Gartner Hype Cycle
What is the Gartner Hype Cycle?
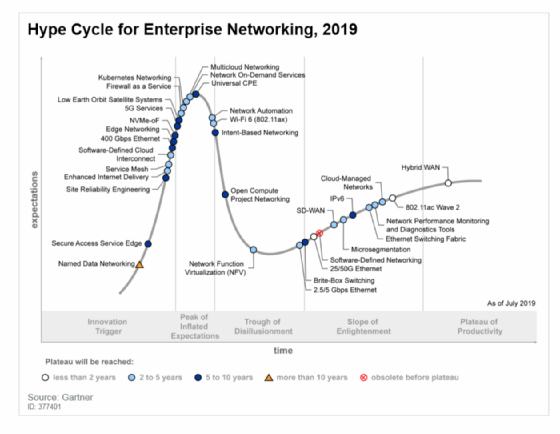
The Gartner Hype Cycle is a graphical representation of the lifecycle stages a technology goes through from the initial development to its commercial availability and adoption, as well as its eventual decline and obsolescence. It was developed by the research company Gartner.
The hype cycle's stages are often used as reference points in marketing and technology reporting, as well as to guide technology decisions by their level of comfort with risk. Each stage of the cycle is associated with its own risks and opportunities.
What are the 5 phases of the Gartner Hype Cycle?
The five phases of the Gartner Hype Cycle are described below.
Phase 1: Technology Trigger
This is the stage when technology is first introduced to the public. It can come from emerging markets, research labs, think tanks and universities. There is usually a lot of hype about the product and its potential applications.
There might be prototypes, but there are often no functional products or market studies. The potential spurs media interest and sometimes proof-of-concept demonstrations.
Phase 2: Peak of Inflated Expectations
At this point, media outlets and industry analysts have picked up on the new technology and its potential applications. This leads to an increase in enthusiasm for it and often unrealistic expectations of what it will do.
Phase 3: Trough of Disillusionment
As reality sets in, it becomes apparent that the initial enthusiasm was misplaced when many limitations become clear or issues arise with the technology. This leads to a decrease in enthusiasm as people question its viability and potential applications.
Phase 4: Slope of Enlightenment
At this stage, more realistic expectations emerge about the product's capabilities, limitations and potential use cases. People are becoming more knowledgeable about what it can accomplish, allowing for more effective implementation in different scenarios.
Phase 5: Plateau of Productivity
The final phase is when the product reaches maturity and widespread adoption in the market. At this point, people are familiar with it and have a good understanding of how to use it effectively. This leads to a higher level of productivity as users become more proficient at leveraging its features for their benefit.
What is the Gartner Hype Cycle used for?
The Gartner Hype Cycle is used to assess the maturity and potential of emerging technologies. It provides a framework for understanding the various stages in technology adoption and can give insights into where investments should be made or avoided.
Decision-making
By providing an objective assessment of a technology's current status, its prospects for success and where it might fit into the larger market context, the hype cycle helps businesses make informed decisions about investing in emerging technologies.
This type of analysis can help save companies time, money and resources when researching new technologies. It can also help in predicting future trends in technology innovation.
Risk management
The hype cycle can also be used as a guide to inform technology decisions by providing an understanding of what level of risk is associated with each stage in the cycle. By being aware of these risks, businesses can make more informed decisions when considering new investments and technology solutions.
For example, if a technology is in the Peak of Inflated Expectations stage, businesses should know it might not be as reliable or effective as initially thought and thus require more research before investing. On the other hand, technologies that are in the Slope of Enlightenment stage can provide more reliable and proven solutions with less risk.
Thought leadership
The hype cycle also serves as a useful reference point for media outlets that want to deliver accurate reporting on new products or services by providing context and insight into the commercial viability of such products or services.
This can help media outlets better serve their readers and viewers by providing more accurate information about emerging technologies.
What other considerations should organizations make when investing in technology?
With any new technology, the Gartner Hype Cycle can be a useful tool for understanding what stage it is in and how viable it might be as an investment or implementation.
However, businesses should also consider other factors, such as current market trends, competition, customer feedback, scalability potential and more. Ultimately, the decision to invest in technology will depend on a variety of factors related to the company's needs and resources.
The Gartner Hype Cycle is just one tool among many that businesses can use when evaluating emerging technologies. It can provide insights into where investments should be made, but it should always be used with other analysis techniques to ensure the making of informed decisions.
Learn about balancing the benefits with the risks of emerging technology and how emerging technology fits in your digital transformation.