ISO date format
What is ISO date format?
The International Organization for Standardization (ISO) date and time Format is a standard way to express a numeric calendar date -- and optionally time -- in a format that eliminates ambiguity between entities. The format, defined in the ISO 8601 standard, is used extensively by applications and machines to exchange date and time data without the uncertainly that comes when trying to communicate this data across international boundaries, diverse cultures or different time zones.
For example, North Americans usually write the month before the date, as in March 30, 2021 or 3/30/2021. However, Europeans typically write the date before the month, as in 30 March 2021 or 30.3.2021. Even the separators between the numbers can vary. ISO 8601 provides an international standard that eliminates this type of confusion.
Date representations in ISO 8601 are based on the Gregorian calendar, which replaced the Julian calendar in 1582 to better accommodate the seasonal cycles. The ISO standard also considers leap years. Additionally, it is based on a 24-hour clock (sometimes referred to as military time), and it accommodates varying time zones and how they differ from Coordinated Universal Time (UTC).
The ISO standard takes a general-to-specific approach for its date formats: The year comes first, followed by the month and then by the day of the month, with most elements represented as numerical values. For example, the ISO representation for July 15, 2022 is either 20220715 or 2022-07-15. The second example represents the extended format, which is part of the ISO extensions introduced in 2019.
The ISO standard takes a similar approach for time. The hour comes first, then the minutes, and finally the seconds. For instance, the time 5:37 p.m. and 9 seconds is represented in the ISO format as T173709 or T17:37:09. The T character is a designator that precedes the time value. When the date and time are provided together, the designator also acts as a separator. Additionally, a time value can use colons to separate elements, which are also part of the 2019 extensions.
Working with ISO date values
ISO 8601 defines multiple formats for expressing date values. The formats use specific characters to represent the date components. The table in Figure 1 describes how these characters are used and shows their acceptable range of values.
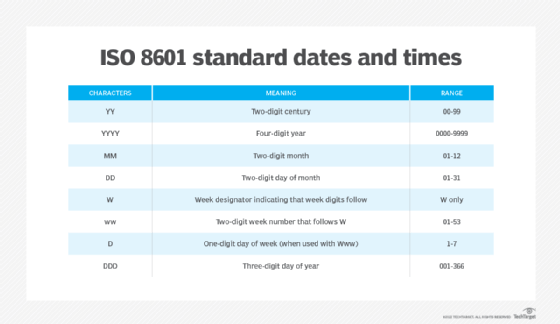
The date formats use the characters in different combinations to represent specific time frames, but they operate within strictly defined limits. For example, the ISO standard defines the year format as YYYY, the year/month format as YYYY-MM, and the year/month/day format as either YYYYMMDD (basic format) or YYYY-MM-DD (extended format). However, the standard does not permit MMDDYYYY, MMYYYYDD or any other unapproved combination to eliminate any confusion.
The standard also limits which date elements can stand alone. For instance, century (YY) and year (YYYY) can be used by themselves, but not month (MM), day of month (DD), or any of the other date characters. Month must be used with year, and day must be used with month. In addition, week (Www) must be used with year, and day of week (D) must be used with week. There are also several other considerations about the week and day to note:
- The first week in the year is the calendar week that includes the first Thursday of that year.
- The last week of the year immediately precedes the first week of the next year.
- When day (D) is specified with week (Www), the numbering starts with Monday. For example, Monday equals 1, Tuesday equals 2, and so on.
The ordinal day of year (DDD) must also be used with a year value. The table in Figure 2 shows the acceptable combination of date characters described in the previous table, along with an example of each one.
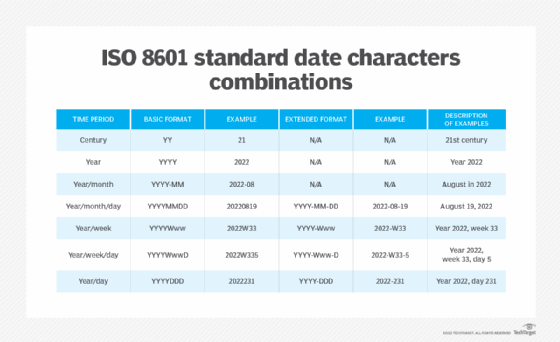
There are no extended formats for century, year or year/month, but there are for the other formats. Additionally, all formats -- basic and extended -- must include the exact number of digits specified by the ISO standard. For example, April 6, 2022 should be specified as 20220406 or 2022-04-06, rather than 202246 or 2022-4-6.
