business process automation (BPA)
What is business process automation?
Business process automation (BPA) is the use of advanced technology to complete business processes with minimal human intervention. A business process is an activity, or set of activities, used to accomplish a specific organizational goal, such as producing a product, assimilating new employees and bringing on new customers.
A business process typically spans multiple business departments, often beginning with an action. For example, in employee onboarding, the HR system could trigger a set of predefined workflow steps to send out a welcome email, configure security credentials and set up financial details in the compensation system. Automating the workflow steps in the business process typically improves the efficiency and accuracy of each step.
BPA takes advantage of a variety of advanced technology, including automation tools, process intelligence capabilities and cloud platforms. Moreover, BPA capabilities are often incorporated in popular enterprise apps such as enterprise resource planning software, human capital management systems and other tools that enforce industry best practices.
Examples of business process automation
Business processes that can be automated show up in many areas of a business, including management, operations, supply chains, HR processes and marketing. In general, good candidates for automation are high-volume tasks that are recurring, time-sensitive, involving multiple people and in need of compliance and audit trails.
Business process automation use cases include the following:
- Onboarding new employees. Integrating a new employee is an important business process that involves many low-level but meticulous tasks. They include filling out employee forms, scheduling training sessions, completing tax documents and setting up direct deposit of paychecks. Automating the process eliminates much of the paperwork, ensures all steps are completed, and keeps relevant managers and employees informed. Automating the onboarding process results in a number of benefits when it comes to recruiting and retaining employees.
- Onboarding new customers. In the financial services industry, banking, insurance and other finance companies must conduct background checks of new customers and inform the appropriate local and federal government agencies when they onboard them as part of Know Your Customer Rule 2090 requirements. BPA can help to streamline these processes by using artificial intelligence (AI) to automate many manual tasks. Faster, more automated processes also improve customer satisfaction.
- Information technology (IT) service desk support. The volume of incoming IT tickets typically outpaces the capacity of IT staff to handle them. Automation software can analyze, classify and route incoming tickets to the relevant support personnel, provide service updates to customers and alert IT workers to issues that need immediate attention for compliance reasons, among other core tasks. Advanced automated helpdesk tools incorporate AI to predict, manage and resolve common user issues.
- Marketing automation. Marketing automation software allows companies to target customers with automated marketing messages across channels, such as email, websites, social media and text messages, to generate sales leads. The technology is a segment of customer relationship management, or CRM. It's typically used by marketing departments as a way to remove repetitive tasks from staff workflows and increase overall marketing efficiency.
Benefits of business process automation
BPA drives efficiencies and standardization that, in turn, bring many business benefits, including the following:
- Increased productivity.
- Lower costs.
- Reduced human error rates.
- Greater employee satisfaction.
- Higher revenue.
- Improved customer service.
- Insight into process success and failures.
- Better auditing and compliance.
- Easy compliance management.
Replacing humans with machines to handle repetitive tasks saves time and reduces errors. To do this, businesses must carefully define the steps in their processes and subject them to limited interpretation. In addition, the process automation system must communicate any exceptions where human intervention is allowed. Workflow automation of menial tasks frees employees to do higher value work.
By centralizing a business process through automation, organizations also gain transparency into their workflows. There is BPA software that gives companies the ability to see all the process steps on one dashboard, providing visibility into the status of process activities, from task reviews to the approval process. Automation can also ensure that compliance regulations are followed.
BPA has become increasingly important as enterprises seek to become digital businesses. Digital transformation depends on process automation, which often begins with converting information into computer-readable formats that then become part of enterprise-wide automation.
Challenges of business process automation
Despite all the benefits of BPA, not every process is a good candidate for automation. BPA is best-suited to tasks that are high volume, recurring, time-sensitive and involve multiple people. Also, since automation isn't a one-and-done effort, enterprises should periodically review how automated processes are affected by changes in governance requirements, regulations, security and other factors.
Challenges businesses are likely to face with BPA include the following:
- Scaling. A business might adopt BPA tools for a specific task or set of tasks. Scaling the BPA effort to encompass other goals in the future might not be easy.
