ISO 14000 and 14001
What are ISO 14000 and ISO 14001?
ISO 14000 is a series of environmental management standards developed and published by the International Organization for Standardization (ISO). The ISO 14000 standards provide guidelines and frameworks for organizations that need to systematize and improve their environmental management efforts.
The ISO 14000 and 14001 series of standards aren't designed to aid the enforcement of environmental regulations or policies. Compliance with these ISO standards is voluntary. However, compliance is desirable for several reasons, including considerations such as business success, stakeholder approval, competitive standing and reputational effects. The ISO Technical Committee that supports ISO 14000 is TC 207.
ISO 14001 is the most important part of the ISO 14000 family of standards. It provides the requirements for an environmental management system (EMS).
Why is ISO 14001 important?
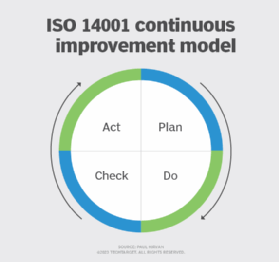
ISO 14001 specifies what's required to implement an effective EMS for organizations of all sizes. An EMS is a systemic approach to handling environmental performance issues within an organization. The management system standard uses the plan-do-check-act (PDCA) continuous improvement model. PDCA is a four-step lifecycle assessment aimed at bringing about system and process improvement and change.
Any organization, whether in the public or private sectors, can use ISO 14001 to establish a program to meet its environmental responsibilities. The benefits of ISO compliance include establishing an ongoing capability to ensure compliance with environmental objectives.
How does ISO 14001 work?
ISO 14001's PDCA cycle methodology involves the following four steps:
- Plan. This part of ISO 14001 involves establishing environmental processes and objectives to achieve the goals of an organization's environmental policies.
- Do. This part of the cycle involves establishing procedures and processes to implement and operate elements of the ISO 14001 standard.
- Check. This deals with monitoring, measuring and auditing the results of processes and procedures. It also assesses conformance with the organization's environmental policies.
- Act. This involves taking action to correct problems identified in the check stage and implement improvements.
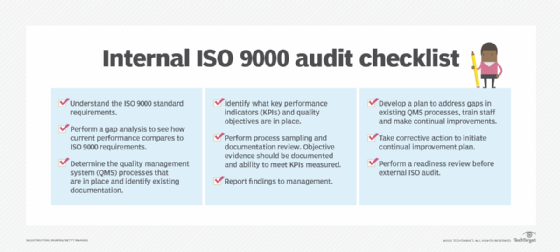
The entire process can take several months and even years depending on the size of the organization. If an organization is already ISO 9000-certified, the implementation of ISO 14001 is a shorter process. ISO 9000 is an international standard for quality management systems. For most organizations, achieving compliance with ISO 9000 is a prerequisite for launching a program for ISO 14001 compliance. Both standards provide extensive guidance on establishing management practices that address the specific subjects.
When an organization is compliant with ISO 14001, it can either register with a third-party registrar or self-declare its compliance. The ISO 14001 standard is the only ISO 14000 standard that allows an organization to register to show it's compliant.
How does an organization get certified in ISO 14001?
Accreditation with ISO 14001 is voluntary, but it's a mandatory step to demonstrate an organization's commitment to smart environmental stewardship, reduction of environmental impacts and compliance with the global standards.
The following steps help organizations prepare to launch an ISO 14001 regulatory certification initiative:
- If not already ISO 9000-certified, start that process.
- Obtain and study the ISO 14001 standard and ISO 14004:2016 Environmental management systems -- General guidelines on implementation.
- Arrange for training on ISO 14001 to prepare for the accreditation process.
- Contract with an authorized third-party auditor to do an environmental performance evaluation and authorize awarding of the ISO certificate of compliance with ISO.
The process to obtain ISO 14001 certification includes the following steps:
- Secure approval and funding from top management to launch an ISO 14001 compliance and certification project.
- Select a team to support the project.
- Launch the project with a project plan, schedule, scope and objectives.
- Use ISO 14001 and 14004 to perform a gap analysis of existing environmental management activities and environmental issues.
- Based on the gap assessment, identify areas of potential noncompliance.
- Launch corrective action in areas of noncompliance, and document those efforts.
- When satisfied that the areas of noncompliance have been remediated, schedule an audit with the third-party environmental auditing organization.
- Submit all relevant documentation, such as gap assessment results, remediation efforts and results, and policies and procedures to the auditor.
- Review the auditor's findings.
- Initiate actions to resolve any nonconformance auditors identify.
- Present a report to auditors noting remediation efforts and associated evidence.
- Assuming the outcome is positive, the certifying organization coordinates with ISO and awards the certificate of accreditation in ISO 14001.
Find out how to get your organization ready for ISO 9001 certification.
