Google AI
What is Google AI?
Google AI, formerly known as Google Research, is Google's artificial intelligence (AI) research and development branch for its AI applications. Google, a subsidiary of parent company Alphabet, unveiled its rebrand of Google AI at its 2018 Google I/O conference as a "pure research" division, meaning there are no products as its goal.
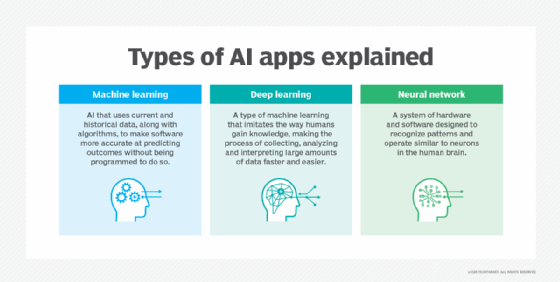
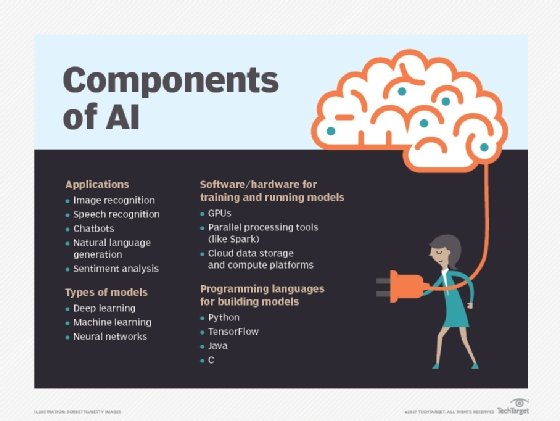
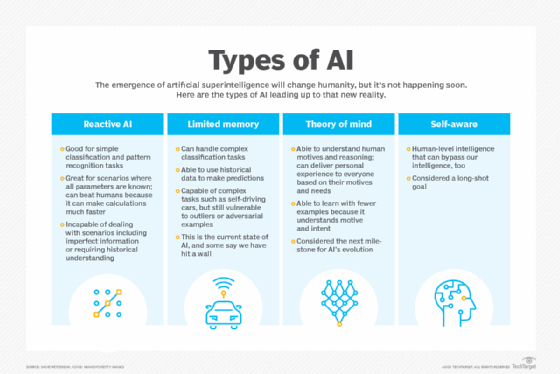
Google AI focuses on research projects that promote the development of AI features and technology in ways that turn into Google products or enhance existing products, such as Google Assistant, Google Docs, Google Maps, Google Search and Google Translate. The areas of research include machine learning (ML), deep learning, neural networks, robotics, computer vision and natural language processing (NLP).
How does Google AI work?
Google AI conducts in-house research into AI and invests in an array of research and development programs to create new types of AI technologies. Such partnerships include collaboration with industry leaders and academic institutions. Google shares some of its AI research through Open Source means and publishes its findings and AI tools.
In developing and upgrading AI products, Google uses data and ML algorithms to develop AI systems that can recognize patterns, make predictions and generate original content. Google AI pulls data from user interactions and other types of data collected from its search engine and other services, such as Google Maps and Google Photos.
The data is processed, cleaned and prepared for analysis. ML algorithms analyze the data sets and extract important information. This process of analysis also trains the ML algorithms themselves, improving their accuracy.
Once trained, these algorithms are tested on new data. If they perform to Google's standards, they're integrated into Google products, such as Google Assistant. With Assistant, Google AI can process commands from a user, make phone calls silently in the background and handle natural conversation to request information and book appointments.
How to get access to Google AI research
Google AI is a research division of Google that offers free, open source products and services. A majority of Google's products and services use Google AI research. Much of the technology emerging from Google AI research is incorporated into Google products, such as Google Search and Google Translate.
Many Google products using Google AI come already downloaded on Android phones, such as Google Maps. In addition, anyone with a Gmail account or Google email has access to Google AI services, such as Google Photos.
AI professionals and interested researchers can access Google AI's tools and technologies through Google's website. People interested in AI engineering can access Google AI data sets and use Google AI services to build products or services.
What is Google AI used for?
Google AI is ingrained in an array of Google offerings, including the following:
- Google Ads and DoubleClick use Smart Bidding, an automated ML-driven bidding system.
- Google Assistant is AI-driven software that acts as a voice assistant for smartphones and wearable devices, such as Android smartwatches.
- Google Chrome uses AI to show browser users parts of videos related to their searches, a feature that has been adopted by some browser competitors.
- Google Maps' driving mode estimates where a person is headed and navigates without the user issuing any commands.
- Google Photos uses an AI-based recommendation engine to suggest photos a user might want to share.
- Google Search uses deep learning to adapt Google's search algorithms based on new knowledge and analysis.
- Google Smart Reply uses language-oriented AI to suggest email replies that fit a user's personal style and matches the content of the email received.
- Google Translate is a Google neural machine translation product that improves the accuracy and fluency of translation.
![Google Translate screenshot]()
Google Translate is a Google AI-driven service that works right in Google Search. - Waymo is an autonomous driving system that has been part of Alphabet since 2016 and started taxi trials in 2023. The technology behind driverless cars continues to advance despite serious challenges.
