ISACA
What is ISACA?
ISACA is an independent, nonprofit, global association that engages in the development, adoption and use of globally acceptedinformation system(IS) knowledge and practices. Previously known as the Information Systems Audit and Control Association, ISACA now goes by its acronym only.
What does ISACA offer?
ISACA provides guidance, benchmarks and governance tools for enterprises that use information systems. ISACA also hosts a series of international conferences that focus on technical and managerial topics relating to IS assurance, control, security and IT governance.
It also administers manyprofessional certificationprograms, includingCertified Information Systems Auditor (CISA), Certified Information Security Manager (CISM), Certified in the Governance of Enterprise IT, Certified in Risk and Information Systems Control, Certified Data Privacy Systems Engineer, Cybersecurity Practitioner Credential, Certified in Emerging Technology (CET) and Information Technology Certified Associate (ITCA). Candidates must pass a certification exam to obtain the desired credential. Due to the popularity of the CISA exam, ISACA increased the frequency and locations of test centers for CISA candidates several years ago.
ISACA also offers 17 certifications across a broad range of IT issues, including risk, auditing, networking, cybersecurity and artificial intelligence (AI). The following is a list of those certifications:
- IT Audit Fundamentals Certificate.
- IT Risk Fundamentals Certificate.
- Certificate of Cloud Auditing Knowledge.
- Cybersecurity Audit Certificate.
- Computing Fundamentals Certificate.
- Networks and Infrastructure Fundamentals Certificate.
- Cybersecurity Fundamentals Certificate.
- Software Development Fundamentals Certificate.
- Data Science Fundamentals Certificate.
- Cloud Fundamentals Certificate.
- Blockchain Fundamentals Certificate.
- IoT Fundamentals Certificate.
- Artificial Intelligence Fundamentals Certificate.
- COBIT Design and Implementation.
- Implementing the NIST Cybersecurity Framework Using COBIT 2019.
- COBIT Foundation.
- COBIT 5 Certificates.
ISACA extends its reach globally through 225 chapters in 188 countries. Most of its 170,000 members have at least one ISACA credential, commonly the CISA. ISACA offers numerous educational programs, guidance and reference documents and other resources across its focus areas.
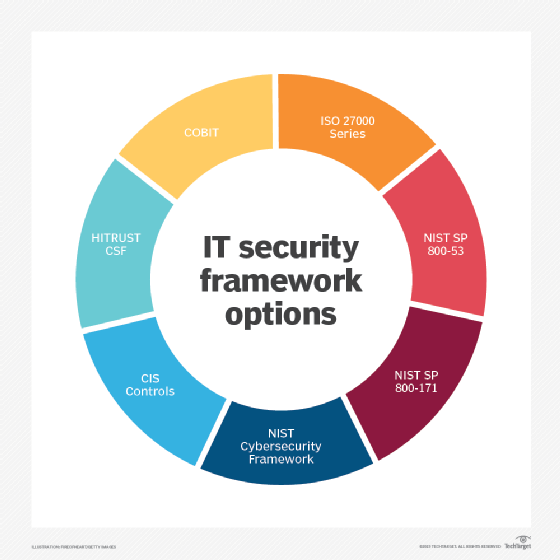
ISACA also developed Control Objectives for Information and Related Technology (COBIT), a businessand technology frameworkdesigned to help enterprises across industries manage their information and technology. The current version, COBIT 5, was updated in 2019 and is regularly reviewed and updated as needed. Numerous training courses, white papers and reference documents have been developed in support of COBIT.
Who uses ISACA?
Anyone involved in IT security, risk, governance, enterprise operations, and auditing can benefit from the many services offered by ISACA, in addition to membership and certification. Non-IT professionals can adapt ISACA tools and guidance to their own requirements.
Why is ISACA important?
Founded in 1969, ISACA has become a preeminent resource for IT professionals across different areas of information technology, governance and risk, cybersecurity, auditing and many other disciplines. ISACA certifications, particularly the CISM and CISA certifications, are among the most widely recognized and accepted IT credentials. While an ISACA credential does not guarantee a promotion or job offer, having a credential adds important credibility that is acknowledged by organizations of all types and sizes.
ISACA research and guidance resources are often referred to in the performance of a variety of IT initiatives, such as IT audits, IT governance, cybersecurity management and compliance projects. IT audits, for example, that are supported by ISACA guidance, are highly regarded as the auditing process can be performed consistently across a range of IT controls. Because the rules are globally accepted, organizations with large IT teams, can standardize their audit practices by using ISACA guidance and frameworks.
Pros and cons of ISACA membership and certification
ISACA certifications are recognized globally and have significant research and analysis behind them. Various ISACA internal teams and committees keep the rules up to date and in sync with emerging technology trends, such as AI and cybersecurity. Professional development is a primary activity, as ISACA offers dozens of training courses to help members sharpen their skills. ISACA membership provides the opportunity to network with tens of thousands of members worldwide.
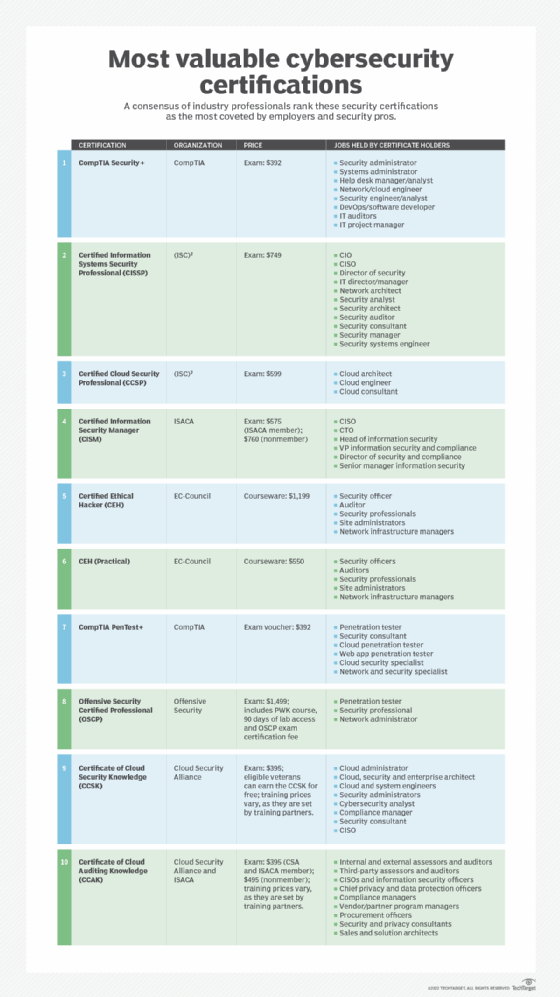
However, ISACA members pay annual dues for membership and for their certifications. Certified members must annually present evidence of their efforts at continuing education to retain their certifications. ISACA has several competitors in the IT training and certification space, such as the International Information Systems Security Certification Consortium (ISC2), CompTIA and SANS Institute. Each organization has a different focus, which is beneficial for IT professionals, who can pick and choose among the available options.
Check out nine advanced IT certifications for operations experts, and 10 cybersecurity certifications to boost your career. Compare top identity and access management certifications, and explore CISA practice questions to prep for the exam.






