Google Docs
What is Google Docs?
Google Docs, first released in 2006, is a free web-based word processor in which documents can be created, edited and stored as part of the Google Docs Editors suite of free web applications. The cloud-based productivity platform also includes Google Sheets, Google Slides, Google Drawings, Google Forms, Google Sites and Google Keep.
Google Docs users can import, create, edit and update online documents in various fonts and file formats that can be accessed from any computer with an internet connection and web browser.
Users can also access documents from mobile devices with Android, Chrome or iOS operations systems, and create new documents to work on from their device.
How is Google Docs used?
To use the software, users must create a free Google account. This will also give them a Gmail email address. To begin, simply go to docs.google.com or by navigating to Google Docs from their Gmail or Google Drive online storage account.
General access is free for all. However, Google's business offering, Google Workspace (formerly G Suite), offers these apps with additional business-focused functionality as part of a monthly subscription.
The benefits of Google Docs
One of the main benefits of using Google Docs is that collaborators can see the revision history of any changes made to Google documents and when those alterations were done in the version history.
Users can also control who sees their work so privacy can be maintained in a business or personal setting. It also offers built-in commenting tools that let users discuss changes and work together as they're being made.
Additionally, because documents are stored online and can also be stored on users' computers, there is no risk of total data loss as a result of a localized catastrophe.
Thus, Google Docs is an ideal word processing option for businesses, blog authors or students who use it for writing assignments.
Google Docs vs. Microsoft Word
While Google Docs and Microsoft Word are both used for word processing, there are some key differences between the two applications.
Google Docs is a free web-based application, while Microsoft Word is part of the Microsoft Office suite, which must be purchased in order to use it.
Users can store Microsoft Word documents or Google Docs offline or in the cloud via Microsoft OneDrive for the former and Google Drive for the latter.
Lastly, both Google Docs and Microsoft Word include real-time collaboration features built-in. This means that two or more people can collaborate on and share documents in real time.
Other Google alternatives to Microsoft Office products:
As mentioned above, the Google Docs app is only one of several Google apps available to help increase productivity and facilitate business operations. Here are just a few examples of other apps in its product suites:
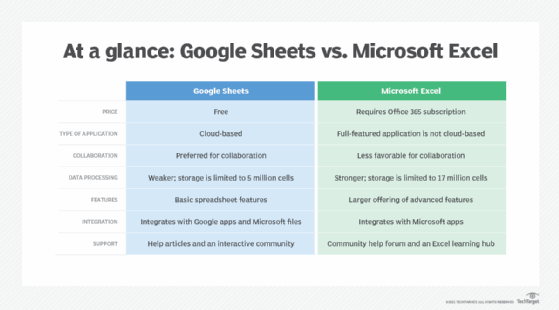
- Google Sheets is Google's free equivalent to Microsoft Excel, which provides functionality to create and edit spreadsheets in real time.
- Google Slides is the equivalent of Microsoft PowerPoint and includes a variety of templates, transitions, themes and more.
- Google Drive is Google's cloud-based file storage system similar to Microsoft OneDrive.
- Google Calendar is Google's time management application that can be used to schedule appointments, set reminders and more.
- Google Hangouts is Google's messaging platform that can be used for text, audio and video conversations.
- Google Forms is Google's form maker that can be used to create surveys, questionnaires, quizzes and more.
Issues with Google Docs
The cloud-based nature of Google Docs has given rise to concerns among some authors that their work may not be private or secure. While Google does take steps to protect user privacy, data security cannot be guaranteed.
For example, Google Docs may become unavailable or users may lose access if Google experiences downtime, and Google can't guarantee the data will be retrievable when services are restored.
Additionally, Google's algorithms that monitor for spam and inappropriate content may flag legitimate documents as offensive, causing them to be removed from Google Drive.
You can try to avoid these issues by reading Google's Terms of Service regarding unacceptable material and how to secure your Google account using two-factor authentication and strong passwords.
While Google Docs has a number of benefits, it is ideal for collaborative projects or individuals who need real-time collaboration features built into their word processors.
