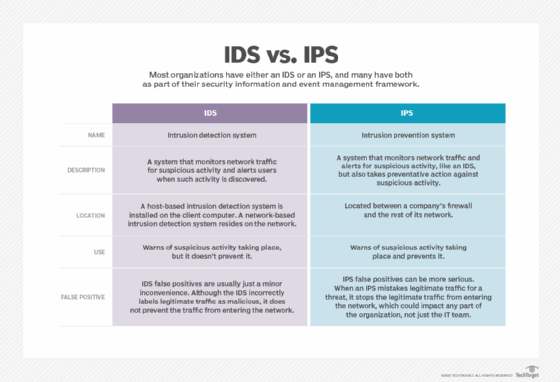
Service providers could include telecommunications companies or a networking and communications vendor, like Cisco. Cybersecurity providers can also be included in this list, for instance, including hardware-based firewalls and intrusion prevention or intrusion detection systems.
What is the history of customer premises equipment?
Historically, telecommunications companies placed CPE at the customer's end of the telephone line. Bell System, a system of companies under the Bell Telephone Company -- later AT&T, until its breakup in 1983 -- usually owned this equipment.
However, the U.S. Federal Communications Commission eventually ruled that carriers could no longer bundle CPE with a telecommunications service. So, today, almost any end-user equipment can be called customer premises equipment.
The subscriber or the provider can own these devices.
What are different types of customer premises equipment?
Today, a variety of different types of devices count as CPE. The following list includes a few examples:
- telephones and telephone handsets;
- Channel Service Units/Data Service Units, routers or wireless access point devices;
- Broadband, Ethernet or DSL modems;
- cable set-top boxes;
- adapters for network services;
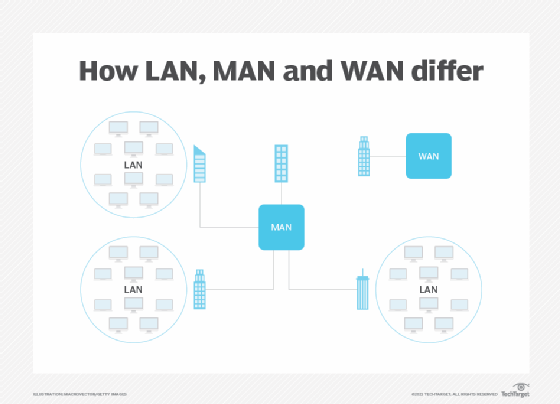
- Local area network (LAN) or wide area network (WAN) devices;
![LAN vs. WAN vs. MAN]()
The difference between a local area network, wide area network and metropolitan area network - private branch exchanges (aka routing switchboards);
- voice over Internet Protocol devices; and
- firewall hardware.
What is virtual customer premises equipment (vCPE)?
VCPE takes the concept of CPE hardware and brings it to software. So, unlike standard CPE, which brings provider-owned equipment on premises to customers, vCPE delivers network services, like virtual private networks, firewalls and routing, to users virtually through software.
Also referred to as cloud CPE, vCPE abstracts device intelligence that resides on remote data centers and brings it to inexpensive and simple on-site hardware.
As with the CPE model, vCPE can consolidate specialized devices onto a single general-purpose box. This makes the distribution and maintenance of these services more cost-effective and convenient -- potentially lowering capital and operating expenditures, simplifying operations and speeding up the delivery services.