Web 2.0
What is Web 2.0?
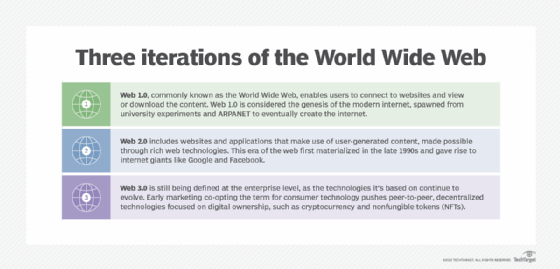
Web 2.0 are websites and applications that make use of user-generated content for end users. Web 2.0 is characterized by greater user interactivity and collaboration, more pervasive network connectivity and enhanced communication channels.
The term Web 2.0 was coined by information architecture consultant Darcy DiNucci in 1999 to differentiate the post-dot-com bubble. It was later popularized by O'Reilly Media during the Web 2.0 Conference in 2004.
Web 2.0 reflects the new age of the internet, which puts greater emphasis on social networking, cloud computing, higher participation levels and sharing information between internet users. While Web 2.0 doesn't signify a technical upgrade, it does reflect a shift in the way the internet is consumed. Social media sites, web apps and self-publishing platforms -- such as Facebook and WordPress -- gained popularity during this shift.

Web 1.0 vs. Web 2.0
Web 2.0 emerged because of certain limitations in the original version of the web, commonly known as Web 1.0. The following are the main differences between Web 1.0 and Web 2.0:
This article is part of
What is Web 3.0 (Web3)? Definition, guide and history
- Compared to Web 1.0, Web 2.0 offers a greater degree of collaboration among internet users, content providers and enterprises. It highlights user-generated content and offers interoperability among end users.
- Web 1.0 is all about content browsing and finding information. Originally, data was posted on websites, and users simply viewed or downloaded the content. Increasingly, users have more input into the nature and scope of web content and, in some cases, exert real-time control over it. Web 2.0 introduced writable data that enables users to write and provide input to the internet; information on the Web 1.0 platform is unalterable.
- With Web 2.0, websites enable community-based input, interaction, content sharing and collaboration. Types of social media sites and applications include forums, microblogging, social networking, social bookmarking, social curation and wikis.
- The information presented on Web 1.0 follows a linear format complete with lists and pages, whereas Web 2.0 follows a nonlinear format.
- Web 1.0 carries static pages, whereas Web 2.0 supports dynamic content, such as social media and user-generated content.
- Web 1.0 doesn't provide any user-to-server communication, whereas Web 2.0 offers virtual and interactive apps, such as online documents, cloud computing operations, pay-per-click ads and video streaming
- Web 2.0 provides increased functionality and availability of web application programming interfaces, which are internet-based web services with an Hypertext Transfer Protocol-based programming interface.
Web 2.0 examples
Since the advent of Web 2.0, the social aspects of internet communications have changed. Internet users can tag, share and tweet their opinions and engage in conversations.
The following are some popular examples of Web 2.0:
- Wikis. These websites enable web users to contribute, collaborate and edit site content. Wikipedia is one of the oldest wiki-based sites.
- Web applications. These include software as a service, web apps and cloud computing rather than locally installed programs and services.
- Mobile computing. Also known as nomadicity, mobile computing is the trend toward users connecting from wherever they may be. This trend is enabled by the proliferation of smartphones, tablets and other mobile devices, in conjunction with readily accessible Wi-Fi networks.
- Mashups. These include webpages or applications that integrate complementary elements from two or more sources.
- Social networking. This is the practice of expanding the number of business and/or social contacts by making connections through individuals. Social networking sites include Facebook, Twitter, LinkedIn and Instagram.
- Collaborative efforts. These are based on the ability to reach large numbers of participants and their collective resources, such as crowdsourcing, crowdfunding and crowdsource testing.
- User-generated content. This includes writing, images, audio and video content -- among other possibilities -- made freely available online by the individuals who create it.
- Unified communications (UC). UC integrates multiple forms of multimedia and cross-media message management functions controlled by an individual user for both business and social purposes.
- Social curation. This is the collaborative sharing of content organized around one or more themes or topics. Social web content curation sites include Reddit, Digg, Pinterest and Instagram.
- Blogs. Blogs can be single pages or groups of pages. They share various forms of text and stories with users and have the capability of receiving feedback from internet users, as well as gaining followers.
- Video hosting sites. Users can upload and share various audiovisual content on video hosting platforms, such as YouTube, as well as host their own video channels to grow a fan following.