Working with ISO time values
A time value is typically preceded by the T designator. The T can be omitted if there is no risk of confusing the time with the date. However, it should be omitted only if agreed upon by both partners of the communication exchange. Note that the characters used for seconds (ss) include 00 -- 60 in their range, rather than 00 -- 59. This is done to incorporate leap seconds.
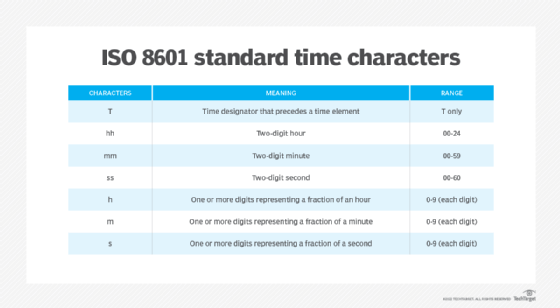
The fraction characters for hours, minutes and seconds (h, m and s) can be one or more digits. If used with hours, the time value cannot include minutes (mm) or seconds (ss). If used with minutes, the time value cannot include seconds. However, either a comma or a period can be used to separate a fraction from its root time segment. For example, the time 6:11 a.m. and 54.17 seconds can be represented as T061154,17, T06:11:54,17, T061154.17 or T06:11:54.17.
As with the date formats, the ISO standard limits which time elements can stand alone. In this case, only the hour format (hh) can be specified by itself. Minutes (mm) must be used with hours, and seconds (ss) must be used with minutes. Additionally, the character combinations must conform to the ISO specification, just like with dates. For example, ss:mm:hh or some other unapproved mix cannot be used.
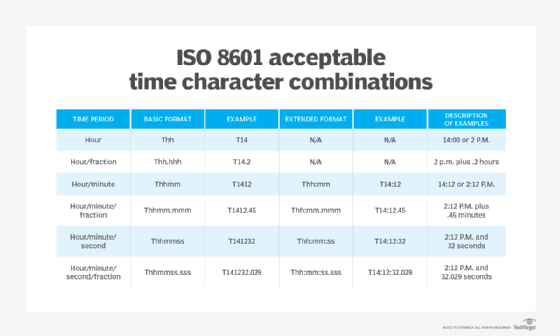
There are no extended formats for hour or hour/fraction, but there are for the other formats. As with date values, all time values must include the exact number of digits specified by the ISO standard. For example, 4:08 a.m. and 6 seconds must be specified as T040806 or T04:08:06, not T486 or T4:8:6. The only exception to this is the fractional time periods. In the table, they're represented as three digits, but they can be any agreed-upon number of digits.
The beginning of the day is expressed as either T000000 or T00:00:00, and the end of the day is expressed as either T240000 or T24:00:00. This means that the end of one calendar day (T24:00:00) coincides with the start of the next calendar day (T00:00:00). The shorter formats can also be used for these values, such as T00:00 and T24:00.
Working across time zones
The ISO 8601 standard also provides for time zone differences, as they relate to UTC. Time zone information is tagged onto the end of a time value. A time can be specified as being the same as UTC or as being ahead or behind it. When ahead or behind, the time difference must be expressed in hours or in hours and minutes. The table in Figure 5 shows how to add time zone information to time values. It also provides examples of the different formats.
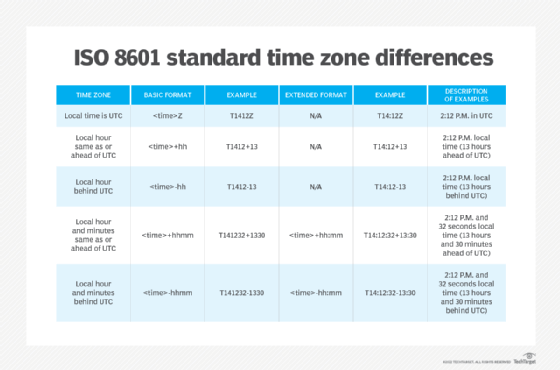
The <time> placeholder represents a valid time value, which can include any of the approved ISO time formats. The Z designator indicates that the time zone is UTC and needs only to be tagged onto the time value.
If a local time zone is the same or ahead of UTC, a plus sign should be added after the time value, followed by the number of hours or number of hours and minutes. If a local time zone is behind UTC, a minus sign should be added after the time value, followed by the number of hours or number of hours and minutes. The minutes should be omitted only if the time difference is exactly an integral number of hours.
See also: Julian date
