Luddite
What is a Luddite?
A Luddite is a person resistant to increased industrialization or new technologies, especially computers.
History of the term Luddite
The term Luddite originated in the early 19th century during a period of great social and economic change in England. At the time, many workers feared that the introduction of new machines would lead to widespread unemployment, as machines could perform tasks more efficiently and cheaply than humans.
In response, a group of workers began to destroy the new machinery in the belief that this would protect their jobs. These workers became known as the Luddites, drawing their name from the mythical figure Ned Ludd, who was said to have destroyed his own loom in protest.
Modern applications for the term Luddite
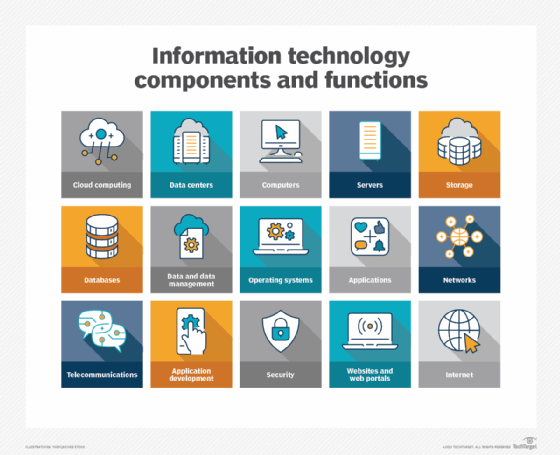
Today, the term Luddite is often used to refer to anyone who is opposed to new technology, particularly in the field of IT.
Luddites may view technology as a threat to traditional ways of life, or they may be concerned about the negative impacts that technology can have on society, such as the erosion of privacy or the concentration of wealth and power in the hands of a few tech companies.
Examples of Luddite perspective on technology
There are several arguments that Luddites might make against technology. For example, some might argue that technology leads to the dehumanization of work, as machines and algorithms increasingly replace human labor.
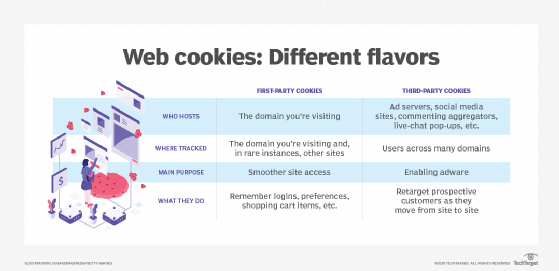
Others might point out that technology can be used to exploit and oppress vulnerable groups, such as through the use of surveillance or targeted advertising -- for example, using cookies to track a user's online behavior to target specific ads and marketing their way. Still others might argue that technology is fundamentally changing the way we think and interact with the world, in ways that are hard to predict and potentially harmful.
Other perspectives on technology
Despite these concerns, it is worth noting that technology has brought many benefits to society. For example, advances in IT have led to the creation of new industries and job opportunities and have made it easier for people to communicate and collaborate with one another.
Technology has also played a crucial role in improving public health through the development of new medical treatments and the ability to share information about health threats more quickly and efficiently.
Ultimately, the debate over the role of technology in society is likely to continue, and it is up to individuals and communities to decide how to balance the potential benefits of new technologies.
Learn about balancing the benefits with the risks of emerging technology, and explore the importance of culture in digital transformation.
