Amazon
What is Amazon?
Amazon (Amazon.com) is the world's largest online retailer and a prominent cloud service provider.
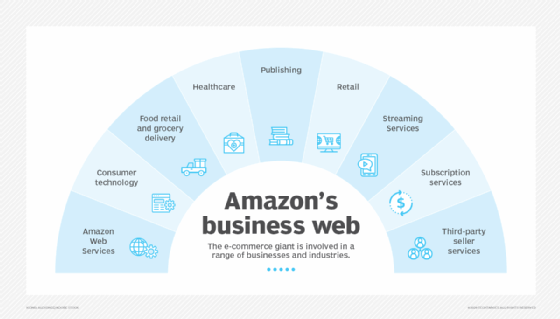
Originally started as an online bookselling company, Amazon has morphed into an internet-based business enterprise that is largely focused on providing e-commerce, cloud computing, digital streaming and artificial intelligence (AI) services.
Following an Amazon-to-buyer sales approach, the company offers a monumental product range and inventory, enabling consumers to buy just about anything, including clothing, beauty supplies, gourmet food, jewelry, books, movies, electronics, pet supplies, furniture, toys, garden supplies and household goods.
Headquartered in Seattle, Amazon has individual websites, software development centers, customer service centers, data centers and fulfillment centers around the world.
History and timeline of Amazon
Amazon has come a long way since it was founded by Jeff Bezos in his garage in Bellevue, Wash., on July 5, 1994.
The following is a brief history and timeline of events that have evolved Amazon from its humble beginnings to a multinational business empire.
The 1990s
Amazon officially opened for business as an online bookseller on July 16, 1995. Originally, Bezos had incorporated the company as Cadabra but later changed the name to Amazon. Bezos is said to have browsed a dictionary for a word beginning with A for the value of alphabetic placement. He selected the name Amazon because it was exotic and different and as a reference to his plan for the company's size to reflect that of the Amazon River, one of the largest rivers in the world. Since its inception, the company's motto has always been "get big fast."
The 2000s
In 2005, Amazon Prime This membership-based service for Amazon customers offers free two-day shipping within the contiguous U.S., as well as streaming, shopping and reading benefits. According to Amazon's website, current Amazon Prime membership rates are $14.99 a month or $139 per year.
Amazon Web Services
This comprehensive and evolving cloud computing platform was also born in the 2000s. The first Amazon Web Services (AWS) offerings were launched in 2006 to provide online services for websites and client-side applications. Amazon Elastic Compute Cloud (EC2) and Simple Storage Service (S3) are the backbones of the company's growing collection of web services. The same year, Amazon also launched a cloud computing and video-on-demand service known at the time as Unbox.
By changing the way people bought books, Amazon also shaped how they read them with the launch of its first Kindle e-reader in 2007. This device helps users browse, buy and read e-books, magazines and newspapers from the Kindle Store.
From the 2010s to present
Amazon debuted its first tablet computer, the Kindle Fire, in 2011 and the Amazon Fire TV Stick, which is part of Amazon's extensive line of streaming media devices, in 2014.
Amazon also started an online Amazon Art marketplace for fine arts in 2013, which has featured original works by famous artists such as Claude Monet and Norman Rockwell.
The popular in-home virtual assistant Amazon Alexa was rolled out to consumers in 2015 and was followed by the Alexa-equipped Echo Dot in 2016.
Amazon acquired the organic grocery store Whole Foods in 2017 and launched Amazon Go, a chain of cashierless grocery stores in 2018.
The rise of in-home shopping during the COVID-19 pandemic made consumers rely on Amazon even more, and the trend is likely to keep growing.

Notable Amazon products and services
Amazon offers an ever-expanding portfolio of services and products. Following is a list of its noteworthy offerings.
Retail
- Amazon Marketplace. Amazon's e-commerce platform enables third-party retailers to showcase and sell their products alongside Amazon items.
- Amazon Fresh. Amazon's grocery pickup and delivery service is currently available in nearly two dozen U.S. cities and a few international locations. A grocery order can be placed through the Amazon Fresh website or the Amazon mobile app. Customers can either get their groceries delivered or visit the store for pickup.
- Amazon Vine. Launched in 2007, Amazon Vine helps manufacturers and publishers get reviews for their products to help shoppers make informed purchases.
- Woot. Acquired by Amazon in 2010, Woot offers limited time offers and special deals that rotate daily. This shop features refurbished items, as well as new items that are low in stock. Prime members get free shipping.
- Zappos. Amazon bought Zappos in 2009. This online retailer of shoes and clothing carries a wide range of brands, including Nike, Sperry, Adidas and Uggs.
- Merch by Amazon. This on-demand T-shirt printing service enables sellers to create and upload their T-shirt designs for free and earn royalties on each sale. Amazon does the rest -- from printing the T-shirts to delivering them to customers.
- Amazon Handmade. This platform enables artisans to sell handcrafted products to customers around the world.
