IMAP (Internet Message Access Protocol)
What is IMAP (Internet Message Access Protocol)?
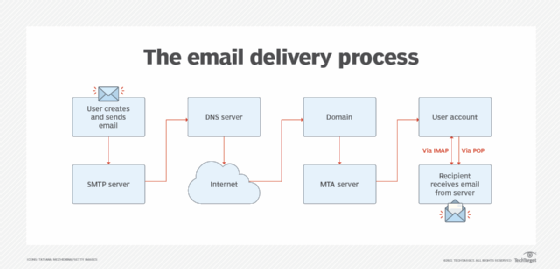
Internet Message Access Protocol, or IMAP, is a standard email retrieval (incoming) protocol. It stores email messages on a mail server and enables the recipient to view and manipulate them as though they were stored locally on their device(s).
IMAP enables users to organize messages into folders, flag messages for urgency or follow-up, and save draft messages on the server. Users can also have multiple email client applications that sync with the email server to consistently show which messages have been read or are still unread.
How does IMAP work?
As an incoming email protocol, IMAP functions as the intermediary between the email server and email client. When users read an email using IMAP, they read them off the server. They don't actually download or store the email on their local device. This means that the email is not tied to a particular device, and users can access it from any location in the world using different devices, such as the following:
- desktop PC
- laptop
- smartphone
- tablet
These are the general steps and processes involved in an IMAP operation:
- When a user signs into the email client -- e.g., Microsoft Outlook -- the client contacts the server using IMAP.
- The connection is made on a specific port.
- The headers of all emails are displayed by the email client.
- IMAP only downloads a message to the client when the user clicks on it; attachments are not automatically downloaded.
- Users can check their messages much more quickly with IMAP than with other email retrieval protocols, like Post Office Protocol 3 (POP3).
- Email messages remain on the server unless the user explicitly deletes them.
An IMAP server listens on port number 143, while IMAP over Secure Sockets Layer (SSL)/Transport Layer Security is assigned port number 993.
IMAP, TCP and HTTP
Most modern client-server protocols operate between a web browser and a server or an app and an application programming interface (API). APIs are implemented on top of the base protocol, Hypertext Transfer Protocol (HTTP). HTTP is implemented on top of TCP, which ensures that data packets are delivered to their intended destination.
Like HTTP, IMAP is also implemented on top of TCP. It works based on different types of requests, known as IMAP commands. A command in IMAP is similar to a request in HTTP. It either tells the server to do something or asks the server for some information.
An IMAP command generally looks like this:
<tag> <command> [<arg1><arg2>…]
In the early '90s, when network connections had low bandwidth, HTTP was important for IMAP.
Adding email accounts to IMAP
When an email account is added to an email app or client, it will usually attempt to set it up with IMAP access. In that case, user inputs are not required. But, if the account is already set up for POP3, the client may have difficulty adding the account to IMAP.
If users still need to configure their account with IMAP, they need to get the names of the POP3 and Simple Mail Transfer Protocol (SMTP) -- outgoing mail -- server from the email provider and then enter this information into the client:
- IMAP server: imap.<name of service>.com
- POP3 server: pop.<name of service>.com
- SMTP server: smtp.<name of service>.com
Differences between IMAP and POP3
Like IMAP, POP3 is also a client-server email retrieval protocol. However, there are differences between the two protocols. With POP3, email is saved for users in a single mailbox on the server. It is moved from the server to their device when the mail client opens.
While POP3 can be thought of as a "store-and-forward" service, IMAP can be thought of as a remote file server, since the user can store the email on the server and access it from any device or location as needed.
Advantages and limitations of IMAP
Advantages
Most implementations of IMAP support multiple logins. This enables users to simultaneously connect to the email server from different devices. For example, users simultaneously could access their email with an Outlook app on an iPhone, as well as an Outlook desktop app.
Multiple accesses are not possible with POP3, where downloaded emails disappear from the server and, therefore, cannot be accessed from a different device later. So, POP3 is only suitable when users access their email from the same device every time.
IMAP provides greater access flexibility for users who travel often or need to check their email from different devices or locations. The details for how to handle multiple connections are not specified by the protocol, but are instead left to the developers of the mail client.
In brief, the advantages of IMAP are the following:
- emails accessible from multiple devices;
- fast and efficient access;
- a single mailbox can be shared by multiple users;
- users can organize emails on the server by creating folders and subfolders;
- support for email functions, like search and sort;
- IMAP server supports IDLE extensions (push mail) so the email is displayed in the inbox as unread, eliminating the need to set up a polling interval or requiring users to first click on receive; and
- can be used offline.
Limitations
Even though IMAP has an authentication mechanism, the authentication process can easily be circumvented by anyone who knows how to steal a password by using a protocol analyzer because the client's username and password are transmitted as cleartext.
In an Exchange Server environment, administrators can work around this security flaw by using SSL encryption for IMAP.
In general, IMAP is a popular email retrieval protocol. Its popularity is growing due to the proliferation of mobile devices, such as smartphones and tablets. IMAP is ideal for those who need to access their email on the go or using different devices.
