CDN (content delivery network)
What is a CDN?
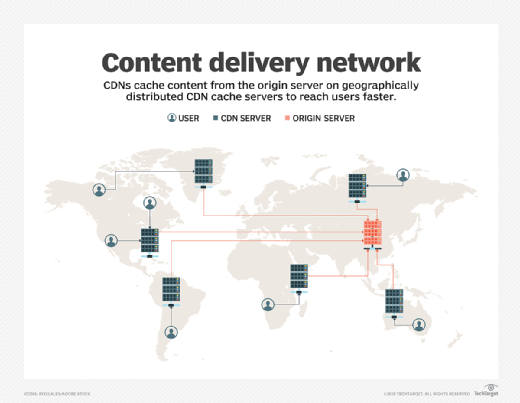
A CDN (content delivery network), also called a content distribution network, is a group of geographically distributed and interconnected servers. They provide cached internet content from a network location closest to a user to speed up its delivery.
The primary goal of a CDN is to improve web performance by reducing the time needed to send content and rich media to users. Today, CDNs serve the bulk of web traffic, including traffic from well-known websites such as Facebook, Netflix and Amazon.
Why is using a CDN important?
A content delivery network is crucial for providers and website owners because it makes it easier to transfer content -- such as images, videos and website files -- to numerous servers spread out around the globe. This enhances user experience, especially for users who are located far from the origin server. It also speeds up web page loading times while reducing the strain on the main server.
As the content is served from numerous servers, a CDN can help increase the security and dependability of a website, making it less susceptible to security attacks and downtime.
How does a CDN work?
The process of accessing content cache on a CDN network edge is almost always transparent to the user. CDN management software dynamically calculates which server is located nearest to the user, making the request and delivering content based on those calculations. CDN edge servers communicate with the content's origin server to deliver to the user cached content and new content that hasn't been cached.

Edge servers reduce the distance that content travels and the number of hops a data packet makes. The result is less packet loss, optimized bandwidth and faster performance. This minimizes timeouts, latency and jitter, and it also improves the user experience. In the event of an internet attack or outage, fresh content cached and hosted on a CDN server remains available to those users who are nearest to the edge locations until the time-to-live for the CDN server expires. For example, if a website server goes down, the website is still accessible to visitors if it was cached properly on different geographically dispersed servers.
Organizations buy services from CDN providers for routing content to users from the nearest geographic location. CDN providers either host the content themselves or pay network operators and internet service providers to host CDN servers.
CDN providers also use load balancing and solid-state drives to help data reach users faster. They reduce file size using compression and special algorithms, and deploy machine learning and artificial intelligence to enable faster load and transmission times.
How does CDN caching work?
The functionality of a CDN is mostly dependent on caching static content. The data is stored and cached by the CDN edge servers.
The following is an example of a typical CDN caching process:
- A web server in Chicago hosts static web content that a website visitor located in Washington, D.C., requests.
- Once the origin server in Chicago receives the request, it sends a response to the website visitor. Simultaneously, it delivers a copy of the response to the CDN point-of-presence (POP) that's geographically closest to the website visitor.
- The CDN POP stores its copy as a cached file.
- When the same visitor or another visitor in that location makes a similar request again, the caching server -- not the origin server -- delivers the response.
CDN vs. web host
Despite using similar technology, CDNs and web hosts have distinct purposes. The following are the main differences between the two:
- Unlike web hosts, CDNs don't provide content across the last mile to consumers and only provide temporary content storage and caching.
- Web hosting usually provides access to a single server that handles everything from host name resolution to delivering requests. On the other hand, CDNs use a network of servers that are spread out globally, resulting in reduced response times for websites because the data is served from the closest edge location.
- A web host is responsible for hosting a website. Although a CDN doesn't host content, it caches it at the network edge to enhance performance. Most websites that struggle with performance issues opt for CDNs.
- Web hosts serve all types of content but CDNs only serve and host static data. The workload on CDN servers is lessened as a result, letting them concentrate on their main task of edge delivery.
- Issues, including restricted bandwidth, service outages and security risks, occasionally happen with traditional web hosting. CDNs address these problems by employing content caching on edge servers.
What are the uses of a CDN?
The main use of a CDN is to deliver content through a network of servers in a secure and efficient way. These networks improve the content security, performance and availability. Other CDN use cases include collecting user analytics and tracking data on network traffic. CDNs serve a range of content, including websites, mobile applications, streaming media and downloadable objects. Social media and search engine traffic go through CDNs.
Content-owning organizations use CDN services to accelerate the delivery of static and dynamic content, online gaming, mobile content and streaming video, as well as other specialized services.
