TCO (total cost of ownership)
What is TCO (total cost of ownership)?
Total cost of ownership (TCO) is an estimation of the expenses associated with purchasing, deploying, using and retiring a product or piece of equipment.
TCO, or actual cost, quantifies the cost of the purchase across the product's entire lifecycle. Therefore, it offers a more accurate basis for determining the value -- cost vs. return on investment (ROI) -- of an investment than the purchase price alone.
TCO can be calculated as the initial purchase price plus costs of operation across the asset lifespan.

What factors determine TCO?
The overall TCO includes direct and indirect expenses, as well as some intangible ones that may be assigned a monetary value.
For example, a server's TCO might include an expensive purchase price, but indirect costs could include a good deal on ongoing information technology support, and low system management time because of its user-friendly interface.
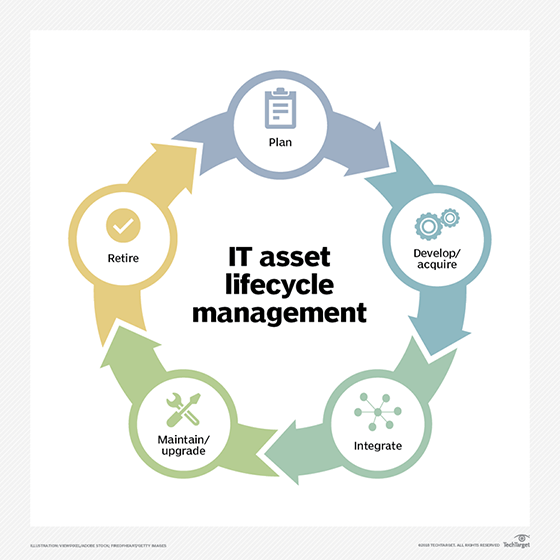
TCO factors in costs accumulated from purchase to decommissioning.
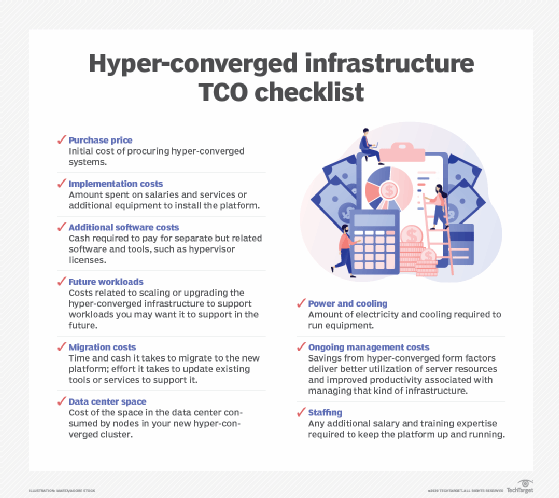
For a data center server, for example, this means initial acquisition price, repairs, maintenance costs, upgrades, service or support contracts, network integration, security, software licenses and employee training.
It can even include the credit terms on which the company purchased the product. Through analysis, the purchasing manager might assign a monetary value to intangible costs, such as systems management time, electricity used, downtime, insurance and other overhead.
The total cost of ownership must be compared to the total benefits of ownership (TBO) to determine the viability of a purchase.
The challenges with calculating TCO
There are several methodologies and software tools to calculate the total cost of ownership, but the process is not perfect. Many enterprises fail to define a singular methodology. This is bad because they cannot base purchasing decisions on uniform information.
Another problem is that it is difficult to determine the scope of operating costs for any piece of IT equipment; some hidden cost factors are easily overlooked -- such as depreciation and warranty -- or inaccurately compared from one product to another.
For example, support costs on one server include the cost of spare parts. This might make support cost more than it does on another server but eliminates acquisition costs.
Cost of ownership analysis generally doesn't anticipate unpredictable rising costs over time -- for example, if upgrade part costs jump substantially more than expected due to a distributor change.
TCO calculations cannot account for the availability of upgrades and services or the impact of vendor relationships.
If a software vendor cancels a particular functionality after three years, no longer stocks parts after five years, or ends support for certain software, the business may be subject to unexpected and significant additional costs which could drive the TCO far beyond its initial estimate.
Best practices to optimize TCO calculations
Enterprise managers and purchasing decision-makers complete cost analysis for multiple options, then compare TCOs to determine overall costs and, ultimately, the lowest long-term cost.
For example, one server's purchase price or license fees might be less expensive than a competitive model, but those tasked with decision-making can see that anticipated upgrades and annual service contracts would significantly reduce any perceived cost savings.
In turn, one model's TCO may be slightly higher than another model's, but it's TBO incentives far exceed that of the competitive offering.
Without TCO analysis, enterprises could greatly miscalculate IT budgets, or purchase servers and other components unsuited to their computing needs, resulting in slow services, uncontrolled downtime and other problems.






