CamelCase
What is CamelCase?
CamelCase is a way to separate the words in a phrase by making the first letter of each word capitalized and not using spaces. It is commonly used in web URLs, programming and computer naming conventions. It is named after camels because the capital letters resemble the humps on a camel's back.
CamelCase is formally referred to as medial capitals. It may also be called or styled as PascalCase, camel case, InterCaps, mixedCase or WikiCase.
The first letter may or may not be capitalized in CamelCase. This difference is called UpperCamelCase and lowerCamelCase. PascalCase always has the first letter capitalized.
Uses of CamelCase
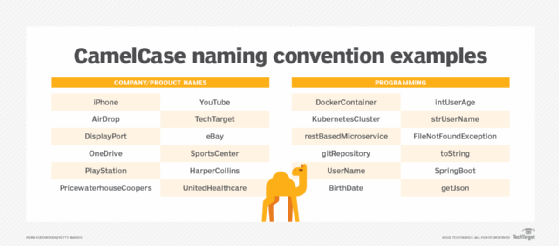
Many companies and technologies use CamelCase to create new words out of existing words that can be registered as trademarks. Some examples of these would be iPhone, AirDrop, DisplayPort, OneDrive, PlayStation, YouTube and TechTarget.
When a computer parses text, it treats the spaces as a delimiter between words. CamelCase is most used in places where white space is not allowed for technical reasons. This can make the phrase hard to read or ambiguous. An example of an ambiguous phrase in programming is chartable, which can be interpreted as char table (a table of characters) or chart able (having the ability to be charted). Other ways to remove white space are with dashes called kebab-case or with underscores with snake_case.
Website URLs often use CamelCase to replace spaces. Domain names cannot contain special characters and are not case-sensitive, so most websites write their domain name in CamelCase to make it easier to read and remember. If a space is present in a URL, it needs to use American Standard Code for Information Interchange percent encoding to replace it with %20, which is hard to read and type. Post tagging and #hashtags are often presented in CamelCase for easy readability. Emails may also be presented as CamelCase, such as [email protected].
CamelCase may be used in file names. While most file systems support spaces in file names, there are many reasons why CamelCase is popular. If a file is used on the internet URL, encoding the space in the file name may cause issues. Referring to file names or paths with a space in a command-line interface can be cumbersome and require the use of quotation marks. It is also important to note that some file systems are case-sensitive when referring to files.
CamelCase in computer programming
CamelCase is a popular convention in computer programming and variable names. Generally, variables can be any string of characters without white space. To keep them consistent and readable, it is best practice to establish variable naming conventions within an organization. Some examples of CamelCase variable names would be UserName, BirthDate, intUserAge and strUserName. Kebab-case is discouraged in many computer languages due to the dash being interpreted as a mathematical minus sign.
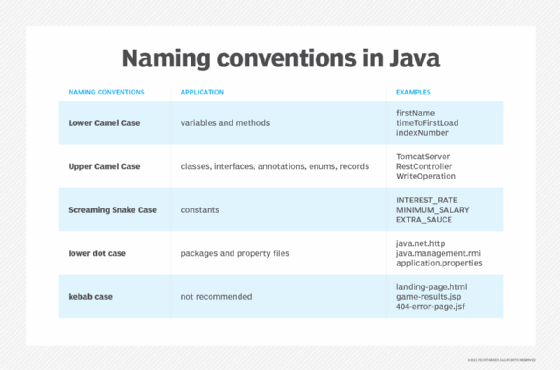
In some languages, CamelCase is encouraged in the developer documentation best practice. This can be specific to recommendations to using UpperCamelCase -- or PascalCase -- for some instances and lowerCamelCase for other. For example, naming conventions in Java recommend lowerCamelCase for variables, UpperCamelCase for classes and SCREAMING_SNAKE_CASE for constants.
Caution is required as some languages are case-sensitive. Depending on the language, userName and UserName may be interpreted as different variables or as the same one, causing errors. Java, Python and C are case-sensitive, while Basic and Pascal are not case-sensitive.
CamelCase may also be used in other instances such as Extensible Markup Language tags, domain name system names or Windows Active Directory names.
Explore the difference between kebab vs. CamelCase and CamelCase vs. snake case naming conventions.