Some examples of how CDNs are used include the following:
- An e-commerce organization uses a CDN to deliver content at busy times of the year when traffic spikes are likely.
- A bank uses a CDN to securely transfer sensitive customer data.
- A mobile application provider uses a CDN to reduce load times and increase response times, improving mobile users' customer experience.
What are the benefits of a CDN?
CDNs provide several advantages:
- Efficiency. CDNs improve web page load times and reduce bounce rates. Both advantages keep users from abandoning a slow-loading site or e-commerce application.
- Security. Besides content caching and web delivery, CDN providers offer services that complement their core functionality and capitalize on their presence at the network edge. These services include distributed-denial-of-service (DDoS) attack mitigation, web application firewalls (WAFs) and bot mitigation.
- Availability. Since the website is distributed across multiple geographically dispersed servers, CDNs offer scalability. They can handle more traffic and avoid network failures better than origin servers. As a result, content is readily available.
- Optimization. These networks provide a diverse mix of performance and web content optimization services that complement cached site content.
- Resource and cost savings. CDNs reduce bandwidth consumption and costs.
- Reduced latency. CDN architecture is designed to reduce network latency caused by hauling traffic over long distances and across several networks. Eliminating latency is important as more dynamic content, video and software as a service are delivered to an increasing number of mobile devices. A reputable CDN provider can assist with delivering high-quality content at extremely low latency rates.
- Caching. CDN providers house cached content in either their POPs or third-party data centers. When a user requests content from a website that's also cached on a CDN, it redirects the request to the server nearest to the user and delivers the cached content from its location at the network edge. This process is invisible to the user.
- Improved performance. Many organizations use CDNs to cache website content to meet their performance needs. The demand for CDN services is increasing as websites offer more streaming video, e-commerce and cloud applications, where high performance is key. Few CDNs have POPs in every country. As a result, organizations must use several CDN providers to ensure they meet the needs of their customers and users, wherever they're located.
- Special services. Other services offered include web and application performance and acceleration services, streaming video and broadcast media optimization and digital rights management for video. Some CDN providers make their application programming interfaces (APIs) available to businesses to meet their unique needs.
What are examples of CDN platforms?
There are many CDNs available, each offering a variety of features. Products include the following:
- Akamai Technologies Inc. Intelligent Edge.
- Amazon CloudFront.
- ArvanCloud.
- CDN77.
- Cloudflare.
- Limelight Networks Edgio (formerly Yahoo Edgecast).
Some CDN providers, such as Cloudflare and Limelight, market their platforms as CDNs with added services, including DDoS or WAFs. Other providers, such as ArvanCloud, offer CDN services as part of several broader cloud services, such as cloud security and managed domain name system.
History of CDNs
CDNs are an integral part of modern internet architecture. They were born from a need to maintain efficient website performance and still serve that purpose today.
CDNs have evolved over the years and their evolution can be segmented into the following three generational types:
Static CDNs
Akamai launched the first static CDN in 1998. The company's techniques serve as the foundation of today's CDNs. First-generation CDNs focused mostly on static content, such as software downloads and audio and video streaming.
Static CDNs offered the following features:
- Served content included HTML and downloadable files.
- Used origin push caching.
- Improved server performance.
- Used a dispersed network topology.
- Cost a significant amount of money.
- Catered to the corporate sector.
Dynamic CDNs
As cloud and mobile computing gained traction, second-generation CDN services evolved. They enabled the efficient delivery of more complex dynamic multimedia and web content. As internet use grew, the number of CDN providers multiplied, along with the services they offered.
Dynamic CDNs offered the following features:
- Served both static and dynamic content, including rich media, to end users.
- Used origin pull caching.
- Used a consolidated network topology.
- Improve the efficiency and accessibility of servers and resources.
- Cost exorbitant amounts of money.
- Catered to the business sector.
Multi-purpose CDNs
The third-generation or next-generation CDN uses multiple CDNs from various CDN providers. A vast network of POPs is used instead of just one, which further improves the speed of content delivery, expands to wider regional and global coverages, and eliminates cybersecurity risks and outages.
Multi-purpose CDNs come with the following features:
- Serves both static and dynamic content, including rich media.
- Uses origin pull caching.
- Uses a highly consolidated network topology.
- Improves security, performance and availability.
- Costs an affordable amount of money.
The target audience for multi-purpose CDNs includes anyone who owns a website.
Some CDN business models are based on usage-based pricing or the volume of content delivered. Others charge a flat rate for basic services or even provide them for free, with additional fees for performance and optimization services.
Learn more about the benefits of a CDN service and how to choose the best one for your business.