Consumer technology
- Amazon Kindle. Amazon's first e-reader, Kindle, enables users to browse, buy and read e-books, magazines and newspapers from the Kindle Store.
- Amazon Fire tablet. Previously known as Kindle Fire, Amazon's popular and high-profile Fire tablet competes with Apple's iPad.
- Amazon Fire TV. This line of Amazon's streaming media players and digital devices delivers streamed video content over the internet to a paired high-definition television.
- Amazon Alexa. This cloud-based, AI-powered, voice-controlled personal assistant is designed to answer queries, interact with users, and perform other tasks and commands.
- Amazon Echo. This is one of Amazon's smart home devices that comes equipped with a speaker and connects to Alexa. Amazon Echo can perform several functions, including talking about the weather, creating shopping lists and controlling other smart products, such as lights, switches and televisions.
- Amazon Echo Dot. A smaller, puck-shaped version of the original Amazon Echo, an Echo Dot can be placed in any room and can answer questions, play music, and read news and other stories.
- Amazon Echo Show. As part of the Amazon Echo line of speakers, the Amazon Echo Show works similarly through Alexa but also offers a 7-inch touchscreen display to play videos and music and conduct video calls with other Echo users.
- Amazon Astro. This is Amazon's first home monitoring robot that works with Alexa. It is designed to help with various household tasks, such as home monitoring, caring for the elderly through notifications and alerts, and following owners from room to room to play TV shows, music or podcasts.
Subscription services
- Amazon Prime. This subscription service provides members access to exclusive shopping and entertainment services, discounts and more. As an example, all Amazon Prime members enjoy free one-day or two-day shipping on qualifying orders.
- Amazon Prime Video. This is Amazon's on-demand video streaming service that offers a selection of about 24,000 movies and over 2,100 TV shows. This service is included with an Amazon Prime membership.
- Amazon Drive. Previously known as Amazon Cloud Drive, Amazon Drive is a cloud storage app that offers 5 gigabytes (GB) of free and secure online storage for photos, videos and files for Amazon customers. Amazon Prime members get free, unlimited, full-resolution photo storage, along with 5 GB of video storage.
- Twitch Prime. A monthly subscription service, Twitch Prime is a subsidiary of Amazon Prime. It gives members premium access to Twitch -- a video streaming platform that offers a fun and social way to watch people play games.
- Amazon Music Prime. This is Amazon's music streaming service that is free for Prime members.
Digital content
- Amazon Pay. An online transaction processing platform, Amazon Pay enables Amazon account holders to use their Amazon accounts to pay external online merchants.
- Amazon Music Unlimited. Amazon's premium music service costs $8.99 a month for Prime members and $9.99 for non-Prime members.
- Kindle Store. Part of Amazon's retail website, the Kindle Store can be accessed from any Kindle device to purchase e-books.
- Amazon Appstore for Android. Amazon's app store for the Android operating system enables users to download games and mobile apps to supported devices.
AWS
- S3. This is Amazon's scalable, cloud-based object storage. Files are referred to as objects in S3 and are stored in containers called buckets.
- Amazon Simple Queue Service (SQS). SQS is a pay-per-use web service that is designed to provide access to a waiting message queue where messages can reside until a computer processes them.
- Amazon EC2. This web service interface provides scalability with resizable compute capacity in the AWS cloud. Users can run virtual servers or instances, commonly known as EC2 instances, that can be scaled up or down, depending on the network requirements.
- Amazon S3 Glacier. Amazon S3 Glacier is a low-cost cloud storage service for data that might be associated with longer retrieval times. It also offers data archiving and backup of cold data.
- AWS Identity and Access Management (IAM). IAM provides secure and controlled access to resources.
- Amazon Redshift. This data warehouse in the cloud enables users to query petabytes of both structured and semistructured data using standard Structured Query Language queries. For example, to address the expanding volume of transactions, Nasdaq moved from a legacy on-premises data center to the AWS cloud, which is powered through the Amazon Redshift cluster.
Amazon AI services
- Amazon SageMaker. A fully managed cloud machine learning platform, Amazon SageMaker enables developers and data scientists to build, train and deploy machine learning models for predictive analytics applications.
- Amazon Lex. This service for building conversational interfaces into any application using voice and text is powered by the same technology as Alexa.
- Amazon Polly. A text-to-speech service, Amazon Polly uses deep learning technology to convert text into spoken audio. It includes 60 voices across 29 languages.
- Amazon Rekognition. This software-as-a-service facial recognition and analysis platform uses a deep learning algorithm to process images and extract information from them.
- AWS DeepLens. This programmable video camera enables developers to easily experiment withmachine learning, AI and the internet of things.
- Alexa Voice Service. This programming interface provides developers with a set of C++ libraries to add Amazon Alexa's speech and other capabilities into their applications and devices.
- Amazon Transcribe. This service converts speech to text quickly and accurately by using a deep learning process called automatic speech recognition.
- Amazon Translate. Amazon Translate is a cloud service that can convert large amounts of text written in one language to another language.
