IT asset disposition (ITAD)
What is IT asset disposition (ITAD)?
IT asset disposition (ITAD) is an industry term and practice built around reusing, recycling, repurposing, repairing or disposing of unwanted IT equipment in a safe and environmentally responsible way. An IT organization can practice IT asset disposition itself or have a specialized vendor handle it.
Instead of ending up as electronic waste, or e-waste, in a landfill, an IT device's internal components can be reused. This helps keep waste such as plastics and heavy metals out of the environment.
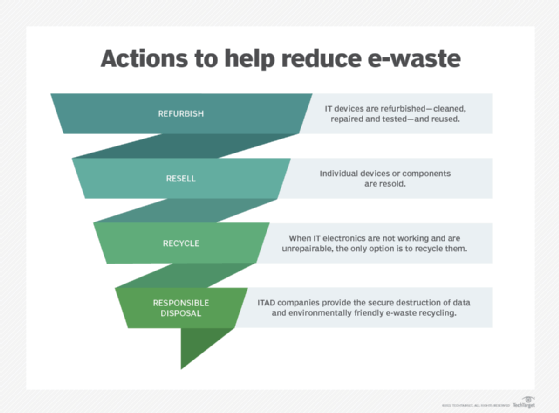
Although many businesses have a systematic replacement cycle for electronic equipment, enterprises with worn-out hardware must decide whether to refurbish, resell, recycle or dispose of their business equipment. When done internally, parts of the IT asset disposition process are often handled by IT asset management, procurement or risk management teams. An organization can also work with external businesses that focus specifically on ITAD. These companies typically provide the secure destruction of data and environmentally friendly e-waste recycling. ITAD vendors specialize in the process of streamlining the disposition of IT assets for their clients, while minimizing costs and potentially reclaiming equipment value.
What does ITAD do?
IT asset disposition focuses on the following:
- Securing data. Old hardware may still contain data, so ITAD providers follow best practices for thorough data deletion. Storage devices are securely wiped.
- Recycling and reusing devices. ITAD providers dispose of numerous types of used hardware, including desktops, laptops, servers, phones and tablets. Items such as RAM sticks or video cards can be harvested and reused in other products or recycled.
- Repairing hardware. ITAD services may also offer repair options for hardware so organizations can repurpose their equipment.
IT asset disposition companies can help organizations get rid of their excess IT equipment. They buy unneeded hardware from IT organizations and then attempt to recoup value from that hardware.
IT asset disposition vendors typically provide the following services:
- asset management
- data center decommissioning
- data erasure
- Hard drive shredding
- refurbishing
- repair and return
Why is IT asset disposition important?
Organizations quickly cycle through IT, making IT asset disposal a larger and more urgent issue when considering e-waste. These devices may contain heavy metals, chemicals and other materials that could be harmful to the environment when disposed of in a landfill. These materials could leak into the ground and affect water sources, for example. To ensure the proper and secure disposal of e-waste, ITAD providers use certified recyclers.
ITAD is also important when considering data security. For example, data breaches could occur if the data in a hard drive is not properly deleted when disposed of. ITAD providers ensure complete data erasure by physically destroying the hardware or by degaussing. Degaussing electronically removes the magnetic field of a disk or hard drive using a special device, rendering it unusable. These are both secure ways of ensuring total data deletion.
ITAD also enables IT organizations to save money, as they buy the IT equipment from their customers and refurbish their old equipment.
What is the ITAD market?
The IT asset disposition market is a secondary IT market for ITAD businesses that remarket the hardware they purchase. Within the market, different ITAD companies may coordinate with one another to sell equipment. IT organizations may also directly contact ITAD companies.
One of the most well-known entries into the ITAD market was Arrow ITAD, which has since exited the asset disposition business. Other examples are Ingram Micro Services, ITRenew, Transpere and Sipi Asset Recovery.
ITAD services that handle the process of fully and securely wiping data are a part of what made ITAD popular, as small and medium-sized businesses may use an ITAD service to handle data deletion processes for them. Rising concerns for the environment have also contributed to ITAD's success.
A market study from research firm Global Industry Analysts Inc. titled "IT Asset Disposition (ITAD) Global Market Trajectory & Analytics" estimated the global market for ITAD in 2020 was estimated at $14.6 billion and the projected growth by 2026 is $24.5 billion.
The ITAD market experienced a decline in growth in 2020 and 2021 as a result of the COVID-19 pandemic. The disruption to supply chains affected the demand for ITAD services, such as asset recovery, recycling and data destruction.
How to choose an ITAD company
Which IT asset disposition company an IT organization chooses to work with should depend on certain factors, including the following:
- Certifications. ITAD businesses can earn certifications to show they follow industry standards for best practices in recycling and reusing electronics. Some examples are e-Stewards and the National Association for Information Destruction. Certifications can also build customer trust.
- Sustainability. Choose ITAD service providers that are committed to environmental sustainability. Whenever possible, they should help IT organizations repurpose, resell or recycle hardware. Potentially harmful chemicals should also be disposed of appropriately.
- Cost. ITAD services should cost less than if an organization handled hardware disposal itself.
- Guarantee of secure data. ITAD services should disclose how they erase data for data sanitization and security reasons. They should be able to guarantee full and secure data erasure.
- Repair management. ITAD businesses also ideally offer repair services so IT organizations can get the most life out of their IT equipment.
Learn how the shift to remote work during COVID-19 increased IT buying and added to the e-waste problem.
