GSA IT Schedule 70
What is GSA IT Schedule 70?
GSA IT Schedule 70 is a long-term contract issued by the U.S. General Services Administration to IT hardware, software and services vendors. It enables U.S. federal, state and local governments to procure IT products from leading and preapproved industry vendors for their specific requirements.
It is one of the largest government contracts awarded to vendors looking to sell IT products, software and professional services to U.S. government entities.
While the contract is commonly called IT Schedule 70, GSA defines it in the following way:
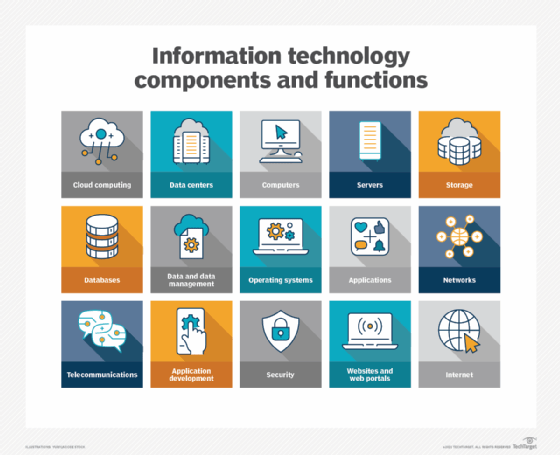
Information Technology (IT) is one of 12 categories of products and services that can be offered on the GSA Multiple Award Schedule (MAS) Contract. Formerly referred to as GSA Schedule 70 or GSA IT70, this category covers a broad range of IT hardware, software, and services.
It is an indefinite delivery, indefinite quantity contract, meaning there are no orders or a set amount of dollars attached to it. Rather, it acts as a procurement vehicle for government buyers and a "license to hunt"-type channel through which sales can flow between vendors and buyers. The contract term is fixed, but the deliverables are not. So, any U.S. government purchaser can order an unlimited amount of IT products or services from an approved vendor during the term of the contract.
Large IT product categories under GSA IT Schedule 70
Twelve categories of products and services can be offered under GSA's MAS. IT Large Category is one of these categories -- Category F -- and includes products and services in all these subcategories:
- F01: Electronic commerce (e-commerce).
- F02: IT hardware.
- F03: IT services.
- F04: IT software.
- F05: IT solutions.
- F06: IT training.
- F07: Telecommunications.
The products in each subcategory are associated with a unique special item number (SIN). For example, e-commerce products are mapped to SIN 54151ECOM, while SIN 611420 is the unique SIN for IT training offerings. Multiple SINs are mapped to the offerings under IT hardware, IT services, IT software, IT solutions and telecommunications. Thus, the SIN for purchasing new electronic equipment is SIN 33411, but purchasing refurbished equipment is SIN 33411REF. Both subcategories fall under the IT hardware category.
The other subcategories include SINs for specialized offerings in all the following areas:
- Highly adaptive cybersecurity services.
- Health IT services.
- IT professional services.
- Software licenses.
- Software maintenance services.
- Cloud computing services.
- Identity, credentialing and access management.
- Automated contact center solutions.
- Commercial satellite communications solutions.
All the SINs are listed on the GSA's website on the MAS IT page, enabling government buyers to see what they can buy and initiate the purchase process for their IT requirements. Furthermore, they can use the GSA's Cooperative Purchasing Program to purchase the products and services they need through specific SINs.
Who can buy IT products and services under GSA IT Schedule 70?
GSA IT Schedule 70 is most commonly used to sell IT products and services to the U.S. federal government. The contract and program enable federal agencies and departments, such as the Department of Defense and Department of Homeland Security -- among dozens of others -- to save time when choosing vendors and then get innovative products through a simplified process. In addition, state, local and municipal agencies also can use GSA IT Schedule 70 to purchase IT products and services from those preapproved vendors through the Cooperative Purchasing Program.
Any IT vendor can apply for a GSA IT Schedule 70 contract. But this doesn't mean that only one vendor can get the contract for a particular SIN or buyer. There is no upper limit on the number of vendors that can be awarded the contract, so multiple companies can receive the contract to sell the same product or service to a government agency.
Benefits of GSA IT Schedule 70 for IT vendors and government buyers
A GSA schedule contract enables IT vendors to expand their government sales, while cutting down on their administrative costs. It also enables them to get a competitive advantage in the public sector and position themselves as a "prime contractor" offering innovative IT products and services. Since the U.S. government agencies are reliable buyers, vendors who get a GSA IT Schedule 70 contract can expect to earn significant revenue from their contracts. In fiscal year 2022, the 6,000 IT companies holding a GSA MAS contract under the IT Large Category earned billions of dollars. For all these reasons, this contract is highly sought-after by IT vendors.
In order to win the contract, vendors undergo a rigorous application process, including the negotiation of fair and reasonable prices with GSA. Once they are approved by GSA, government buyers can purchase the products they need from them.
Purchasing from preapproved vendors under the contract enables buyers to cut through red tape and reduce their own administrative costs. One reason is that they don't have to vet vendors to ensure that the vendors are in compliance with all applicable laws and regulations because GSA does it for them.
The sales process is also shorter, so buyers can receive goods and services faster and fulfill their specific requirements by reaching implementation of the new technology in less time. Finally, awarding a GSA IT Schedule 70 contract to an IT vendor signifies that GSA has determined that the vendor's pricing is fair and reasonable so buyers can expect to get high-quality offerings at a reasonable cost.
Eligibility and process to get a GSA IT Schedule 70 contract
In theory, any IT company can apply for a contract under GSA IT Schedule 70. But, practically, companies must first check their eligibility before applying. For example, they must have healthy financials in terms of sales, profits and losses that they can prove to GSA. Also, their offerings must fit into one of the pre-decided subcategories and SINs.
Finally, the IT products offered by the vendor and listed on the contract must be manufactured or "substantially transformed" in the United States or a country designated by the Trade Agreements Act (TAA). The list of TAA designated countries is provided by the Federal Acquisition Regulation and includes many countries in South America, Africa and Europe, in addition to several countries in Asia (Japan, South Korea, etc.) North America (Canada and Mexico), and Oceania (Australia, New Zealand, etc).
In order to get a GSA IT Schedule 70 contract, potential vendors must meet the eligibility criteria mentioned above. They must also do the following:
- Prepare and upload a GSA offer, which consists of roughly 30 documents.
- Clarify the questions that may be asked by a GSA Contracting Specialist -- or Officer -- from the GSA's Schedule 70 department.
- Negotiate discounts, terms and conditions with GSA.
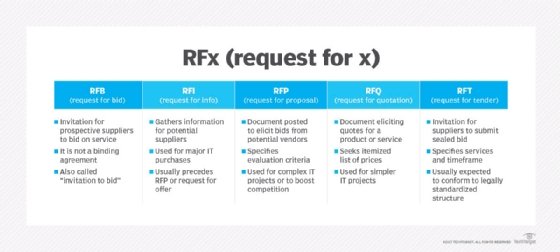
Once the contract is awarded, the vendor can check requests for proposal and requests for quote on GSA's eBuy portal and submit contract offers to the portal. Vendors can also scale up their business development and marketing efforts to expand their government customer base.
