Ethereum
What is Ethereum?
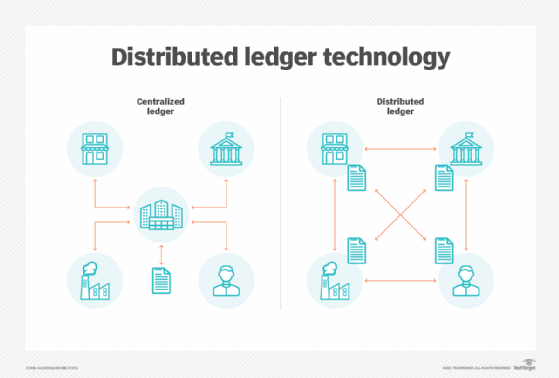
Ethereum is an open source, distributed software platform based on blockchain technology. It has its own native cryptocurrency called Ether and a programming language called Solidity. Blockchain is a distributed ledger technology that keeps a permanent, tamper-proof list of records. Ethereum is Bitcoin's main competitor.
Ethereum enables developers to build decentralized applications. Miners produce Ether tokens that can be used as a currency and to pay for usage fees on the Ethereum network. The platform also supports smart contracts, which are a type of digital contract.
Cryptocurrency researcher Vitalik Buterin first described Ethereum in a proposal in 2013 that suggested the addition of a scripting language for programming to Bitcoin. Ethereum's development was funded by an online crowdsale, which is Crowdfunding done through issuing cryptocurrency tokens, and the project came online on July 30, 2015.
How does Ethereum work?
Ethereum uses a blockchain network. The network is made up of nodes -- computers of volunteers who mine for the coin. The nodes produce the Ether tokens, and mining creates the cryptography upon which the currency is based. Because mining is a demanding use of a computer's resources, miners are rewarded with Ether.
The Ethereum platform offers the computationally complete Ethereum Virtual Machine (EVM). EVM executes scripts worldwide across its network of distributed public nodes. These nodes provide the processing power for decentralized applications developers create to run on the network. Developers may buy Ether to pay for the use of the network, or they can mine for the tokens themselves, becoming a part of the network. An internal mechanism called Gas sets the pricing of transactions on the network.
Smart contracts are carried across the network in the same blockchain that records the ledger of transactions for the Ether cryptocurrency. These digital contracts can have conditions that run on scripts until fulfilled. Ethereum has built-in mechanisms to detect when an agreement is not met. Smart contracts can be used to exchange things such as properties, money and stocks on the back of an Ether token.
From the time of Ethereum's creation in July 2015 until Sept. 15, 2022, Ethereum used the Proof of Work (PoW) model to execute and verify transactions with the cryptocurrency, using the Ethereum Mainnet blockchain. Proof of Work is a type of consensus algorithm that is used for verification and data integrity.
On Sept. 15, 2022, the Ethereum community completed what is known as "The Merge" with a transition to a Proof of Stake (PoS) consensus algorithm running on the Beacon Chain. For Ethereum and its users the benefit of moving to Proof of Stake (PoS), include potentially faster transaction speeds, while using less overall energy to process and validate transactions.
Ethereum and Ether: What is the difference?
Ethereum is a blockchain-based network. It is a platform that developers can use to build applications and program the smart contracts on which virtual currency is based. Like blockchain, it can be used for many different types of applications, including a number of financial uses.
Ether (ETH) is Ethereum's native cryptocurrency. It is bought and sold using the Ethereum platform. It is one of many cryptocurrencies that can be traded using the Ethereum network. It is also used to reward miners when they add blocks to a blockchain.
Ether supports the Ethereum network; it pays for computational services and applications built on the platform. It is described as the fuel that Ethereum runs on.
For example, an application running on Ethereum requires resources to function. Developers use Ether tokens to fund an application and support it on the network.
Ethereum applications and use cases
According to the Ethereum Foundation, Ethereum can be applied to codifying, decentralizing, securing and trading almost everything. Its uses include the following:
- crowdfunding
- financial exchanges
- company governance
- domain names
- intellectual property
- smart property with hardware integration
- voting
- contracts and agreements
Ethereum can be used for the following purposes:
- buy and sell cryptocurrencies like Ether and other fungible, Ethereum Request for Comments 20-validated tokens;
- host smart contracts and decentralized apps (dApps);
- carry out decentralized finance activities;
- exchange nonfungible tokens;
- power Ethereum-based enterprise software independently from the public Ethereum chain; and
- play Ethereum-based video games, where users can earn real cryptocurrency from playing the game.