- Alexa Skills Kit. This software development kit enables developers to build skills or conversational applications on Amazon Alexa.
Amazon privately owned brands
- AmazonBasics. This is Amazon's privately labeled, low-budget brand that mainly sells kitchen, tech and household products.
- Amazon Elements. This line of domestic products includes health and personal care items, as well as nutritional supplements.
- Mama Bear. This private label of Amazon sells baby wipes, newborn through size 6 diapers, baby food, diaper pail refills and baby laundry detergent.
- Presto!. This brand started as a laundry detergent in 2016 but has added household paper towels and toilet paper to its product line.
- Amazon Essentials. A Prime-exclusive program, this clothing line offers basic wear for men, women, babies and kids, with additional options for family, big and tall, and athletic activity.
- Happy Belly. This private label of Amazon was introduced in 2016 and sells snack food items. In February 2019, the brand also began offering milk delivery services.
- Goodthreads. This menswear apparel line is available exclusively to Amazon Prime members. The label offers both casual and professional pieces and is deemed a bit higher quality and more stylish than the Amazon Essentials brand.
Notable Amazon subsidiaries and acquisitions
From healthcare to entertainment, Amazon has acquired multiple companies by tapping into a variety of sectors over time.
Following is a list of Amazon's notable acquisitions and subsidiary companies:
- IMDb. The world's most popular database for movies, TV, celebrity, video games and streaming online content was acquired by Amazon in 1998.
- Audible. Audible, a book and spoken audio content provider, was acquired by Amazon in 2008 for $300 million.
- Zappos. Amazon acquired this online shoe and clothing retailer in an all-stock deal worth $1.2 billion in 2009.
- Twitch. A social media and video game streaming platform, Twitch was purchased by Amazon for $970 million in 2014.
- Whole Foods. Food, beverage and organic grocery store chain Whole Foods was acquired by Amazon for $13.7 billion in 2017.
- Ring. Amazon took ownership of this home security and smart home company in 2018 for $1 billion.
- Zoox. An autonomous vehicles, robotics and transportation company was acquired as a wholly owned subsidiary by Amazon for $1.2 billion in 2020.
- Metro-Goldwyn-Mayer. Amazon acquired this film and TV studio for $8.5 billion in March 2022.
Amazon controversies and criticisms
Amazon has suffered a massive backlash over the years from multiple sources. The tech giant is also being held responsible for creating the Amazon effect -- the evolution and disruption of the retail market due to the company exhibiting monopolistic behaviors.
Following are a few concerns and allegations that Amazon has faced over time:
- Monopolistic and anticompetitive behavior. Due to Amazon's size and economies of scale, it has been outpricing local and small shopkeepers and is accused of displacing an open market with a privately controlled one. This is leading to the slow death of the brick-and-mortar store model built by companies such as Sears and J.C. Penney.
- Unfair treatment of workers. Amazon is frequently under the microscope for providing unfair work conditions in its warehouses, including treating workers as robots, providing low wages and creating unsafe work conditions.
- Huge carbon footprint. Over the past two decades, Amazon has been accused by environmental activists of having a staggering carbon footprint. Transport of any merchandise relies on oil, and since Amazon delivers anything everywhere, it leaves a long-lasting carbon footprint that automatically falls on its shoulders.
- E-waste. A recent investigation conducted by British television network ITV uncovered how Amazon is contributing to the world's e-waste crisis by destroying millions of unused or returned products. This also includes millions of electronics, such as phones, computers and TVs that are toxic to soil, water, air and wildlife.
- Counterfeit product listings. Amazon has been under scrutiny by brands, shoppers and lawmakers as counterfeiters have been listing and selling fake products on Amazon through its third-party marketplace. To crack down on counterfeit products on its site, Amazon destroyed 2 million counterfeit products sent to its warehouses and blocked 10 billion fake listings in 2021.
- Avoiding taxation. Edging fast toward a monopoly status, Amazon has been criticized for often avoiding tax payments despite making huge profits. According to a report by the Institute on Taxation and Economic Policy, the company avoided around $5.2 billion in corporate federal income taxes in 2021.
Amazon finances
According to a news release posted on Amazon's investor relations website, Amazon experienced a significant increase in net sales but a decrease in operating income in the first quarter of 2022.
Following are some notable statistics from the release:
- Net sales increased 7% to $116.4 billion in the first quarter, compared with $108.5 billion in the first quarter of 2021. Excluding the $1.8 billion unfavorable impacts from year-over-year changes in foreign exchange rates throughout the quarter, net sales increased 9% compared with the first quarter of 2021.
- Operating income decreased to $3.7 billion in the first quarter, compared with $8.9 billion in the first quarter of 2021.
- Net loss was $3.8 billion in the first quarter compared with net income of $8.1 billion in the first quarter of 2021.
Besides being recognized as a company with business interests in e-commerce, cloud computing and AI services, Amazon also offers an extensive list of subscription services. Learn about these services and the perks they offer.