ITAR and EAR compliance
What is ITAR and EAR compliance?
The International Traffic in Arms Regulations (ITAR) and the Export Administration Regulations (EAR) are two important U.S. export control laws that affect the manufacturing, sales and distribution of certain technologies, technology products, software and services.
Both laws are designed to control access to specific types of technology and data to prevent the unintended disclosure or transfer of sensitive information to an unauthorized or suspicious foreign national.
The International Traffic in Arms Regulations (ITAR) explained
ITAR rules regulate the export of defense articles and services, including technological products and services and technical data. The articles and services regulated under ITAR are identified in the United States Munitions List (USML).
A broad range of defense products are covered under ITAR, including electronic items, imaging systems, satellites, body armor and spacecraft. Defense services might include the design, development, testing and maintenance of a wide range of military systems, the repair of these systems, as well as military training.
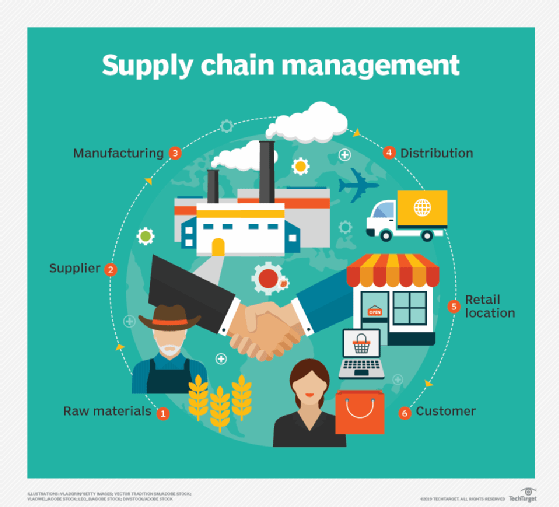
The rules apply to any entity in the United States that manufactures, exports or temporarily imports defense products or services. These entities could be any part of the supply chain, such as:
- wholesalers
- distributors
- software vendors
- vendors
- contractors
- third-party suppliers
These entities have obligation to be ITAR-compliant.
The U.S. Department of State Directorate of Defense Trade Controls (DDTC) is the governing agency for the ITAR. Its primary documentation is known as the United States Munitions List (USML).
The ITAR's USML
The USML includes many items that the DDTC deems as providing the U.S. a critical advantage in military or intelligence terms and whose unauthorized export could adversely affect the national security of the country. The list consists of 21 categories of products, such as aircraft, ground vehicles and firearms. The items in each category could be identified as software, technical data or defense services. Minor items such as spare parts, accessories components and sub-assemblies are also listed in the USML.
Note that not all defense-related items are subject to the ITAR. To avoid confusion and possible errors, entities must carefully review the USML and ascertain if ITAR compliance applies to their business and offerings.
Exports and imports under ITAR
The ITAR controls the exports of defense services and products, reexports and temporary exports, and temporary imports. In other words, any entity involved in any of these activities with respect to defense services and products must be ITAR-compliant.
The term "export" is broadly defined under the ITAR. It not only refers to the export of a tangible product or service, but also to a U.S. person providing (i.e., exporting) controlled or sensitive information to a foreign person. This meaning applies even if this transfer occurs within the same company located in the U.S.
The Export Administration Regulations (EAR) explained
Many defense products and services that are not subject to the ITAR might be subject to the EAR. These regulations control commercial goods and dual-use items (items that can be used both for commercial and military purposes) that are not on the ITAR's USML or other export control lists. The EAR controls many types of military hardware, including:
- munitions
- firearms
- aircraft
- military vehicles
- materials
- chemicals
However, many military items might fall outside the ITAR's or the EAR's jurisdiction but are subject to control by other federal agencies, such as the FDA, USDA, and so on.
The governing agency for the EAR is the U.S. Department of Commerce's Bureau of Industry and Security (BIS), and its primary documentation is the Commerce Control List (CCL). The BIS oversees the EAR's jurisdiction, licensing, policy setting and the enforcement of EAR regulations.
What is EAR's Commerce Control List (CCL)?
The CCL is a list of regulated commercial items, including those items that have both commercial and military applications. It includes 10 categories and five product groups. Each item that falls under the purview of the EAR is assigned an Export Control Classification Number (ECCN).
Vendors must properly classify their items with the correct ECCN instead of assigning it the catch-all category of EAR99. Proper classification ensures that the user fulfills EAR requirements and maintains compliance with its rules.
Licensing applications under ITAR and EAR
The ITAR requires vendors to submit an export license application through the DDTC's DTrade electronic licensing system. This system enables U.S. citizens and certain foreign individuals to submit license applications that allow them to export or temporarily import defense articles as per the rules specified in the ITAR.
Similarly, under the EAR, U.S. exporters of defense or dual-use items must submit export license applications through the BIS' SNAP-R online systems. Through SNAP-R, users can also submit commodity classification requests and reexport license applications. To access the system, they must have a Company Identification Number (CIN) and create an active user account.
What are the differences between ITAR and EAR?
The ITAR regulates the manufacture, sale, distribution and export of defense-related articles and services, whereas the EAR regulates the manufacture, sale, distribution and export of commercial and dual-use items, technology and information not already covered by ITAR. The dual-use items covered under the EAR have both commercial and military applications. The EAR also covers items that are purely for commercial use.
The ITAR is regulated and enforced by the U.S. Department of State, while the EAR is regulated and enforced by the U.S. Department of Commerce. Exporters who fall under the purview of the ITAR or EAR must check the relevant documents. For the ITAR, the chief document is the United States Munitions List, while for the EAR, the main document is the Commerce Control List.
Despite these differences, the ITAR and EAR have a common goal: to protect U.S. national security and foreign policy interests by preventing the unauthorized export of controlled/defense items to foreign persons.
Complying with ITAR and EAR
To be ITAR or EAR compliant, a manufacturer or exporter whose articles or services appear on the USML or CCL lists must register with DDTC. Any company or individual involved in the export or temporary import of defense articles, arms brokering or providing defense services must get DDTC authorization. It might be necessary to obtain a Commodity Jurisdiction (CJ) from the DDTC to understand which regulation applies. Working with an outside consultant can facilitate the process.
ITAR and EAR compliance can be problematic for a global corporation because the data related to a specific type of technology might need to be transferred over the internet or stored locally outside the U.S. to make business processes flow smoothly. It is the responsibility of the manufacturer or exporter to take the necessary steps to certify that they comply with the regulations.