Ethereum-based projects include the following two examples:
- Microsoft and ConsenSys partnership to build Ethereum Blockchain as a Service on Microsoft Azure. Microsoft's partnership with ConsenSys aims to provide enterprise clients and developers with a cloud blockchain development environment.
- Advanced Micro Devices and ConsenSys joint venture to build a network of data centers using Ethereum infrastructure.
Ethereum vs. Bitcoin: Key differences
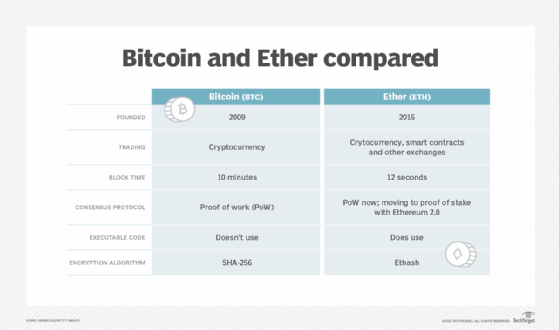
Bitcoin is the most used cryptocurrency, and Ethereum is second to Bitcoin. The word Bitcoin is used to refer to the blockchain network and to the currency itself. Ethereum refers to the network, and Ether refers to the corresponding cryptocurrency.
Some other differences between the Bitcoin and Ethereum networks are the following:
- Abbreviation. BTC refers to Bitcoin currency, and ETH refers to Ether.
- Inception. Bitcoin is the world's first cryptocurrency, created in 2009. Ethereum came next in 2015. Ether was originally intended to complement Bitcoin, but the two coins ended up competing.
- Trades enabled. Bitcoin exclusively trades in cryptocurrency, whereas Ethereum offers several methods of exchange, including smart contracts.
- Block time. The average block time for an Ether transaction to be confirmed is about 12 seconds compared with 10 minutes for Bitcoin.
- Consensus system. Bitcoin operates on a proof of work (PoW) system, which is used for validating transactions. Ethereum used PoW for the first 7 years of its existence, and transitioned to a proof of stake (PoS) based system as part of the Ethereum 2.0 upgrade with the Merge on Sept. 15, 2022.
- Executable code. Ethereum transactions can be affixed with executable code, whereas Bitcoin network transactions cannot. This enables decentralized applications and conditional transactions, which are transactions that take place only when certain conditions are met.
- Encryption type. The two blockchain networks run different encryption. Ethereum runs Ethash, while Bitcoin runs Secure Hash Algorithm 256 (SHA-256) encryption.
Benefits of Ethereum
Many benefits of blockchain technology apply to Ethereum, including the following:
- Decentralization. Ethereum is decentralized, so there is no interference from third-party cloud providers. It uses blockchain, which enables peer-to-peer transactions. Users can exchange value or store data without the need for an intermediary unlike some other software applications, which often require trust in a central authority.
- Availability. Because Ethereum is decentralized, there is no downtime if a node goes down. Other computing models use centralized servers and can suffer performance issues if interrupted.
- Privacy. When using the network for exchanges, users can remain anonymous. They do not need to enter their personal credentials to use an Ethereum application.
- Security. Like any decentralized blockchain-based network, Ethereum is designed to be unhackable. Hackers would have to control most of the network nodes to exploit the network.
- Permissionless. Ethereum is a permissionless blockchain, meaning that everyone can participate. This contrasts with permissioned blockchains, which are limited to designated participants.
- Less ambiguity. The hardcoded smart contracts that serve as the basis for trade and agreement on Ethereum ensure stronger contracts. For example, a freelancer that gets work through a dApp on Ethereum could enter into a smart contract with a hardcoded rule that states, "X compensation will be released when Y work is completed." This differs from normal contracts, which require interpretation and follow-through.