- Synchronization. When automation systems and bots share work with humans, it can be difficult to train people to work with the automation tools and provide all the needed information so the tools can operate effectively.
- Overcoming roadblocks. Often, BPA tools are adopted to expedite processes without any consideration of potential disruptions that can slow or halt the work of BPA tools.
- Insufficient documentation. BPA tools must be presented with clearly documented processes in a step-by-step format. A business lacking sufficient documentation would need to overcome this hurdle before using BPA.
How does BPA relate to RPA?
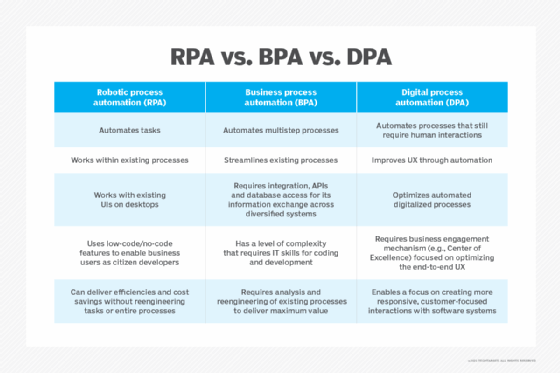
The term BPA is used to characterize a collection of automation capabilities for streamlining and improving business processes. Robotic process automation (RPA) is a subset of BPA that focuses on automating how humans use software applications at work. It's attractive to businesses because it provides a quick way to automate data entry and copy data between applications.
Using RPA software, workers and developers alike can record the rough draft for a simple automation by clicking and scrolling their way through a business process. These drafts are turned into final apps by the development team. The various RPA platforms then harden these basic programs so they can't be changed in the application layouts and workflows.
Intelligent process automation and digital process automation (DPA) combine basic RPA capabilities with AI tools to create more sophisticated automations. For example, optical character recognition can read printed text, and natural language processing can map numbers from invoices to fields in business systems. Machine vision algorithms could perform tasks like estimating insurance damages. AI and machine learning algorithms can automate other types of decisions a bot might have to make.
Low-code development platforms are another type of BPA automation tool. These tools take advantage of application programming interface (API) access rather than emulating human progress through the user interface. This lets them provide better performance than traditional RPA programs. Some of the low-code platforms, such as Microsoft's Power Automate, are starting to combine the ease of RPA programming with the speed of cloud API execution.
How does BPA relate to BPM?
BPA can be a standalone initiative or part of a larger, overarching business process management (BPM) strategy. The terms BPA and BPM are sometimes used interchangeably, but they aren't the same.
Both BPA and BPM aim to help businesses improve business processes to meet their organizational goals. However, their purviews are different. BPA focuses on how automation can simplify and streamline a business process. BPM might include automation but doesn't have to, and it employs a variety of methods to discover, model, analyze, change and optimize end-to-end business processes.
In BPM, business processes are managed collectively to reduce error rates and improve workflow efficiency. It also handles other tasks, such as clarifying job roles and responsibilities, thereby increasing the organization's capacity to adapt to changing business goals.
BPM projects often use diagramming tools such as business process modeling notation to diagram complex business processes. These diagrams are used to improve understanding of existing business processes. They may also serve as templates for implementing automation through various BPA technologies.
How does BPA relate to business process analysis?
Business process automation and business process analysis are complementary technologies, which confusingly use the same acronym. Business process analysis is a subset of business process automation. As its name denotes, it's concerned with analyzing business processes. It uses various manual processes and automated approaches to map and understand existing processes.
In the manual approach, process experts typically interview subject matter experts and business users to construct a process map. The automated approach uses various technologies that include process mining, process capture and process intelligence to do the same.
Process mining analyzes enterprise system logs to map out business processes and variations in how they are executed. Process capture -- sometimes called task mining -- uses machine vision to watch over an employee's screen to generate a map of processes that span multiple applications. Process intelligence is a newer term to describe the use of both technologies combined with business intelligence and analytics capabilities for greater automation and insight.
