Lightning (Salesforce Lightning)
What is Lightning in Salesforce?
Lightning (Salesforce Lightning) is a component-based framework for Salesforce app development. Salesforce Lightning aims to simplify the Salesforce app development processes for business users, who typically do not have programming experience.
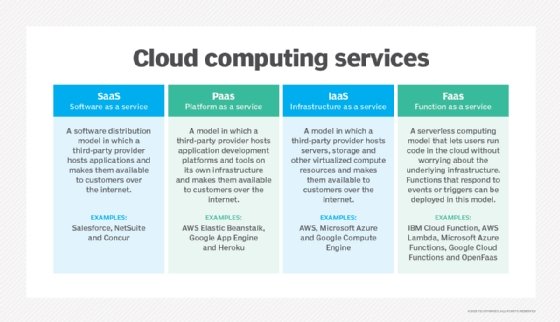
Salesforce overview
Salesforce is a cloud computing and social enterprise software as a service (SaaS) provider. The company was founded in March 1999 and is based in San Francisco.
Salesforce Lightning comprises a collection of tools and technologies behind a significant upgrade to the Salesforce1 Platform (now known as App Cloud), the company's mobile app development platform (MADP).
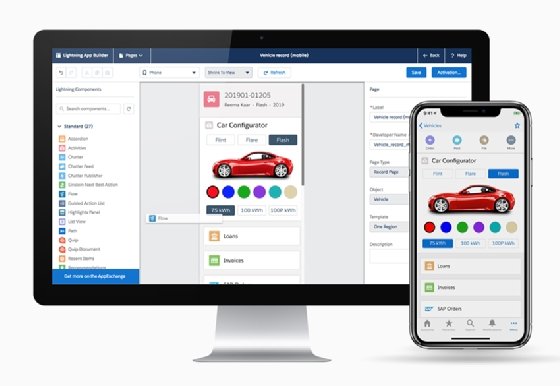
Lightning features the Lightning Component Framework and some Salesforce application development tools. These tools help developers build mobile apps with advanced Salesforce Lightning page layouts.
Salesforce Lighting features
Here are some key Salesforce Lightning features:
- Experience Builder is a graphical user interface (GUI) optimized for speed. Administrators can build robust communities using Lightning templates and components following a visual no-code development approach.
- Lightning App Builderfollows a no-code development approach providing drag-and-drop capabilities to facilitate app creation and customization.
- Lightning Component Framework includes tools and extensions that enable the development of reusable components and standalone apps and Salesforce Mobile App customizations.
- AppExchange makes over 300 partner components available in the App Builder.
- Design System offers style guides and user experience (UX) best practices for app development.
- Lightning Connect is an integration tool that makes it easier for Salesforce apps to consume data from any external source that conforms to the Open Data Protocol (OData)
Lightning developers can also build custom reusable components that other administrators and developers can incorporate into their Lightning Experience and Salesforce mobile apps.
Businesses can accelerate development and enhance app performance by seamlessly customizing and deploying Salesforce Lightning components. Even Salesforce Lightning Experience and the Salesforce mobile app were built using the Salesforce Lightning design system and components.
Salesforce Lightning Experience
Salesforce Lightning Experience is a modern, capable user interface (UI) that empowers sales representatives and service representatives to sell more faster and support customers more efficiently.
Salesforce Lightning vs. Classic
Salesforce veterans familiar with Salesforce Classic know that it does not come with Lightning features like a modern interface, activity timeline, Einstein opportunity insights and regular updates. The two features common to both Lightning and Classic are comprehensive sales data and Einstein forecasting.
Although Salesforce Classic is still available and is supported for current users, new users are taken straight to Salesforce Lightning.
Here are the primary Salesforce Lightning benefits:
- The activity timeline helps track the activity and history of each account or sales lead.
- The artificial intelligence (AI) integration uses advanced protocols for lead scoring, opportunity scoring, and support for marketing resource assignment for the right customers or direct customer support.
- Expanded forecasting includes features like forecast sharing, revenue and quantity forecasts, territory forecasts, product and schedule date forecasts, and other customizable forecasts.
- There is greater security, with an additional security layer between the components and stronger authentication
- A comprehensive homepage features news, key deals, events, calendars, performance charts and customizable dashboards.
- Mobile optimization ensures optimal responsiveness across mobile devices and browsers.
- Workspace page layout lets users customize and design new types of pages.
Salesforce Field Service Lightning
Salesforce Field Service Lightning (FSL) helps connect products, customers and the workforce to a single platform to provide efficient on-site services. Teams can also offer enhanced customer support -- a primary purpose of any customer relationship management (CRM) system like Salesforce -- by intelligently delegating work to field service technicians and continuously monitoring them.