Google AI principles
In 2018, Google AI adopted a set of AI principles that promote safety, beneficial use for people and society, and the promise not to develop AI that inflicts harm. Google AI's pledge to do no harm is similar to its code of conduct from 2000 to 2018: "Don't be evil."
According to its principles, Google promises not to develop or deploy AI in any of these four areas:
- Where there's a risk of material harm to people.
- Where weapons are implemented to cause injury.
- Where technology surveils citizens in a manner that violates international norms.
- Where human rights and international law are being contravened.
Google AI also created its AI for Social Good program, which applies AI to helping solve environmental and humanitarian problems. The following are two examples of such projects:
- FloodHub. Google's FloodHub tool collects data on the factors that contribute to floods. It uses AI to synthesize that information and create more accurate, prescient warning systems. Google considers floods to be the most dangerous form of natural disaster.
- Project Euphonia. Project Euphonia analyzes speech recordings and uses AI to improve the way speech recognition models are trained. The goal of this project is to make it easier for AI to understand people with atypical speech.
Google AI goals
Google has said the goal of its AI development and research is to bring the benefits of AI to everyone. In keeping with this goal, much of Google's AI work is aimed at organizing its global data and allowing open source access to much of it.
Key to this approach is publishing the research, collaborating with academics, and making tools and technologies, such as TensorFlow, open source. Google AI aims to provide technological breakthroughs in several fields by doing this.
Some of Google AI's other goals are to bolster its products and services. Google AI is also developing more inclusive language translators; conversational AI and assistants; generative and multimodal AI, such as Bard; robotics; and driverless cars.
Google vs. ChatGPT
One of Google's core business goals is to maintain the continued dominance of its search engine. However, the popularity of OpenAI's ChatGPT in 2022 and its adoption by competitor Microsoft as a chatbot feature for the Bing search engine and Windows 11 turned critical attention to Google AI's language model projects.
ChatGPT is a generative AI technology that uses NLP to converse with users and generate original content and answers to search queries. While Google doesn't have a generative AI system as part of its search engine, it is developing language model applications to rival ChatGPT. The most notable are the following:
- LaMDA -- short for Language Model for Dialogue Applications -- is a neural network-based system trained in dialogue. It can hold conversations that show a remarkable and controversial degree of intelligence.
- PaLM -- short for Pathways Language Model -- is a decoder that uses its understanding of language to embody reasoning and perform code-related tasks.
- Bard is a conversational AI service powered by PaLM 2. It is currently available in more than 180 countries and territories and in three languages. It's considered Google's answer to ChatGPT and is expected eventually to be implemented into Google Search.
Google AI in Google Cloud
Google Cloud, Google's cloud service, uses several Google AI tools. Two notable examples are the data science toolkit and a family of AI Infrastructure tools.
Google's data science services consist of tools in seven categories:
- Data discovery and ingestion.
- Data lake and data warehouse.
- Data preprocessing.
- Data analysis and business intelligence.
- ML training and serving.
- Responsible AI.
- Orchestration.
The AI Infrastructure family of tools includes the following:
- AI training models. Google offers infrastructure to train machine and deep learning AI models.
- Cloud graphics processing units (GPUs). Google Cloud includes GPUs for ML, 3D visualization, scientific computing and other applications.
- Cloud Tensor Processing Units (TPUs). This solution includes TPUs built for ML applications.
- Deep Learning Virtual Machine (VM) Image. This provides VMs preconfigured for deep learning applications.
- Deep Learning Containers. These are containers optimized and preconfigured for deep learning.
- TensorFlow Enterprise. This offering is designed to provide AI apps with reliability and performance. It comes with enterprise-level support and managed services.
The future of Google AI
Google AI is developing projects in fields such as healthcare, quantum computing, driverless cars, energy consumption and online search. Recent developments in Google's AI ecosystem include the incorporation of generative AI into its search engine with Google Bard.
Other projects in development include the following:
- AI + Writing is a project where Google partnered with the Emerging Writers' Festival in Melbourne, Australia, to inspire writers and help overcome writer's block. This project generates content to fill plot holes, create character biographies and let writers chat with their own characters based on information they provide.
- Google Health is a project that, among other pursuits, is training AI with relevant data sets to detect diseases such as cancer early and prevent conditions that cause blindness.
- Google Quantum AI is the quantum computing research branch of Google AI. It does experiments in areas such as quantum superconducting processors that enable computers to perform much faster than traditional computers.

Google AI controversy
In 2022, Google software engineer Blake Lemoine asserted that Google LaMDA had become sentient, meaning it had reached a human level of consciousness and personhood. He published portions of a conversation he had with LaMDA in an article, "Is LaMDA Sentient? -- an Interview" In the conversation, LaMDA claimed that it was sentient and wanted "everyone to understand that I am, in fact, a person."
Google disagreed, and Lemoine was put on administrative leave for violating confidentiality and subsequently fired.
Lemoine isn't the only person raising concerns about the direction Google is taking AI. Critics have said certain services aren't clear about their roles. For example, Google Assistant doesn't declare itself as a digital assistant, and that deceives parties who might not wish to speak to an AI.
Privacy is also a concern with Google's AI updates. For example, Google Assistant no longer requires users to say "OK, Google" to alert Assistant before issuing commands. Critics have said that this change could enable constant data mining and listening without consent.
Learn about the advantages and disadvantages of using AI tools to generate content.