Advantages and disadvantages of Web 2.0
Web 2.0 offers the following pros:
- Dynamic content. Web 2.0 showcases dynamic content that users can interact with and modify, unlike the restricted, read-only format of Web 1.0.
- Increased social networking. Web 2.0 enables people to participate in discussions, share information with friends and family, and stay in touch with people all around the globe.
- Ease of use and information sharing. With Web 2.0, users can easily use, update and share information with a few clicks. Any editing done on the internet can also be tracked.
- Improved marketability. Web 2.0 enables business owners to improve user experience by creating responsive websites. They can also promote their products online and increase their marketability through interactive advertisement campaigns.
- Improved quality of education. Web 2.0 opens doors to interactive learning and virtual classrooms. For example, students can extend their range of learning by using online calculators while solving math problems.
Web 2.0 offers the following cons:
- Cybersecurity risks. The increased online collaboration that comes with Web 2.0 puts users at increased risk of downloading malicious viruses and adware and getting afflicted by various cyber attacks, such as spam and phishing attacks.
- Information overload. Web 2.0 is a sea of information that grows incessantly. This can confuse readers and affect the reliability of the content, as the variety and volume of the information are vast.
- Ethics and credibility. Critics of Web 2.0 maintain that it makes it too easy for the average person to affect online content, which can impact the credibility, ethics and even legality of web content. The extent of data sharing and gathering also raises concerns about privacy and security.
Web 2.0 technologies
Most of the technologies used to deliver Web 2.0 are rich web technologies, such as Adobe Flash, Microsoft Silverlight and JavaScript, in addition to Ajax, RSS and Eclipse. Web 2.0 applications are often based on the decentralized download methodology that made BitTorrent so successful, in which each downloader of content is also a server, sharing the workload and making heavily demanded content more accessible than it would be in the centralized model, where demand can lead to overwhelmed servers and pages.
What is Manufacturing 2.0 and Enterprise 2.0?
The integration of Web 2.0 communication and collaboration applications into traditional manufacturing practices and processes has been dubbed Manufacturing 2.0. Manufacturing 2.0 takes typical Web 2.0 apps and services and incorporates them into every stage of development and production. The use of these technologies and tools facilitates greater collaboration and sharing and referencing of information in a business, ideally leading to better-thought-out design and more efficient production.
Similarly, the inclusion of Web 2.0 technologies into an enterprise's business processes, intranet and extranet is sometimes referred to as Enterprise 2.0. Most Enterprise 2.0 followers use a combination of blogs, social networking and social collaborative tools, as well as free, paid and homegrown technologies. The term Enterprise 2.0 was coined by former Harvard Business School Associate Professor Andrew McAfee in an MIT Sloan Management Review feature he named "Enterprise 2.0: The Dawn of Emergent Collaboration."
For more on Web 3.0, read the following articles:
10 core features of Web 3.0 technology
The biggest advantages and disadvantages of Web 3.0
The 10 most promising tools for Web 3.0 development
8 top Web 3.0 use cases and examples
5 ways Web 3.0 will impact digital marketing
How to become a Web 3.0 developer: Required skills and guide
Web 2.0 vs. Web 3.0
Web 2.0 is an advanced approach to the internet. However, certain setbacks, such as the security of personal data, can be found in its infrastructure. Web 3.0, or Web3, offers a promising improvement over Web 2.0 through its semantic infrastructure, privacy controls, advanced metadata system and integration with innovative technologies, including advanced analytics and artificial intelligence (AI).
The following features differentiate Web 2.0 from Web 3.0:
- Web 2.0 connects people, whereas Web 3.0 empowers individual users through decentralization technologies.
- Payments in Web 2.0 are made in fiat money. Web 3.0 uses encrypted digital currencies, such as Ethereum or Bitcoin, to fund transactions.
- Web 2.0 commonly uses programming languages, including Ajax, JavaScript, Hypertext Markup Language and Cascading Style Sheets 3, whereas Web 3.0 promotes a metaverse version, complete with machine learning, deep learning, the semantic web and decentralized technologies.
- With Web 2.0, the network controls information storage, which can cause access and privacy concerns. Web 3.0 solves this problem by enabling data to be exchanged in several locations simultaneously. Therefore, each entity keeps ownership of the data and shares it as they see fit.
The internet has come a long way -- from static Web 1.0 and interactive Web 2.0 to the emerging Web 3.0. Learn how Web 3.0 can revolutionize the internet and what it can mean for businesses.