Drawbacks of Ethereum
Two criticisms of the Ethereum platform are the following:
- Resource-intensive. Ethereum's current use of the PoW consensus protocol is an energy-intensive way to ensure the nodes of the networks agree on the state of all information recorded on the blockchain. All smart contracts are stored on all of the nodes of the blockchain, and each node calculates every smart contract simultaneously. The move to the proof of stake model is intended to help mitigate concerns of resource utilization. PoS requires less energy than a PoW model, though energy is still consumed to validate and execute transactions.
- Security. The PoW protocol also raised potential security issues. Vulnerabilities in smart contracts on the public blockchain are visible to all and may take longer to fix than to exploit.
The concerns around resource utilization and security were largely addressed when Ethereum moved from a PoW consensus algorithm to a PoS consensus mechanism on Sept. 15, 2022. PoS is expected to improve the blockchain energy efficiency of Ethereum by giving more mining or block validation power to miners with more coins. The result is fewer nodes doing more of the work. It also does not require special equipment -- just the amount of coins necessary to mine and an internet connection.
A downside of this approach is that more mining power is concentrated among a smaller group of people. This enables more manipulation and collaboration on the network.
Other downsides to Ethereum include the following:
- high barrier to entry;
- costly to develop on; and
- challenging to use for anyone unfamiliar with the technology.
Ethereum 2.0
Ethereum 2.0 -- also known as ETH 2.0 or Serenity -- is a major upgrade to the Ethereum network that occurred in 2022. The goal is to increase transaction throughput for the network, from 15 transactions per second to tens of thousands of transactions per second. It will do this by splitting up workloads among many parallel blockchains that share a common consensus PoS blockchain. Maliciously tampering with any single chain would require tampering with the common consensus, an action too costly to be worth it for any threat actor.
The move to ETH 2.0 is underway. It's three phases are as follows:
- Phase 0 -- The Beacon Chain. Launched Dec. 1, 2020, this created the PoS blockchain that acts as the central hub of Ethereum 2.0.
- Phase 1 -- The merge. This will merge the Beacon Chain with the original Ethereum Mainnet network, marking the full transition from PoW to PoS. The merge occurred on Sept. 15, 2022.
- Phase 2 -- Shard chains. This will spread the network's workload across 64 new networks, with Ethereum 1.0 expected to become one the shards of Ethereum 2.0. This is planned to launch in 2022.
PoS enables miners to mine based on which miners are willing to stake a certain number of ETH coins. As of Nov. 30, 2021, that number was 32 ETH.
Ethereum Classic
Ethereum Classic is the name of the original Ethereum blockchain.
In 2016, a set of smart contracts on a platform known as The DAO, a decentralized autonomous organization, raised a record $150 million in an online crowdsale, the name of the crowdfunding method used to help support Ethereum.
Shortly after that money was raised, an anonymous hacker stole $50 million DAO tokens. This resulted in the crypto community's decision to fork the network and to reappropriate the stolen funds. Forking is when the source code of an old open source program is used to create a new one.
The network fork split the Ethereum blockchain into two: the original Ethereum Classic and Ethereum, the new one. This created competition between the two networks and became known as a hard fork. A hard fork is when nodes on the newest version of a blockchain no longer accept older versions.
History of Ethereum
Key dates in the development of Ethereum include the following:
- 2013. Ethereum was first described in Vitalik Buterin's white paper in late 2013 with the goal of developing decentralized applications. Buterin wanted to improve blockchain application development so that real-world assets, like property and stocks, could be attached to a blockchain. Buterin chose the name Ethereum partly because it contained the word ether, which refers to a hypothetical invisible medium that enables light to travel.
- 2014. The formal development of the software began, and EVM was specified in a paper by Gavin Wood, then the chief technology officer of Ethereum Switzerland GmbH.
- 2015. Ethereum created its genesis block, marking the official launch of the platform.
- 2018. Ethereum took second place to Bitcoin in terms of market capitalization.
- 2021. A major network upgrade, named London, included Ethereum Improvement Proposal 1559 and introduced a mechanism for reducing transaction fee volatility. ETH's price rose to an all-time high of $4,865.57 in November 2021.
- 2022. With the Merge, the cryptocurrency moved to Ethereum 2.0 and shifted from a PoW consensus model to PoS.
The inventions of Bitcoin and Ethereum make up a large piece of the blockchain's history. Learn more about blockchain and how it's being used for business in this enterprise guide.