password cracking
What is password cracking?
Password cracking is the process of using an application program to identify an unknown or forgotten password to a computer or network resource. It can also be used to help a threat actor obtain unauthorized access to resources.
With the information malicious actors gain using password cracking, they can undertake a range of criminal activities. Those include stealing banking credentials or using the information for identity theft and fraud.
A password cracker recovers passwords using various techniques. The process can involve comparing a list of words to guess passwords or the use of an algorithm to repeatedly guess the password.
How do you create a strong password?
Password crackers can decipher passwords in a matter of days or hours, depending on how weak or strong the password is. To make a password stronger and more difficult to uncover, a plaintext password should adhere to the following rules:
- Be at least 12 characters long. The shorter a password is, the easier and faster it will be cracked.
- Combine letters and a variety of characters. Using numbers and special characters, such as periods and commas, increases the number of possible combinations.
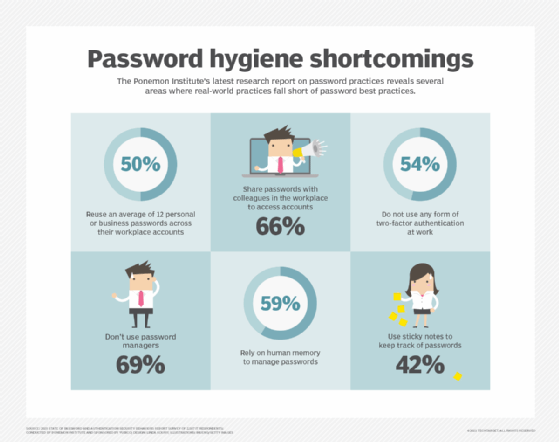
- Avoid reusing a password. If a password is cracked, then a person with malicious intent could use that same password to easily access other password-protected accounts the victim owns.
- Pay attention to password strength indicators. Some password-protected systems include a password strength meter, which is a scale that tells users when they have created a strong password.
- Avoid easy-to-guess phrases and common passwords. Weak passwords can be a name, a pet's name or a birthdate -- something personally identifiable. Short and easily predictable patterns, like 123456, password or qwerty, also are weak passwords.
- Use encryption. Passwords stored in a database should be encrypted.
- Take advantage of password creation tools and managers. Some smartphones will automatically create long, hard-to-guess passwords. For example, Apple iPhones will create strong website passwords for users. An iPhone stores the passwords in its password manager, iCloud Keychain and automatically fills the password into the correct field so the user doesn't have to remember the complicated password.
What does a password cracking attack look like?
The general process a password cracker follows involves these four steps:
- Steal a password via some nefarious means. That password has likely been encrypted before being stored using a hash Hashes are mathematical functions that change arbitrary-length inputs into an encrypted fixed-length output.
- Choose a cracking methodology, such as a brute-force or dictionary attack, and select a cracking tool.
- Prepare the password hashes for the cracking program. This is done by providing an input to the hash function to create a hash that can be authenticated.
- Run the cracking tool.
A password cracker may also be able to identify encrypted passwords. After retrieving the password from the computer's memory, the program may be able to decrypt it. Or, by using the same algorithm as the system program, the password cracker creates an encrypted version of the password that matches the original.
What are password cracking techniques?
Password crackers use two primary methods to identify correct passwords: brute-force and dictionary attacks. However, there are plenty of other password cracking methods, including the following:
- Brute force. This attack runs through combinations of characters of a predetermined length until it finds the combination that matches the password.
- Dictionary search. Here, a password cracker searches each word in the dictionary for the correct password. Password dictionaries exist for a variety of topics and combinations of topics, including politics, movies and music groups.
- Phishing. These attacks are used to gain access to user passwords without the use of a password cracking tool. Instead, a user is fooled into clicking on an email attachment. From here, the attachment could install malware or prompt the user to use their email to sign into a false version of a website, revealing their password.
- Malware. Similar to phishing, using malware is another method of gaining unauthored access to passwords without the use of a password cracking tool. Malware such as keyloggers, which track keystrokes, or screen scrapers, which take screenshots, are used instead.
- Rainbow attack. This approach involves using different words from the original password in order to generate other possible passwords. Malicious actors can keep a list called a rainbow table with them. This list contains leaked and previously cracked passwords, which will make the overall password cracking method more effective.
- Guessing. An attacker may be able to guess a password without the use of tools. If the threat actor has enough information about the victim or the victim is using a common enough password, they may be able to come up with the correct characters.
Some password cracking programs may use hybrid attack methodologies where they search for combinations of dictionary entries and numbers or special characters. For example, a password cracker may search for ants01, ants02, ants03, etc. This can be helpful when users have been advised to include a number in their password.
Learn about emerging passwordless authentication options
Passwordless authentication options and best practices
Okta competing with Microsoft, Google and others in passwordless offerings
When will we finally ditch passwords? Here's Microsoft's 4-step plan
How to go passwordless if not all your apps support modern authentication standards
What are password cracking tools?
Password crackers can be used maliciously or legitimately to recover lost passwords. Among the password cracking tools available are the following three:
- Cain and Abel. This password recovery software can recover passwords for Microsoft Windows user accounts and Microsoft Access passwords. Cain and Abel uses a graphical user interface, making it more user-friendly than comparable tools. The software uses dictionary lists and brute-force attack methods.
- Ophcrack. This password cracker uses rainbow tables and brute-force attacks to crack passwords. It runs on Windows, macOS and Linux.
- John the Ripper. This tool uses a dictionary list approach and is available primarily for macOS and Linux systems. The program has a command prompt to crack passwords, making it more difficult to use than software like Cain and Abel.
Is password cracking illegal?
The legality of password cracking may change based on location. In general, it depends on intent. For example, using a password cracking tool to retrieve one's own password may be fine. However, in most cases, if the goal is to maliciously steal, damage or misuse someone else's data, it will most likely be an illegal action.
Unauthorized access to another individual's device can be grounds for criminal charges. Even guessing someone's password without the use of a password cracker can lead to criminal charges. Under U.S. state and federal laws, more charges can be added depending on what threat actors do once they gain unauthorized access.
In short, using a password cracking method to access one's own password is legal. Using these methods or tools to gain access to someone else's password can lead to criminal charges.
Learn about why security professionals recommend having an effective identity and access management system in place and how employee training fits into a good password and overall cybersecurity strategy.