Recently, Gartner has begun to use the term enterprise business process analysis to characterize these more automated approaches for automatically mapping and analyzing processes.
How to automate business processes
Before beginning a BPA project, it's critical to understand how the existing process works, why it's a good candidate for automation and how it should be changed. Here are some necessary first steps:
- Analyze the enterprise's appetite for business automation. Business process automation changes how work gets done, so it requires buy-in from key stakeholders. The scope of the automation determines the level of executive commitment needed for a BPA effort. Employees need to be kept in the loop: Whether the BPA project is as straightforward as converting a paper form into electronic format and routing it to the appropriate people, or it's a transformative automation effort designed to support a new business model, employees impacted by the automation must be trained on the new workflow and should understand the business value the BPA technology provides. It's also important to communicate how the new automation could positively affect their jobs.
- Understand your processes and identify potential candidates for automation. It's hard to get to where you want to be if you don't know where you're starting from. Before deploying an automation tool, it's critical to know what the existing process involves. However, understanding existing business processes and the business rules that govern them isn't easy for many organizations.
- Scope your project based on automation maturity. Companies typically reap the largest return on BPA projects that automate complex, business-critical processes and case management. Experts advise companies with limited experience in automation to start small, homing in on recurring, rules-based tasks, such as purchase orders, where the steps are unambiguous and well understood. Various process intelligence capabilities, such as process mining and process capture, can help automate this work.
- Get input from key stakeholders on process steps to eliminate, optimize and automate. "Don't pave the cow path" is another common saying in the process automation world. The idea is that automating an existing process without first examining where it can be improved or how it should change simply speeds up existing flaws. There's debate about the wisdom of this warning, especially for companies looking for quick wins from automation. In general, BPA experts believe an existing process should be automated only after analyzing how it could be more effective and input is gathered from key stakeholders. According to software engineer James Highsmith III, a prolific writer on software development and one of the original authors of the Agile Manifesto, successful automation projects have input from multiple sources, including business analysts, development teams and IT.
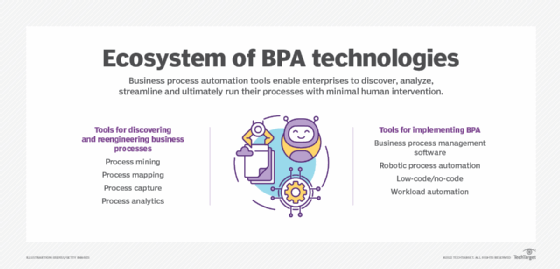
Business process automation tools and software
BPA includes a broad set of established, as well as rapidly evolving business automation technologies, including the following:
- Workflow tools geared to business users with limited coding experience.
- RPA, which creates software robots that mimic how humans interact with digital systems through the user interface.
- Intelligent automation, which uses machine learning and other AI tools to train automation models that improve over time.
- DPA, a term reflecting the linkage between BPA strategies and the larger undertaking of digital transformation.
In addition, business process management software is evolving, as leading BPM vendors in this space -- such as Appian and Pega -- add RPA, AI and low-code/no-code capabilities. These types of advanced technologies facilitate BPA strategies in various ways.
For example, giving no-code automation platforms to nondevelopers lets them automate workflows and customize apps quickly, without forcing developers or programmers to do so. This saves a company time and expense. Also, AI and machine learning systems can analyze data and look for new approaches that optimize existing workflows.
Forrester Research has replaced the term BPM with DPA-deep and DPA-wide to reflect the evolution of BPM software. The upshot of this fast-moving technology space is that companies need to establish what Forrester calls an automation framework that delineates between the various automation tools, filters out the market hype and understands how they can be used separately and in tandem to achieve business process automation.
While business process automation isn't a new idea, hyperautomation is a nascent concept associated with digital transformation. Business leaders are looking to automate as many tasks as possible so human workers can focus on innovative and forward-looking tasks.






